Many of you already regularly use
ZULU, our free service for analyzing any URL to determine it's overall risk and we've just made it better by adding a '
heartbleed' check. ZULU operates by applying a variety of checks to the
content,
URL and
host for a given web page, along with doing the same for external page elements. You will now note that the
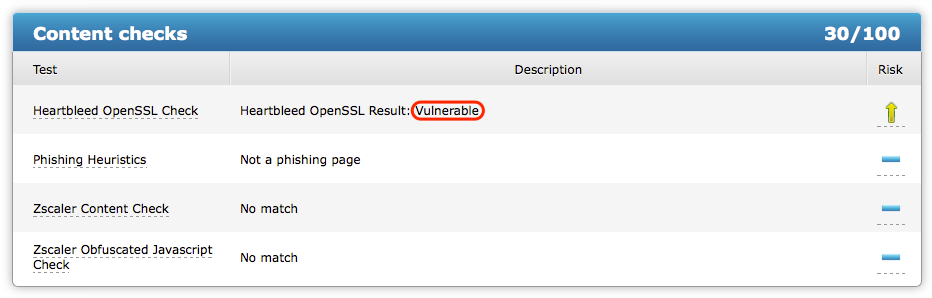
Content Checks section includes a
Heartbleed OpenSSL Check.
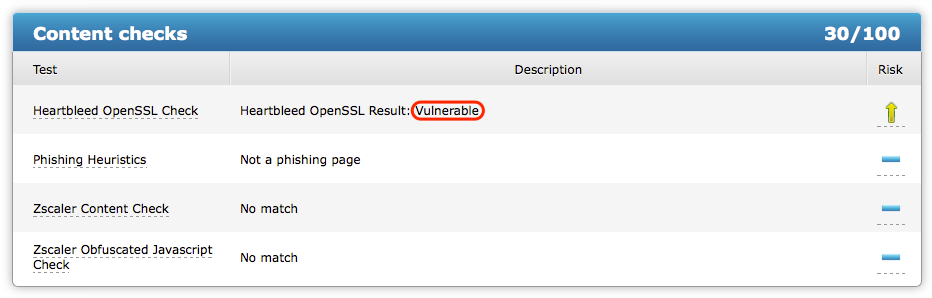 |
| Vulnerable Result Shown for Heartbleed OpenSSL Check |
For more information on why heartbleed is such a serious vulnerability, take a look at our earlier
blog which details how exploitation occurs. In a nutshell, the heartbeat TLS extension allows one machine to send a small packet to another to keep a TLS connection open. That request includes a small message, which the responding machine subsequently includes in the reply. The problem occurs as the request also includes a parameter indicating the size of the message, which is not properly validated in some versions of OpenSSL. Therefore, if the size value is larger than the actual size of the message, the response will also include random data from memory to fill the void. This is a serious data leakage issue as the response could include sensitive information such as passwords, cookies and even private encryption keys. The impact of this vulnerability is also exacerbated by the fact that OpenSSL is such a popular SSL implementation, leaving
many popular websites vulnerable.
Now when you run a ZULU scan, as part of the overall content checks, we also send a heartbeat request to port 443 on the server. We check to see if an SSL server is present and if it will respond to a request where the specified message size does not match the actual length of the message. If that's the case, the report will state
'Heartbleed OpenSSL Result: Vulnerable' in the report and the overall score will be adjusted accordingly.
- michael