hxxp://www.clickspot.biz
hxxp://stats.hillmedia.biz
hxxp://cdn.cbtclick.biz
hxxp://88.80.5.3
hxxp://www.clickbig.biz
hxxp://stats.woodmedia.biz
Here is how random requests looks like,
hxxp://88.80.7.152/cgi/tjo.php?ddddd=4x4x4x4x4x70x
hxxp://88.80.7.152/cgi/dsiy.php?dsydm=5561671
hxxp://88.80.7.152/babymaybe/hwmcr.php?wmcrx=06166<1x644434x4x4x4x=x>
hxxp://88.80.7.152/babynot/blfp.php?dxrzz=77445=1x644413x640
hxxp://cdn.cbtclick.biz/babynot/ecccccc.php?cccc=4x4x640
hxxp://88.80.7.152/cgi/scrhxm.php?rhxm=4x4x4x4x4x70x
hxxp://88.80.7.152/cgi/nd.php?iy=4x4x4x4x4x70x
hxxp://88.80.7.152/cgi/ffffffff.php?fff=4x4x4x4x4x70x
hxxp://88.80.7.152/cgi/raqfv.php?aqf=4x4x4x4x4x70x
hxxp://stats.hillmedia.biz/cgi/wl.php?rgmra==<44=46x644547x640>
As the above requests show, every request is unique, containing random data. This is done to fool IDS/IPS engines from detecting the malicious requests. The C&C server replies with Content-Type “image/jpeg” which contains JPEG image with malicious commands hidden inside. The malicious image file contains the JPEG header followed by some commands that are in encoded format. We observed by downloading some image files that first part of the command remains same and later part changes values. Here are some examples:
lppt>++<<*<4*3*516+`+`h*tlt;bh9g<4f=g=fb==1f5aefg6364a1<64fa4fe"bm`9544"5911266139|200118|2048|0|0|66
lppt>++<<*<4*3*516+`+`h*tlt;bh96efe<6600g6fbb`5<14253a4ea5=6`03"bm`9544"593300195|200057|2048|0|0|2
lppt>++<<*<4*3*516+`+`h*tlt;bh9ag=3g7a31<6<<17`7b2`b53f1`52=ff7"bm`9544"591955928|200044|2048|0|0|18
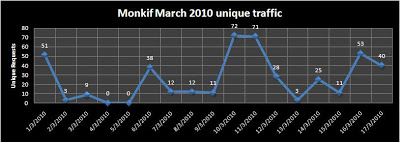
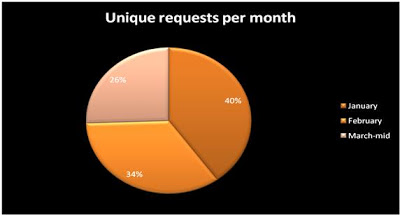 The unique network traffic for Trojan Monkif remains approximately same for each month in this quarter (March data is up to 17th). The detection for these JPEG file is zero (here is the Virustotal result for one of the C&C image files). This means you are at a greater risk from this Botnet if you are relying on only a single security protection like Antivirus.
The unique network traffic for Trojan Monkif remains approximately same for each month in this quarter (March data is up to 17th). The detection for these JPEG file is zero (here is the Virustotal result for one of the C&C image files). This means you are at a greater risk from this Botnet if you are relying on only a single security protection like Antivirus.We are near to end of Q1, 2010 and Botnet attacks remain a large threat on the web. Previously, we saw Koobface activity rise and fall, but this Monkif threat remains consistently active. The attackers behind Trojan Monkif are evading the detection by hiding their malicious Botnet commands inside JPEG files. The commands inside the JPEG files are encoded and vary, making detection more difficult for Antivirus vendors. The Virustotal result shows none of the Antivirus vendors out of 42 are detecting these malicious samples. The web is growing and so are Botnets. Currently, we are seeing only a few C&C servers being used for this Trojan, but this may increase in the future. Koobface and Monkif have been active threats in the Q1 2010, but Monkif has remained consistent. Zscaler’s solution is detecting these kinds of attacks every day. Be sure to block the above-mentioned malicious domains, and check that your security solutions are protecting you from these dangerous threats.
Be Safe!!!
Umesh




