/ What Is a Cloud Native Application Protection Platform (CNAPP)?
What Is a Cloud Native Application Protection Platform (CNAPP)?
A cloud native application protection platform (CNAPP) is a security and compliance solution that helps teams build, deploy, and run secure cloud native applications in today’s heavily automated, dynamic public cloud environments. CNAPPs also help security teams collaborate more effectively with developers and DevOps. CNAPP comprises a new category of cloud security platform, consolidating CSPM, CIEM, IAM, CWPP, data protection, and other capabilities.
Why Is CNAPP Important?
Traditional security tools and approaches and tools were designed to protect on-premises data centers and endpoints, not cloud native apps and services. With the shift to cloud native technologies, dynamic and ephemeral environments with strong automation, faster release cycles, and modern development practices (e.g., infrastructure as code [IaC], CI/CD pipelines, containers, serverless functions, Kubernetes), those tools fall short.
Changes occur frequently in the public cloud, and the security team needs to handle security and compliance—ideally without slowing the whole organization down. To do that, they need to identify security issues and vulnerabilities early in development, speed up remediation, and provide continuous, consistent security and assurance. Unfortunately, accomplishing all that amid the many interdependencies in modern environments can be quite difficult with a traditional approach.
To optimize cloud security and compliance to support DevOps and minimize friction, security teams need to evolve from protecting infrastructure to protecting applications that run on workloads. That means ensuring the security of cloud service configurations and the production environment at a minimum, with runtime protection a valuable layer of additional protection.
Key Components Of CNAPP
An effective CNAPP helps security teams correlate intel across a wide range of signals into a single view to identify and prioritize the organization’s biggest risks, bringing together:
- Cloud security posture management (CSPM) to monitor, identify, alert on, and remediate compliance risks and misconfigurations in cloud environments
- Infrastructure as code security to detect misconfigurations in code early in the software development life cycle to prevent vulnerabilities at runtime
- Compliance and governance to manage compliance status as well as remediate configuration drift and policy violations across multicloud environments
- Cloud infrastructure entitlement management (CIEM) to mitigate the risk of data breaches in public clouds by continuously monitoring permissions and activities
- Data protection to monitor, classify, and inspect data and prevent exfiltration of critical data as a result of phishing, malicious insiders, or other cyberthreats
- Identity and access management (IAM) to control access to internal resources, ensuring users’ permissions grant them appropriate access to systems and data
- Cloud workload protection platforms (CWPP) to provide visibility and control for physical machines, VMs, containers, and serverless workloads in hybrid, multicloud, and data center environments
Challenges of a Legacy Approach
As organizations grow, they tend to end up with a mixture of technologies, with disparate security controls in various cloud environments. Security teams deploy CSPM, CIEM, CWPP, and other tools to secure cloud infrastructure and production environments. This approach leaves them unable to effectively focus, prioritize, and remediate risk, thanks to:
- Visibility gaps and security blind spots
- Multiple sources of data points, with no single source of truth
- Information overflow and time-consuming data correlation processes
- Alert fatigue with no indication of critical issues that need attention
- Limited resources, technical expertise, and training on each tool
- High operational complexity and overhead from managing each tool separately
Trying to maintain proper controls using disparate tools across complex environments takes a lot of time, resources, and manual effort—and often, it’s just not enough to keep up.
Benefits of CNAPP
As a unified security solution, a CNAPP offers complete security coverage to help you keep up with ephemeral, containerized, and serverless environments, providing:
- A single pane of glass, improving team collaboration and efficiency by identifying and correlating minor issues, individual events, and hidden attack vectors into intuitive visual flows with alerts, recommendations, and remediation guidance to support informed decisions.
- Reduced complexity and overhead, replacing multiple point products with a complete picture of risk via comprehensive visibility into configurations, assets, permissions, code, and workloads. A CNAPP analyzes millions of attributes to prioritize the most critical risks.
- Comprehensive cloud and services coverage, with visibility and insights across your entire multicloud footprint, including IaaS and PaaS, extending across VM, container, and serverless workloads and into dev environments, to identify and remediate risks early.
- Security at the speed of DevOps, integrating with IDE platforms to identify misconfigurations or compliance issues during development and CI/CD, as well as with SecOps ecosystems to trigger alerts, tickets, and workflows on violations so teams can act immediately.
- Guardrails to distribute security responsibility, injecting security controls at each level of the DevOps cycle, with native integrations into existing development and DevOps tools. Implementing guardrails enables developers to take ownership of security in their work, reducing friction between security and the DevOps team to better support DevSecOps.
How Does CNAPP Work?
