Recent Zeus C&C activity has been observed from: mnbvicdij4uhdjb5421knnkd.com
At the time of posting, the domain is not present in ZeusTracker.
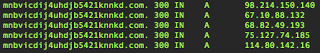
The domain is currently fluxing (Fast-Flux), notice short TTLs and numerous A records across a number of netblocks (in this case, bots):
Zeus Configuration URLs:
hxxp://mnbvicdij4uhdjb5421knnkd.com/bin/oraha.bin
hxxp://mnbvicdij4uhdjb5421knnkd.com/bin/orahxa.bin
hxxp://mnbvicdij4uhdjb5421knnkd.com/xman/xman.bin
oraha.bin = dfd46f8fdf3084984f57580fbe4f40b9
orahxa.bin = dfd46f8fdf3084984f57580fbe4f40b9
xman.bin = f27cb8327406f999fbd60d39d6ad81ea
Zeus Drop Zones:
hxxp://mnbvicdij4uhdjb5421knnkd.com/xman/gogo.php
hxxp://mnbvicdij4uhdjb5421knnkd.com/cp01/zen.php
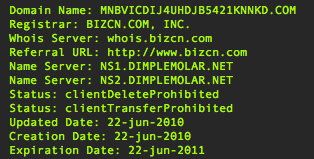
Domain Registration Information:
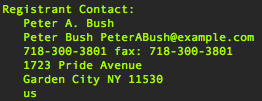
 Registrant Contact:
Registrant Contact:
 The name server domain (dimplemolar.net) has been observed providing name services for other past Zeus domains:
The name server domain (dimplemolar.net) has been observed providing name services for other past Zeus domains:
haijeihefoobeekahkohweto.com
eethahchaehiexahgeemaugh.com
ziosuovareipheighaisheek.com
Registration for the nameserver domain:
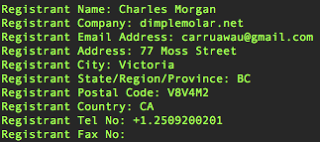
Dancho blogs related to carruawau registration information:
IRS/PhotoArchive Themed Zeus:
ns1.hourscanine.com - 87.117.245.9
Keeping Money Mule Recruiters on a Short Leash:
ns1.dimplemolar.net - 207.126.161.29
Investigating some of the IPs involved in the fluxing show that they are part of a Zeus botnet.
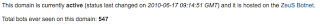
For example, DNSBL.abuse.ch shows that 98.214.150.140 resolving the domain kldmten.net which at present has had 547 bot IPs observed supporting this domain.
The botnet infrastructure supporting the fast-flux hosting and name resolution for these Zeus and money mule recruiting campaigns is related to the Avalanche botnet which has been discussed on the PhishLabs blog.
Zscaler Blog
Get the latest Zscaler blog updates in your inbox
Zeus C&C (Avalanche)
Was this post useful?
Disclaimer: This blog post has been created by Zscaler for informational purposes only and is provided "as is" without any guarantees of accuracy, completeness or reliability. Zscaler assumes no responsibility for any errors or omissions or for any actions taken based on the information provided. Any third-party websites or resources linked in this blog post are provided for convenience only, and Zscaler is not responsible for their content or practices. All content is subject to change without notice. By accessing this blog, you agree to these terms and acknowledge your sole responsibility to verify and use the information as appropriate for your needs.
Get the latest Zscaler blog updates in your inbox
By submitting the form, you are agreeing to our privacy policy.




