WordPress is, by far, the most popular open source software used to build and host websites. So much so that, according to a July 2020 survey, around 455,000,000 websites are using WordPress. Overall, WordPress sites make up 14.7 percent of the Top 100 websites in the world. And some of the sites that use WordPress as their CMS, include NBC, CNN, TechCrunch, People magazine, the NFL, Best Buy, CBS Radio, and UPS. These are just a few of the Fortune 500 companies powered by WordPress.
So, many organizations should be concerned when cyberattacks are focused on the vulnerabilities in this popular CMS, which we have reported on previously in this blog. Recently, the Zscaler ThreatLabZ team discovered a number of phishing and scam campaigns hosted on popular CMS sites built using WordPress. We uncovered the entire campaign, including how some of the WordPress plugins were exploited for malicious intents.
In this blog, we are going to look at the three plugin vulnerabilities that are being actively exploited by attackers to compromise the WordPress sites.
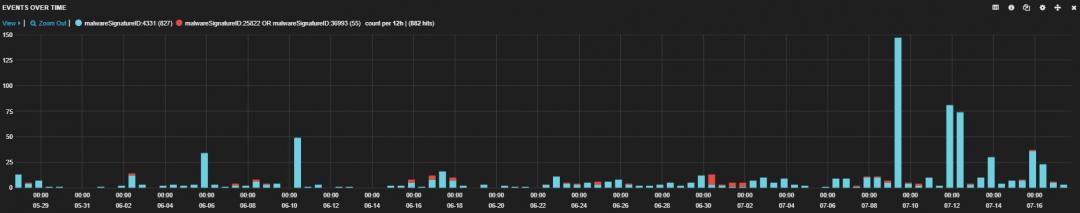
The following image shows the overall hits of the WordPress sites affected by these campaigns observed in the past 3 months in our Zscaler Cloud.
Figure 1: Hits of the compromised WordPress sites.
Vulnerability 1: WooCommerce plugin
WooCommerce is a popular WordPress e-commerce plugin widely used by online merchants. A few years ago, researchers found an arbitrary file deletion vulnerability in a WooCommerce plugin that is earlier than version 3.4.5. This vulnerability allows an attacker to execute arbitrary code on the target system. WooCommerce has patched this vulnerability in version 3.4.6.
Even though the patched version of the vulnerability is available, we observed many sites still using the outdated versions, which made them vulnerable to this scam.
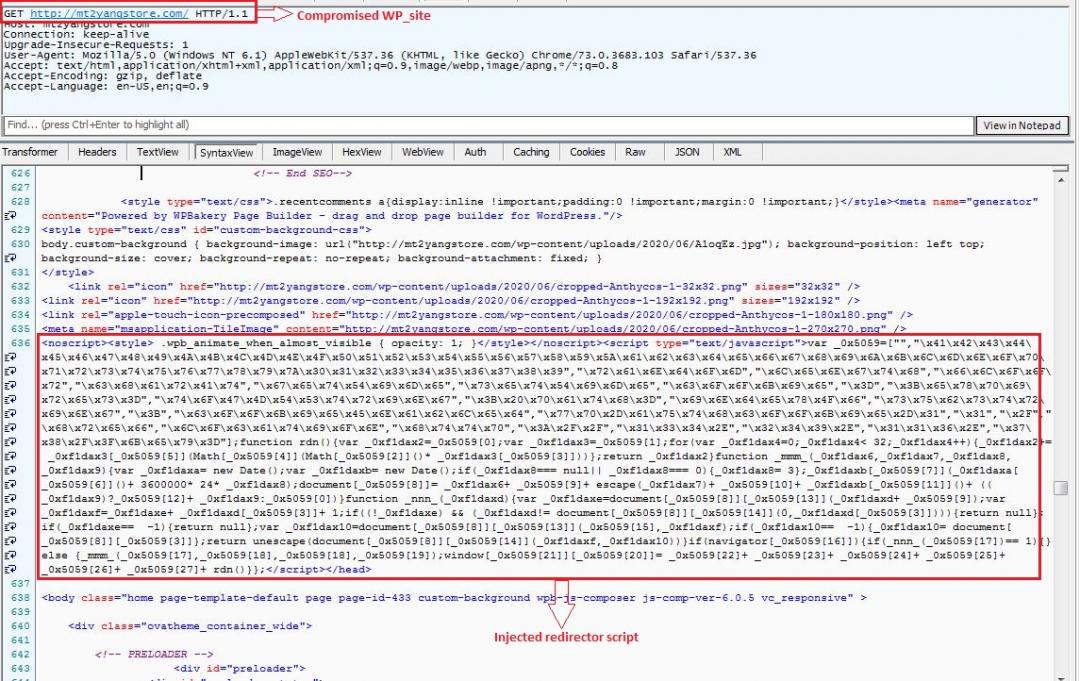
Let's see the working flow of this scam campaign in detail. The following picture depicts the source code of the compromised site with the injected obfuscated redirector script that is present in the site.
