You have likely seen the use of code signing certificates when Windows pops up a User Account Control (UAC) warning to ask for your permission to make a change to your system. If the executable is signed by a Trusted code signing certificate, the UAC will display a "Trusted Publisher" notice, otherwise it will display an "Unknown Publisher" notice.
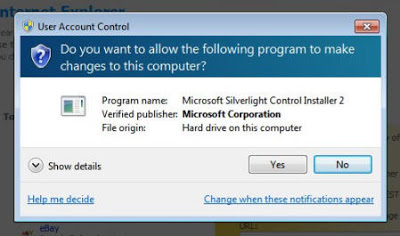 |
| Trusted executable |
 |
| Executable not signed |
However, you can actually do much more with a stolen code signing certificate. Using the Microsoft ClickOnce technology, it is possible to download, run and install any executable on the user's desktop just with one click on a regular HTML link. Users do not have a way to stop the executable from being downloaded and installed once the link has been clicked.
If you use a valid code signing certificate to sign a ClickOnce deployment file and the certificate is not part of the user's list of Trusted Publishers, you will receive the following popup:
 |
| ClickOnce abused. You can choose between Install and Run. |
You may have noticed several elements that make this popup look more reassuring to a user than the usual download/run popup from Internet Explorer:
- The popup is not actually part of the browser, it is actually a separate application.
- It claims to be a Windows Update. If the user clicks on the link, they will be sent to http://support.microsoft.com/.
- The software seems to be hosted on a sub-domain of microsoft.com.
- The publisher (myself), is trusted.
If you host the application on a sub-domain that is very long, the popup will truncate it, making it look like a sub-domain of microsoft.com if you carefully craft the URL. Since the popup width is the same on all Windows versions, regardless of the user screen resolution, such a misleading URL is easy to craft.
The valid code signing certificate cost me $59, but you can get one for free. With a "stolen" certificate from Microsoft, the UAC would show Publisher: Microsoft.
Trusted Publisher
You can bypass the UAC warning completely if the application is signed with a code signing certificate that is part of the "Trusted Publishers" list on the user's computer. In that case, there is no warning and no cancel button - the application is downloaded and run automatically. Pretty scary!
The good news - the "Trusted Publishers" list is empty by default on Windows. The bad news - some software vendors install their own certificates along side a separate software installation. Your administrator may also push your company's certificate to the list in order to deploy software automatically. If one of these certificates is stolen, or if the attacker can fool users into installing a certificate of his choosing (especially if it is signed by Microsoft...), then any application can be installed on your computer without your knowledge.
To verify if you have any certificates installed in your Trusted Publisher list, run "certmgr". In the right pane, click on "Trusted Publishers". if there are certificates, click on "Certificates" to see the list. To be safe, you should remove any that you don't explicitly recognize as needing to be there.
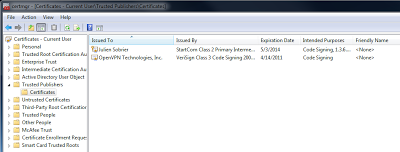 |
| My Trusted Publishers certificates |
There is no need to find vulnerabilities to install software silently on computers when ClickOnce lets you do so legitimately.




