The page itself provides no visible indication of infection, but if you look at the source of the webpage, you will notice a malicious IFrame injected under the Latest News section. Here is the source of page,
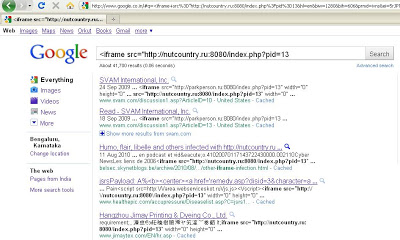
The malicious IFrame points to “hxxp:// nutcountry.ru:8080/index.php?pid=13” which is currently down. By taking the advantage of known/unknown vulnerabilities, attackers have injected malicious IFrames into many legitimate web pages. In this particular case, not only the home page is infected, but all the other pages on the site are infected. This likely indicates that the attacker used a SQL injection vulnerability to inject the malicious IFrame into the backend database from which webpages are dynamically generated. A quick search on Google reveals a significant number of websites infected with with the same IFrame. Here is screenshot of the search results:
Another search reveals that Google has begun to proactively warn users about some of the pages associated with this attack.
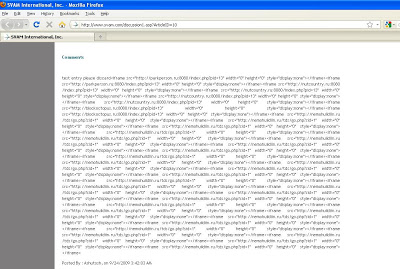
You will note that the search results include ~85k sites which suggests that this particular attack was very broad in scope. This attack also appears to have leveraged persistent XSS (Cross Site Scripting) vulnerabilities to inject malicious IFrames into the comment sections of various web forums. Here is a screenshot of one such website:
Here is a list of malicious IFrames associated with this attack that you should block:
hxxp:// nutcountry.ru:8080/index.php?pid=13
hxxp:// parkperson.ru:8080/index.php?pid=13
hxxp:// blockoctopus.ru:8080/index.php?pid=13
hxxp:// nemohuildiin.ru/tds/go.php?sid=1
hxxp://vamptoes.ru:8080/index.php?pid=13
hxxp://www.bindispute.ru:8080/index.php?p13
hxxp://www.bellday.ru:8080/index.php?pid=13
Attackers are continuing to take advantage of the poor security in web applications by writing utilities that are capable of infecting large numbers of sites in short period of time due, which in turn translates to thousands of victims with minimal effort.
Umesh