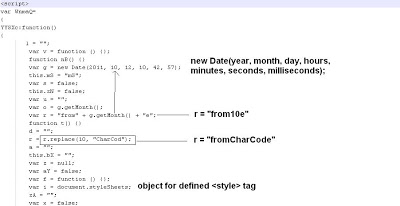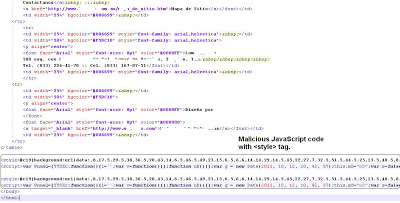
The above code contains one style sheet defined by “#c19”. After further inspection of the code, we determine that variable “WnmaQ” is defined with function “YYSXc()”. After that, there are 3 other variables defined, with 2 of them containing garbage or useless functions and then there is a call to the original function by accessing “Wnmaq.YYSXc()”. This means this code will call the function inside the first defined variable which is “Wnmaq”. Now let’s format that function and break the code into parts so that we can decode it step by step. Here is first part of the script,
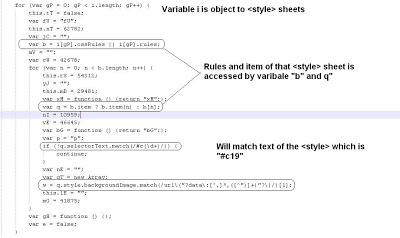
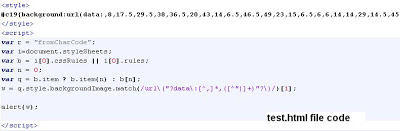
The above “for()” loop will actually extract the array data from the style tag defined earlier. I have put some comments inside the image to better explain the components of the code. Initially, variable “q” is matched with elements corresponding to the style sheet rule with the help of the “.selectorText” property. If the loop matches the string”#c19” of the style sheet, the code will continue. The next variable “w”, actually retrieves the array from the style sheet rule with the help of the property “.style.backgroundImage”. Now, we finally have useful variables. At this point, we should test to ensure everything seems reasonable. Let’s create a simple “test.html” file and add only important variables, style sheet tags and code inside the HTML file. We will test what the variable “w” will contain after above code with the help of “alert()” function. The sample HTML file is shown below:
We have removed everything and added only those variables which we decoded earlier. We should get array values from style tag. Here is what the variable “w” will contain after running above file.
So, the second part of the script just retrieved values from style tag. This shows our analysis is on the right track. We will keep this “test.html” file as it is and will add more interesting code after additional analysis. Let’s look into next part of the main script:
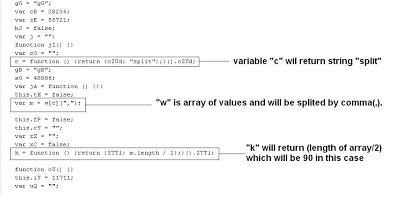
The above code explains that variable “c” will contain string called “split” and variable “m” will contain array values separated by commas. The variable “k” will contain a value which will be the array length divided by 2. We will add all above 3 lines of code into our “test.html” file and will then alert the value of “k” for our purposes. The variable “k” will contain the value 90 if you run the modified “test.html” file. The above code also contains garbage code as mentioned earlier. Let’s decode the last part of the main script,
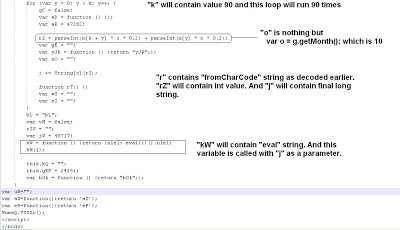
The above code is the last part of the main malicious script. Here we will finish the decoding of the code and will come to determine the main malicious code behind this. As analyzed earlier, variable “k” will contain value 90 and this “for()” loop will run 90 times. The function “parseInt()” is used to obtain the exact integer. The variable “o” will contain the month of the date object, which is 10. The variable “r” contains the string “fromCharCode”, which we found earlier. So finally variable “j” will look like,
j += String[“fromCharCode”][rZ];
The loop will continue and variable “j” will be appended with characters retrieved from above expression. This is the main code behind the entire script. The last variable “kW” contains the JavaScript function “eval()” and then there is call to this function with parameter “j”. This tells us that the malicious content will evaluate the code inside the variable “j”. Let’s add this “for()” loop inside our earlier “test.html” file and we will alert the value of “j” to find out the hidden code. This is what our final “test.html code will look like:
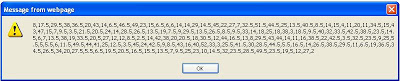
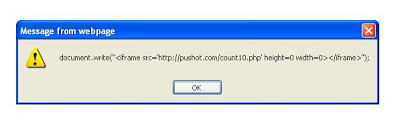
We have only added useful variables, loops and JavaScript code in the above file. We have removed useless variables and functions from the main script. Now here is what you see when you run the above file:
The malicious Iframe pointing to malicious domain is finally revealed. The attacker has created the malicious JavaScript code with the help of a style tag to generate a malicious Iframe. This process can be difficult to analyze and tools or services may fail due to the complex nature of the code and various tricks used by attacker. However, if you have a little patience and good eyes, it is very easy to decode such malicious JavaScript code by understanding the flow of the code. That’s it for now.
Happy Decoding
Umesh