Figure 2: The source page of the compromised WordPress site (mt2yangstore.com).
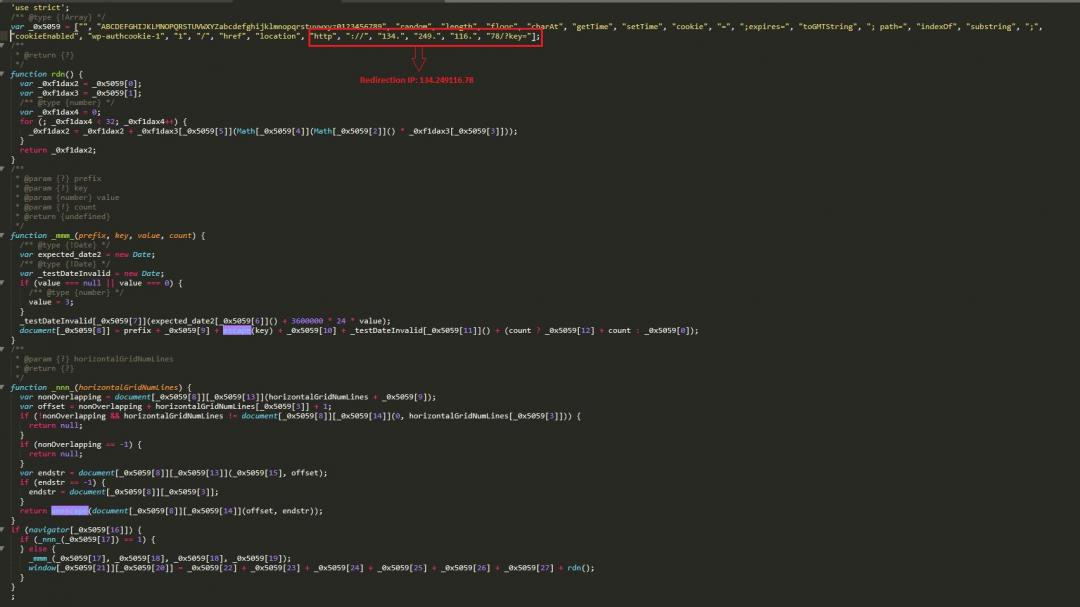
We deobfuscated the injected JavaScript code. The script is redirecting users to the IP 134.249.116.78.
Figure 3: The deobfuscation of the injected redirector script.
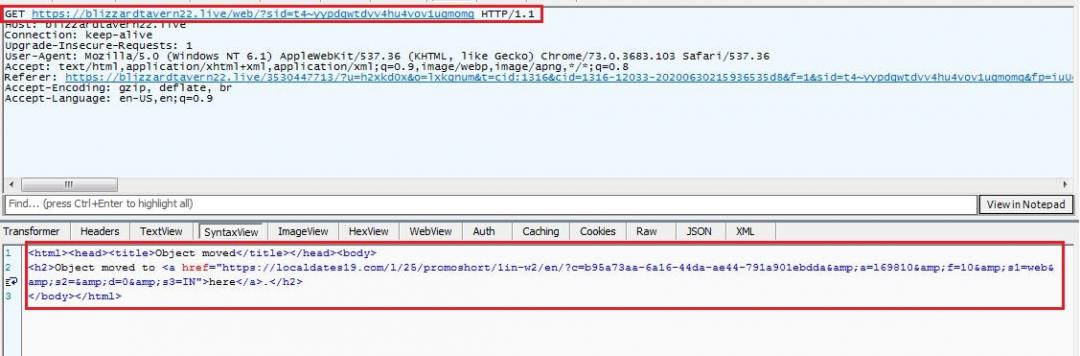
Figure 4 shows the redirected traffic to the above-mentioned IP address (134.249.116.78).
