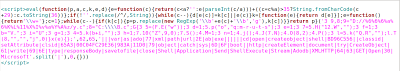
Lets look at obfuscated JavaScript used:
The de-obfuscated code looks like this:
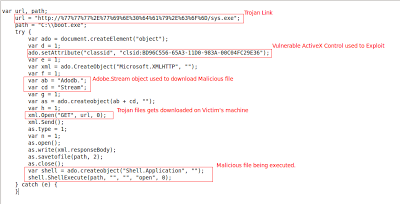
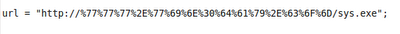
The exploit takes advantage of vulnerable ActiveX object “RDS.DataControl” having classid “BD96C556-65A3-11D0-983A-00C04FC29E36”. The exploit is designed to download executable files, which are then stored on victim's machine. This executable file path in the exploit is as follows:
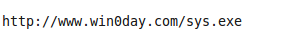
This in turn decodes to:
Virustotal results indicate that 21/43 AV engines have protection against this Trojan – a concerning statistic considering the age of the exploit used to deploy the malware. Virustotal’s URL submission indicates that malware URL was submitted on 2010-11-18 and still is in active state. Why would attackers continue to leverage such an old vulnerability? Sadly, as we have shown in our quarterly reports, nearly one in five corporate users still employ Internet Explorer 6, a nine year old web browser.
Pradeep




