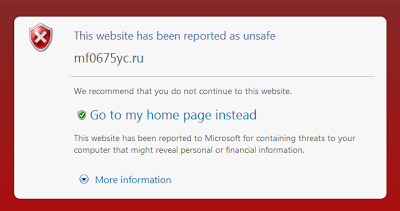
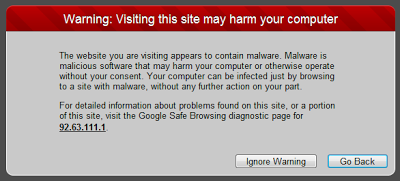
All modern web browsers now include protection from malware. They include a list of known malicious URLs, and compare each address visited by the user against this list. If the URL is recognized as malicious, a warning message is displayed in place of the HTML page. They also protect against phishing sites, but I won't dive into this feature during this post.
Chrome, Safari and Firefox 3.x use Google SafeBrowsing, while Internet Explorer 8 has SmartScreen Filters and Opera includes lists from Netcraft and TRUSTe. Note that it took Safari more than 20 minutes for SafeBrowsing to start working after I upgraded from Safari 4. It did not show any warning informing me that malware protection was disabled while it was retrieving the database.
Safari warning message
I was wondering how well these protections work against current threats. Since antivirus doesn't perform well against viruses spread through fake AV pages, fake videos, or against malicious jar files, I wondered if these browser denylists would keep users safe against current spam SEO attacks.
I've tried a few domains for each type of attack, using each browser. All the malicious domains were directly identified from within Google search results using popular search terms.
Protection Against Fake AV Pages
I first tried various new fake AV domains as well as subdomains for xorg.pl (hostguard-31p.xorg.pl, hostguard-47p.xorg.pl, ubersaving26.xorg.pl, etc.), a domain that has hosted fake AV pages for months.
| Browser | New domains blocked | Xorg.pl subdomains blocked |
|---|---|---|
| Firefox 3.6 | 7/7 | 5/5 |
| Internet Explorer 8 | 2/7 | 0/5 |
| Opera 10.5 | 0/7 | 0/5 |
Google Safe Browsing is very good at blocking fake AV pages. We report to Google on fake AV domains we identify that they don't block, but we're noticing that there are fewer and fewer they don't already block.
Protection Against Fake Video Codecs
This type of malicious page seems to have staged a comeback, and we're seeing them more and more frequently since last weekend. In this scenario, the user is tricked into downloading an executable disguised as a video codec or new flash version.
| Browser | URLs blocked |
|---|---|
| Firefox 3.6 | 2/6 |
| Internet Explorer 8 | 5/6 |
| Opera 10.5 | 0/6 |
Internet Explorer did a great job at flagging the fake video sites. Google Safe browsing, surprisingly, had a very low rate of success.
Protection against Java/PDF/Flash exploits
The number of Java exploits has also increased dramatically over the past few weeks.
| Browser | URLs blocked |
|---|---|
| Firefox 3.6 | 2/4 |
| Internet Explorer 8 | 1/4 |
| Opera 10.5 | 0/4 |
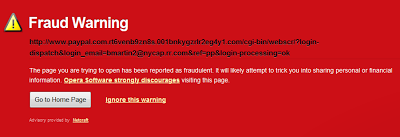
Opera did not flag any of the malicious sites. Their security denylists may be targeting phishing only. To make sure the security notification worked, I attempted to visit a phishing site, and Opera did warn me.
Opera phishing warning
-- Julien