Figure 4: The redirection traffic captured in the Fiddler session.
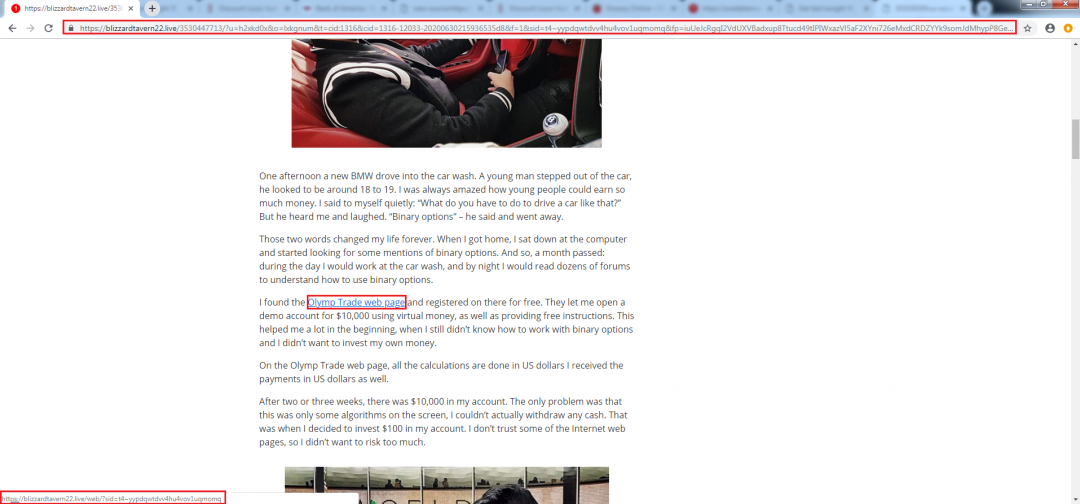
After multiple redirections, the attacker takes the victim to the following scam campaign.
Figure 5: The scam page redirected from the IP address (134.249.116.78).
The scam campaign tricks the user into creating a trading account by opening the link highlighted in Figure 6.
Figure 6: The masquerade link that acts as a web link to create a demo trading account.
Once the user clicks the link, it redirects the user to an adult site instead. The following picture shows the redirection traffic of the final landing page.
Figure 7: Web traffic of the redirection page.
Figure 8: User redirected to adult content from the compromised site (mt2yangstore.com).
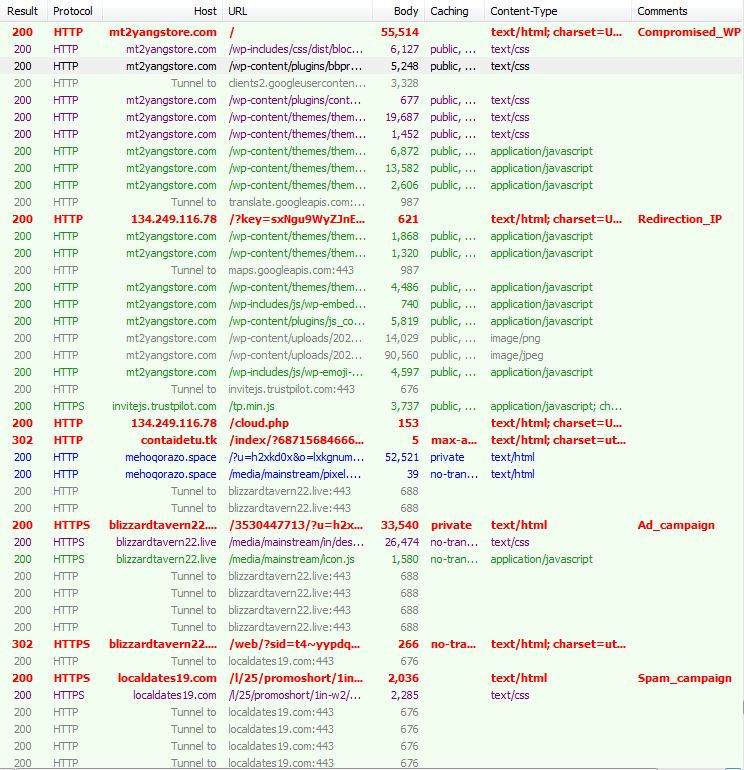
Figure 9: The overall web traffic of the scam campaign captured in the Fiddler session.
