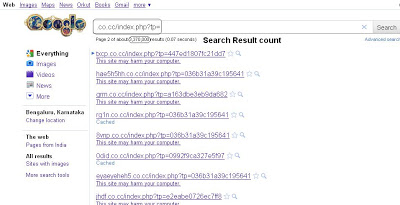
Recently, we have seen an increase in Blackhole exploit kit attacks. Blackhole is yet another web exploit kit developed by Russian hackers. According to one forum, the author indicates that the kit will cost $1,500 annually, $1,000 for a half-year and $700 for 3 months. It is a very powerful kit with a number of recent exploits including Java and Adobe PDF exploits. The attacker has continually improved the kit with more obfuscation and crypto algorithms to avoid the detection by AV vendors. One of the lines from description of the kit says it all - “Exploits crypt on special algorithms that make it impossible to code analysis and detection of anti-virus as well as services,Tipo wepawet and other counterparts ...”. Analysis of this malicious toolkit showed that URL patterns remain the same for most of the malicious domains hosting the Blackhole exploit kit. A Google search for the URL patterns returns thousands of results for such domains and Google does generally flag them as malicious domains. Here is the screenshot of Google search:
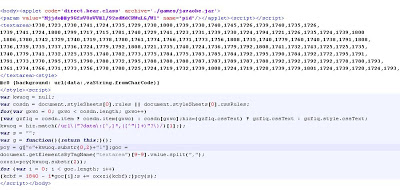
The exploit kit sends heavily obfuscated JavaScript code with Java applet code, which will download a malicious JAR file to the system. Here is what the code looks like:
The above JavaScript code is formatted for better viewing. It is heavily obfuscated to avoid antivirus detection. If we decode the content, we see that the kit is targeting a recent vulnerability in Java. The VirusTotal result for above “.jar” file is very poor with only 2 antivirus engines triggering on it. Here is the decoded part of the script,
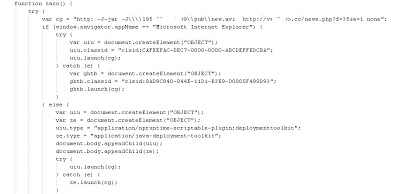
The above decoded JavaScript targets CVE-2009-1671. It will download a malicious binary called “info.exe” from the server and execute it on the system. The VirusTotal result for this file remains poor at only 47%. There is also another Iframe attack in the decoded JavaScript code.
The above code will append the malicious Iframe to the body of the webpage, which points to another malicious URL. The above malicious URL contains yet another malicious URL in an ASX file format. This is intentionally done to avoid a user prompt. Here is the source,
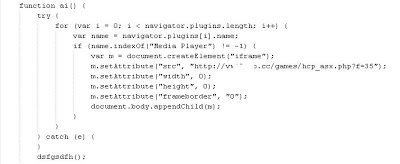
This URL then sends more obfuscated JavaScript code exactly like the second image of the blog. Once decoded it shows JavaScript code which targets CVE-2010-1885. Here is the decoded script,
We have seen many similar web exploits kits in the past and attackers are coming up with new ones like Blackhole with more features and reliable and undetectable exploits all the time. We are also seeing large number of malicious domains hosting Blackhole exploits kit. The detection ratio is generally very poor for malicious binaries contained in the kits. Even though the price of this exploit kit is high, it remains a sought after commodity.
Umesh