The recent Microsoft Exchange server attacks have reportedly impacted 30,000+ organizations in the United States and 100,000+ organizations globally. Originally attributed to the Chinese threat group HAFNIUM, other threat actors are now believed to be using this vulnerability to steal administrator passwords, write and execute files, and gain access to sensitive information, greatly expanding the potential global impact as the tools and techniques become widely available.
For detailed information on the attack, signature coverage, and what to do if you are concerned you have been impacted, read the recent coverage advisory from ThreatLabZ.
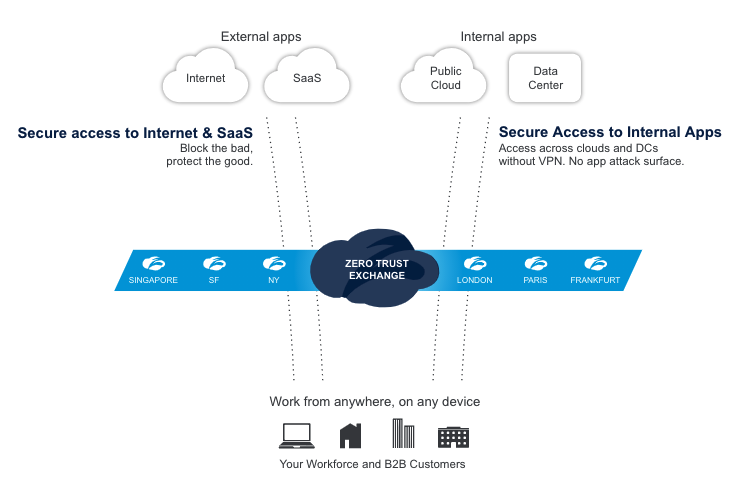
Our customers’ security is our top priority. The Zscaler ThreatLabZ team immediately began investigating these attacks to understand how the Zero Trust Exchange, the platform that powers all Zscaler services, could protect our customers, and if we could further bolster our existing security controls and best practices guidance based on newly available information. In this blog, we will share how you can secure your enterprise today and in the future with Zscaler's cloud-native platform and zero trust architecture, focused primarily on Zscaler Private Access (ZPA).
Eliminate your internet-facing attack surface: Prevent Outlook Web App (OWA) servers from being exposed to external attackers. Per Microsoft’s guidance, “the initial attack requires the ability to make an untrusted connection to Exchange server port 443,” which can be protected against by “restricting untrusted connections” and “[separating] the Exchange server from external access." While many enterprises have eliminated their on-premises Exchange servers and adopted Microsoft 365—with over 2,500 of them trusting Zscaler to protect their SaaS apps—not every organization is ready to make the move. If you still have a hosted Exchange server, there are several methods available to prevent exploitation of these recent vulnerabilities by stopping external access through ZPA:
- Desktop client access: If users are accessing OWA servers via a desktop client on a managed device, having the Zscaler client on that machine routes this traffic via encrypted ZPA tunnels to access the server, eliminating all external exposure.
- Browser-based access: If users are accessing OWA through a web browser—such as on an unmanaged device—ZPA Browser Access brokers a secure connection.
- VPN access: Putting your OWA server behind a VPN can mitigate some risk, but every VPN greatly expands your attack surface with highly exploited vulnerabilities, as seen in our 2021 VPN Risk Report.
If you have users connecting via both managed and unmanaged devices, you will need to implement ZPA for both desktop and browser-based access as described above. In these scenarios, Zscaler eliminates the threat vector entirely by making the Exchange server invisible to the internet. ZPA goes beyond the protection provided by a VPN, disallowing any inbound pings from the internet. Since there is nothing to ping or DDoS, the service is able to protect private apps from internet-based threats that wish to do them harm.
While we haven’t yet observed adversaries using a compromised network to launch additional attacks against other vulnerable Exchange servers, we recommend as a best practice inspecting all server traffic to stop any malicious outbound activity. Within Zscaler Internet Access (ZIA), we’ve added new signatures that will detect outbound activity that could be used to infect other vulnerable Exchange servers. We also recommend using Zscaler Workload Segmentation (ZWS) to prevent any unauthorized lateral movement, network recon activity, and/or payload execution, keeping an attacker who may have successfully compromised an Outlook server from pivoting to other sensitive resources across your enterprise. ZWS flags these anomalies and prevents all of this activity from a compromised asset.
Of course, make sure you are also running the latest security updates from Microsoft. Patching is one of the most important foundational controls that exists.
The emergence of another high-impact zero-day threat underlines the need for a complete, policy-based zero trust architecture. When sensitive apps are not accessible on the internet—and only available through strong identity, authentication, and business policy—you’ve removed an attacker’s ability to compromise them entirely. And, if the worst happened, preventing lateral movement between applications could stop an attacker from conducting additional actions on the network.
This is a core tenet of the Zscaler platform: Users from anywhere pass through an authentication and policy layer to connect directly to the application they need without creating unnecessary network exposure. ZIA enables this secure access to SaaS apps and the open internet, while ZPA does the same for private applications, and ZWS segments and protects internal workload communications.
This zero trust architecture is critical to preventing initial compromise and to mitigating damage if an application should ever be infiltrated—which, as we’re seeing repeatedly, is a possibility for even the most trusted and widely used enterprise applications.
For more tips about implementing zero trust to protect your organization from zero-day threats like the HAFNIUM attack, check out this blog. If you’re concerned about your current attack surface, evaluate your network exposure using our Internet Attack Surface Analysis tool.