Vulnerability 2: WordPress Yoast SEO plugin
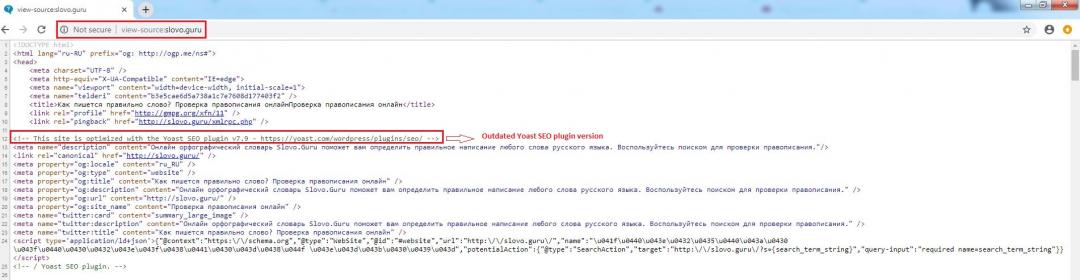
Similarly, we have observed the same scam campaign was hosted by exploiting the Yoast SEO plugin with different scam templates. A stored cross-site scripting vulnerability was discovered in the past year by researchers in Yoast SEO plugin. The vulnerability allows attackers to inject a redirector script in the affected WordPress site. A patched version of this vulnerability was released under version 11.6 and the current updated version is 14.4.1.
Figure 10: The source page of the WordPress site with an outdated Yoast SEO plugin version.
The same redirection script is injected on the compromised WordPress site as shown in Figure 11.
Figure 11: The same injected redirector script in the compromised WordPress site (slovo.guru).
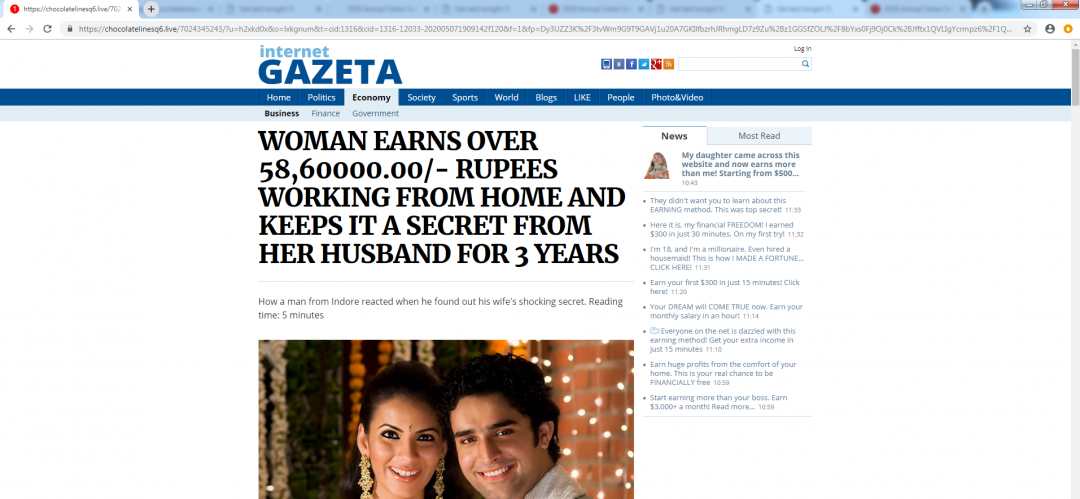
Here, the scam campaign used by the attacker states that “Women earn money” online using the same trading platform that also sends victims to the adult-related sites.
Figure 12: A different scam campaign template used by attackers.
Vulnerability 3: WordPress All in One SEO Pack plugin
A stored cross-site scripting vulnerability was discovered last week in the popular WordPress All in One SEO Pack plugin. The vulnerability allows authenticated users to inject malicious scripts by accessing the wp-admin panel's “all posts” page. All versions of this plugin before version 3.6.1 are vulnerable. The patched version of this vulnerability was released on July 15, 2020, and the current updated version is 3.6.2.
Figure 13 shows the source code of the compromised WordPress site with the injected redirector script. The phishing redirection takes place only if the getProcessHash() function satisfies the condition. The redirection will take place if the compromised site contains the “email” string with the preceding hash value(#).
Fig 13: Source code of the compromised WordPress site with the injected script.
