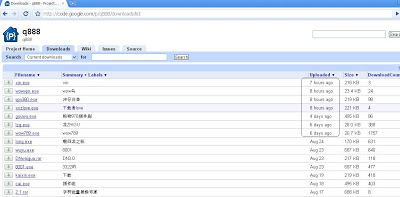
Most of the files are executable files along with zipped “.rar” files. The time stamps show that the files have been uploaded over the course of the last month. This suggests that an attacker is actively using this free service to spread malware. Virustotal results for the first file, show that only 8 antivirus vendors out of 43 flagged the file as malicious. The detection ratio for second file is slightly better than that of the first file.
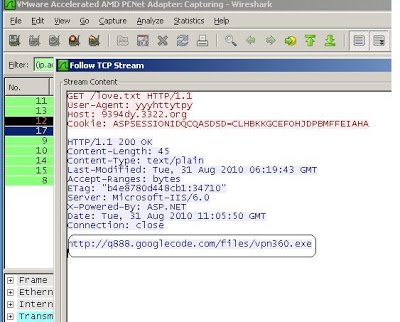
Let’s analyze first file which is “xin.exe”. When the first file is executed on the system, it will make several GET requests to download additional malware onto the system. Here is the first GET request,
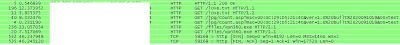
A request for the “love.txt” file contains additional malware also stored on the Google Code site. Here is the link to an analysis of malware by Sunbelt security. The malware performs significant file, network and process activity to while infecting the system. Here is the packet capture of various requests to receive additional malware.
Further analysis of all files shows that they are all malicious threats including Trojans horses, backdoors, password stealing Keyloggers for online games such as “World of Warcraft” etc. Analysis of the file resources from ThreatExpert report indicates the possible country of origin is China. Interestingly, Google Code FAQ page says they will take down the whole project if they find malware being hosted on the project.
The question is how and when the Google Code team scans content hosted on their website to ensure that it’s not infected with malware? The first malicious file was uploaded on June 24, 2010, while this blog was written at the end of August – over a month has passed and still the malicious files are being hosted at the Google Code site. The attacker not only storing old malware but he is also actively uploading new malware on the site. The detection ration by AV vendors varies from reasonable to poor given the specific malware sample. As Google Code is free hosting website for developers, attackers are clearly taking advantage of the site to push their malware.
Have you hosted anything?
UPDATE: 2 September 2010
Google has immediately taken down the project and URL to that project is no longer accessible.
Umesh