- The hijacked website redirects users coming from a Google search to an external domain.
- A website redirects users to the Fake AV page or to a harmless site (mostly bing.com and google.com) depending upon the referer in step #1. This page adds a cookie using JavaScript, and reads it immediately, to make sure the page was accessed by a real browser that supports both JavaScript and cookies.
- The fake AV page is delivered.
Hijacked sites
I demonstrated last year that the Blackhat SEO attacks had migrated from the most popular searches to more specific searches like buying software online where up to 90% of the links returned are malicious. It comes as no surprise that about 95% of the hijacked sites were found for searches like "purchase microsoft word", "achat windows" ("buy Windows" in French), "precio office 2007" (Italian), etc.
There were 12 hijacked sites being used, with 3 domains representing 90% of the hijacked sites redirecting to a fake AV page:
- politicalcampaignexpert.com (WordPress)
- www.extralast.com (WordPress)
- www.ukresistance.co.uk (blocked by Google Safe Browsing)
The domain used to redirect users from the hijacked sites to the fake AV pages are all .ru sites, with the same URL path:
- bannortim-qimulta.ru/industry/index.php
- daliachuuaroyalys.ru/industry/index.php
- bannortim.ru/industry/index.php
- uaroyalysdaliachu.ru/industry/index.php
- uaroyalys.ru/industry/index.php
- etc.
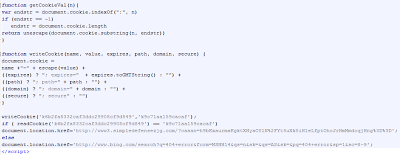 |
| JavaScript and Cookie support test |
Fake AV page
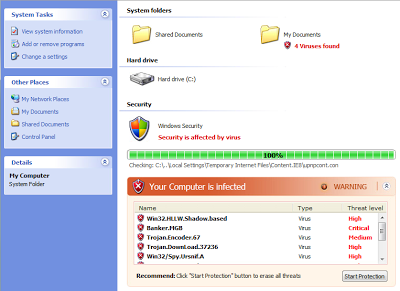 |
| Fake AV page |
Attackers are getting lazy! The fake AV page looks the same as it did two years ago and the source code of the page has barely changed. Fake AV pages used to change every 2-3 weeks when they were found all over the most popular searches, now they are remaining stagnant for six months. Here is the video that shows the Fake AV page in action:
As you can see in the video, the malicious executable is detected by 14 of 43 AV vendors.
Hopefully, one day Google will clean up the search results related to buying software as they did for the most popular searches. Until then, many users will end up on fake stores, fake AV pages or other malicious sites.