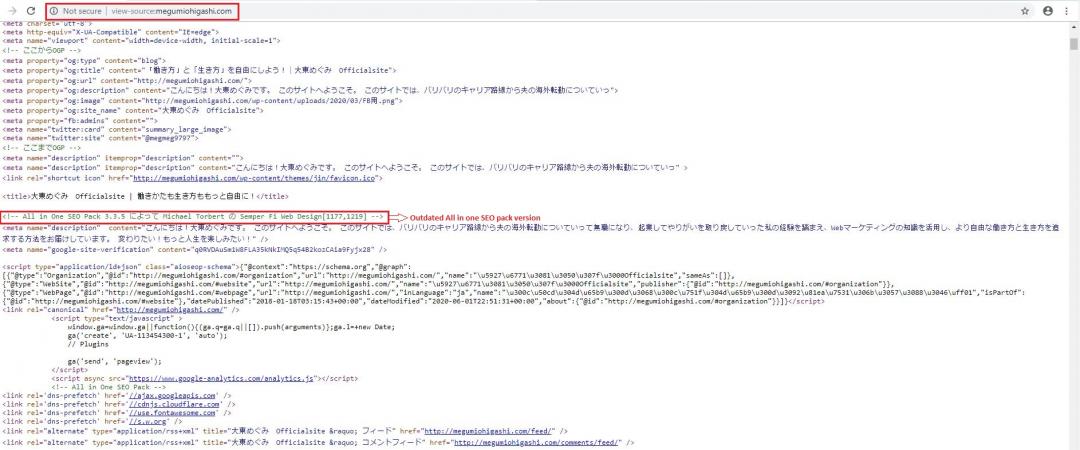
Figure 14 shows the vulnerable version of the All in One SEO Pack plugin in the source of a compromised WordPress site.
Figure 14: The outdated version of the All in One SEO Pack plugin.
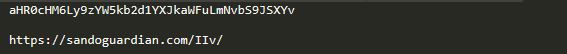
Figure 15: The deobfuscated phishing redirection URL.
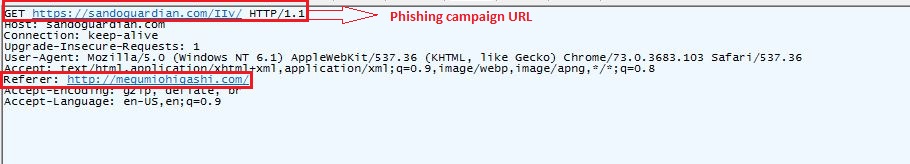
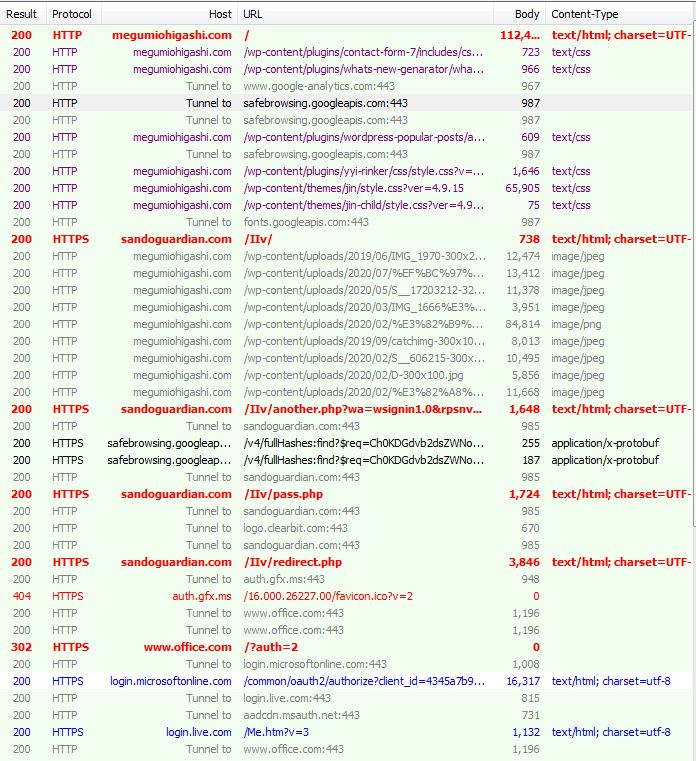
We were able to see the web traffic of the phishing site redirected from the compromised WordPress site during the Fiddler session.
Figure 16: Redirection traffic to the phishing site captured in the Fiddler session.
