The dominance of exploit kits like Blackhole, Incognito and others, continues to be seen in the wild. Attackers continue to use these exploit kits to generate malicious webpages and host them on various domains. These exploit kits usually targets browser and browser plugin vulnerabilities.
To increase the likelihood of a successful attack, exploit kits are commonly used to infect legitimate sites that already have significant traffic. Attackers achieve this by crafting scripts designed to identify sites with injection vulnerabilities, which allow for hidden iFrames to be written, which then point to the exploit kit URL. When users visit the infected sites and are redirected to the browser exploit kits, a known browser or plugin vulnerability is typically used to download and execute malicious content without user knowledge. You can visit this related blog for more information about iFrame injection in detail.
Recently, I’ve seen a spike in such compromised sites, which lead to exploit kit URLs. In most cases, the JavaScript code containing the hidden iFrame is heavily obfuscated. Different exploit kits have their own techniques to obfuscate malicious code. Let’s take look at a couple of examples and their respective de-obfuscated code.
iFrame leading to Incognito exploit kit
URL: hxxp://www.snapstudios.net/kitchen-set-hidden-behind-the-cupboard.html
Obfuscated code:
The aforementioned obfuscated code was injected at the start of the webpage. Let’s deobfuscate the code to make sense of it.
De-obfuscated code:
You can see that the deobfuscated code generates a hidden iFrame with the ‘src’ attribute being assigned the exploit kit URL. Generally, the visibility of the iFrame is kept hidden and dimensions are kept to a minimum, which ensures that the iFrames don’t alter the look and feel of the page.
Exploit kit URL: hxxp://racingengines.osa.pl/showthread.php?t=63942072
After observing patterns in the exploit URL, one can determine that this URL belongs to the Incognito Exploit kit.
Suspicious URL Pattern: “/showthread.php?t=”
Search results for the above pattern at www.malwaresomainlist.com confirms that URL belongs to the well known Incognito exploit kit. The exploit kit URL is still active but currently not delivering the malicious code. Visit this blog on Incognito exploit kit for more details.
iFrame leading to Blackhole exploit kit
URL: hxxp://steelrode.com/
Obfuscated code:
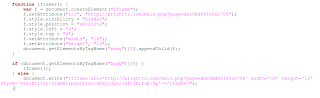
De-obfuscated code:
Exploit kit URL: hxxp://brighttz.com/main.php?page=dac9bd89165e2708
Suspicious URL pattern : “/main.php?page=”
Search results for the suspicious pattern at www.malwaredomainlist.com can be found here. The exploit kit URL is not currently active. We have been writing about the Blackhole exploit kit for some time. At present, this seems to be the favored exploit kit amongst attackers. You can find more information about the Blackhole exploit kit here.
Fortunately, the aforementioned exploit kit URLs have been blocked by Google Safe Browsing. A sample Google diagnostic report of the Incognito exploit kit URL can be found here. While conducting research I came across a number of such compromised websites on a daily basis. Attackers continually alter obfuscated code to ensure that it is not yet detected by popular AV/IPS/IDS vendors. This keeps them one step ahead in this ongoing game of cat and mouse.
To conclude, I would like to say,
“The growth in compromised websites is directly proportional to the growth in popularity of different exploit kits”.
Pradeep