CNAPP platforms bring together multiple security tools and functions to reduce complexity and overhead, providing:
- The combined capabilities of CSPM, CIEM, and CWPP tools
- Correlation of vulnerabilities, context, and relationships across the development life cycle
- Identification of high-priority risks with rich context
- Guided and automated remediation to fix vulnerabilities and misconfigurations
- Guardrails to prevent unauthorized architecture changes
- Easy integration with SecOps ecosystems to send alerts in near-real time
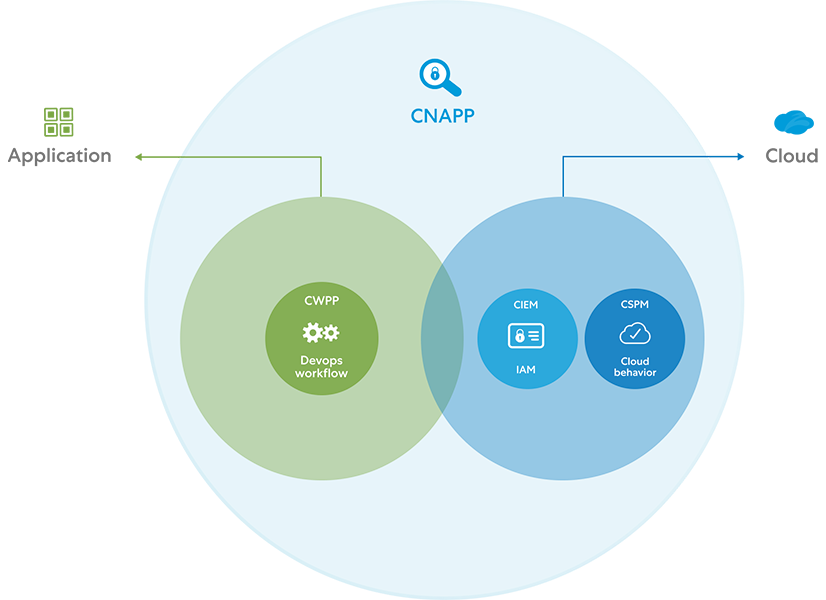
What CNAPP encompasses (Image adapted from "How to Protect Your Clouds with CSPM, CWPP, CNAPP, and CASB," Gartner, May 6, 2021)
Key Capabilities of a CNAPP
As a convergence of so many security and compliance tools, CNAPPs have dozens of specific capabilities. Let's look at the broader strokes of what a CNAPP enables your organization to do.
Secure Multicloud Infrastructure
Discover all apps, APIs, cloud resources, identities, and sensitive data. Gain complete visibility of compliant and noncompliant resources across AWS, Azure, and Google Cloud, and prioritize them for remediation based on risk.
Secure Production Environment
Move security earlier in the development process (i.e., "shift left"). Empower your DevOps professionals to detect threats and vulnerabilities sooner, and fix them faster, to ensure applications and data are compliant.
Secure Workloads
More easily detect and manage vulnerabilities and security misconfigurations as well as perform network-based behavioral monitoring, policy enforcement, and identity-based cloud workload segmentation.
Continuous Governance and Compliance
Minimize audit fatigue with automated security controls for continuous compliance and governance of data, configurations, and permissions.
Team Collaboration Platform
Incorporate common workflows, data correlation, meaningful insights, and remediation to reduce friction and foster team collaboration between DevSecOps, DevOps, and cloud security operations.
Gartner Recommendations Around CNAPP
In "Innovation Insight for Cloud-Native Application Protection Platforms," Gartner offers this advice: “Rather than treat development and runtime as separate problems — secured and scanned with a collection of separate tools — enterprises should treat security and compliance as a continuum across development and operations, and seek to consolidate tools where possible.”
Key recommendations include:
- Implement an integrated security approach that covers the entire life cycle of cloud native applications, starting in development and extending into production
- Scan development artifacts and cloud configuration comprehensively, and combine this with runtime visibility and configuration awareness to prioritize risk remediation
- Evaluate emerging CNAPP offerings as contracts for CSPM and CWPP expire, and use this opportunity to reduce complexity and consolidate vendors
Zscaler and CNAPP
Posture Control™ by Zscaler is a high-performance CNAPP that takes a radically new approach to cloud native application security with a 100% agentless solution that correlates across multiple security engines to prioritize hidden risks caused by misconfigurations, threats, and vulnerabilities across the entire cloud stack, reducing cost, complexity, and cross-team friction.
We built our unified platform from the ground up to prioritize infrastructure and application security risks in distributed clouds and across the development and DevOps life cycles, enabling you to:
- Secure configurations: Maintain comprehensive CSPM controls across cloud infrastructure, resources, data, and identities. Learn more.
- Secure entitlements: Secure human and machine identities while enforcing least-privileged access. Learn more.
- Secure infrastructure as code: Shift security left with the developer and DevOps workflows to fix vulnerabilities and compliance issues. Learn more.
- Secure data: Secure confidential data across multiple cloud repositories while maintaining visibility, control, and compliance. Learn more.
- Secure workloads and applications: Leverage zero trust to agentlessly secure hosts, containers (e.g., Kubernetes) and serverless functions across the full app life cycle. Learn more.