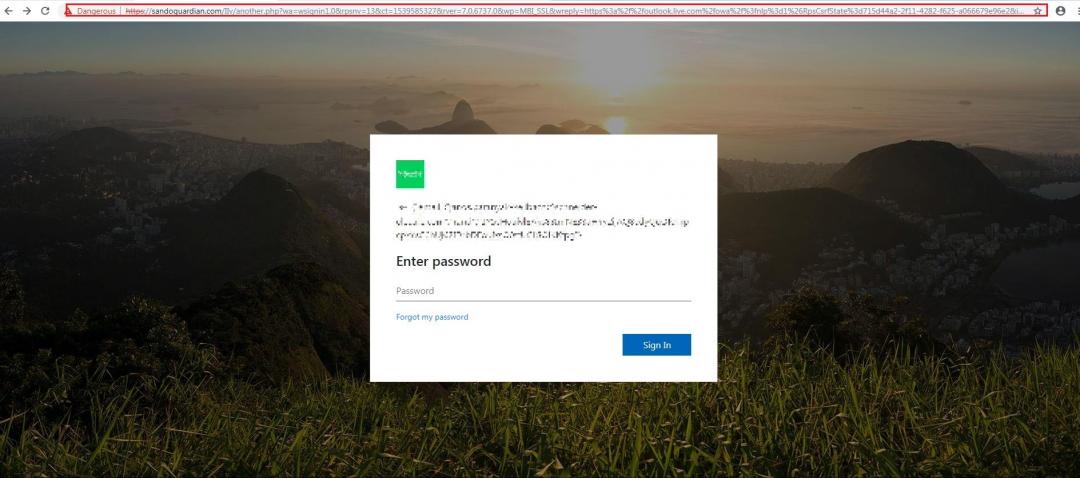
The final destination of this campaign is a spoofed Microsoft phishing site.
Figure 17: The hosted Microsoft phishing campaign from the compromised WordPress site.
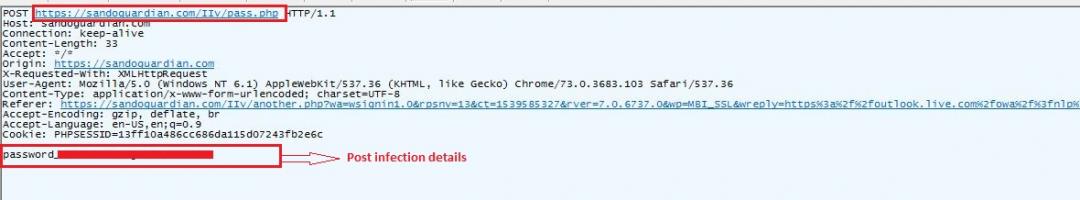
Figure 18: Credential theft from the Microsoft phishing campaign.
Figure 19: The overall web traffic of the phishing campaign captured in the Fiddler session.
Conclusion
Cybercriminals are actively tracking the most popular content management systems (WordPress) to find loopholes and vulnerabilities to exploit them to perform malvertising activities. Website owners should be aware of such campaigns and should maintain their plugin versions patched with the latest security updates. The Zscaler ThreatLabz team is actively tracking such campaigns and blocking them to protect our customers.
Indicators of Compromise
Vulnerability 1 and 2
Malicious IP:
134.249.116.78
Scam site:
localdates19.com
Compromised WordPress sites:
accept.ddns.net
addyaoutdoors.com
aiforum.guu.ru
alkawtherwater.com
ateamhouston.com
belocean.com.mm
celejow.siwydym.pl
chaykaraneshomal.com
cocotierlodge-nosybe.com
denizdugunsalonu.net
emirizm.com
hydro-m.fr
jaguar70.ru
kare.ba
kdrsweb.com
magasini.com
mahawu.com
Mlshop.pl
mt2yangstore.com
pestostop.com
reservator.news
slovo.guru
www.aldawliatires.com
www.art-logics.com
www.babystorelaspezia.com
www.bhagwandascycle.com
www.carlube.co.uk
www.davincyinstituts-minceur-reunion.com
www.detayinterior.com
www.ecsgroup.co
www.flaviomosconi.it
www.szzccc.com
www.trilogym.it
Vulnerability 3
Phishing URL:
sandoguardian.com/IIv
chhotumaharaj.com//temp/IIv/
Compromised WordPress sites:
Megumiohigashi.com
houjuen.org