Security. Communication. Collaboration.
These were the three areas that companies invested in most since the beginning of last year. Don’t just take my word for it— reports from both Microsoft and Okta provide insight into the most popular enterprise applications being used to support remote work for business.
Zero trust is growing just as quickly as collaboration
For years, we have talked about the importance of zero trust for access to apps and its two key foundational elements: identity, and the use of business policies (that can adapt as needed) when it comes to securing user access to critical business services. Identity is the passport needed to determine who a specific user is (no implicit trust of IP address). Business policies are set by IT teams and determine which authorized users can access which specific applications. These policies are enforced, and the user to app connection brokered, by a zero trust exchange service. These business policies follow the user no matter where they are—at home, at their favorite cafe, their Airbnb, or back at the office (hopefully someday soon).
As employees join companies, leave companies, and devices get lost or become infected by malware etc., those business policies then automatically adapt using APIs shared across zero trust ecosystem players like Zscaler, Crowdstrike, Microsoft, Okta, and Splunk. For example, this is where our investment in SCIM 2.0 supporting Microsoft, Okta, and others, becomes incredibly useful to our customers. If an employee leaves the company, we consume that information from IDP, and use SCIM 2.0 to revoke access. We can then view logs in real-time and automatically stream them out to a SIEM server for further SOC analysis.
We purposely designed our Zscaler platform to be able to integrate with popular identity providers like Microsoft Azure Active Directory, Okta, Ping and several other SAML-based IDP solutions because we believe in the importance of zero trust within the enterprise.
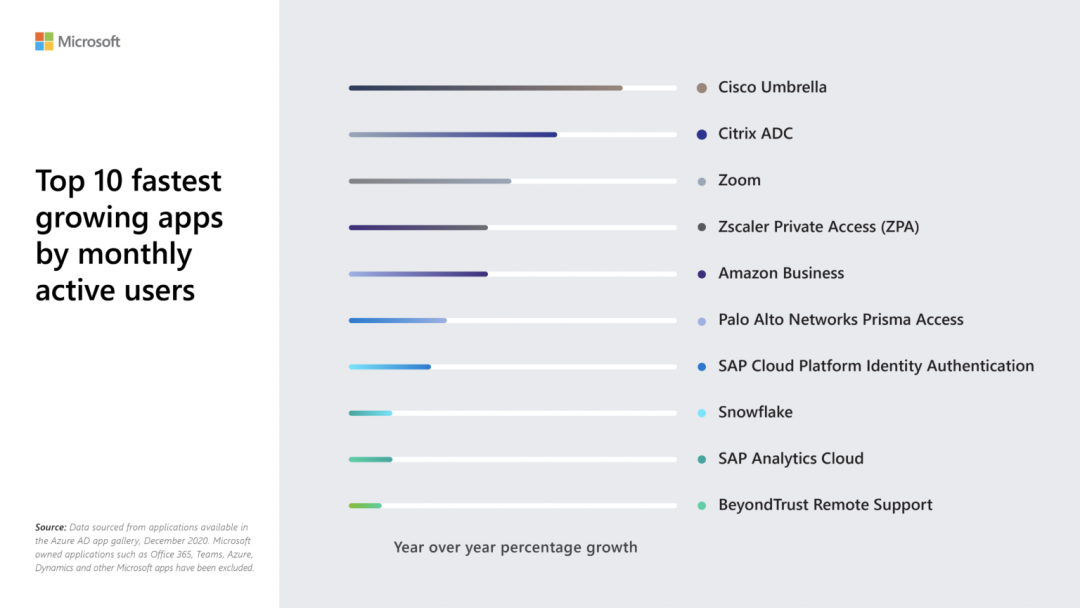
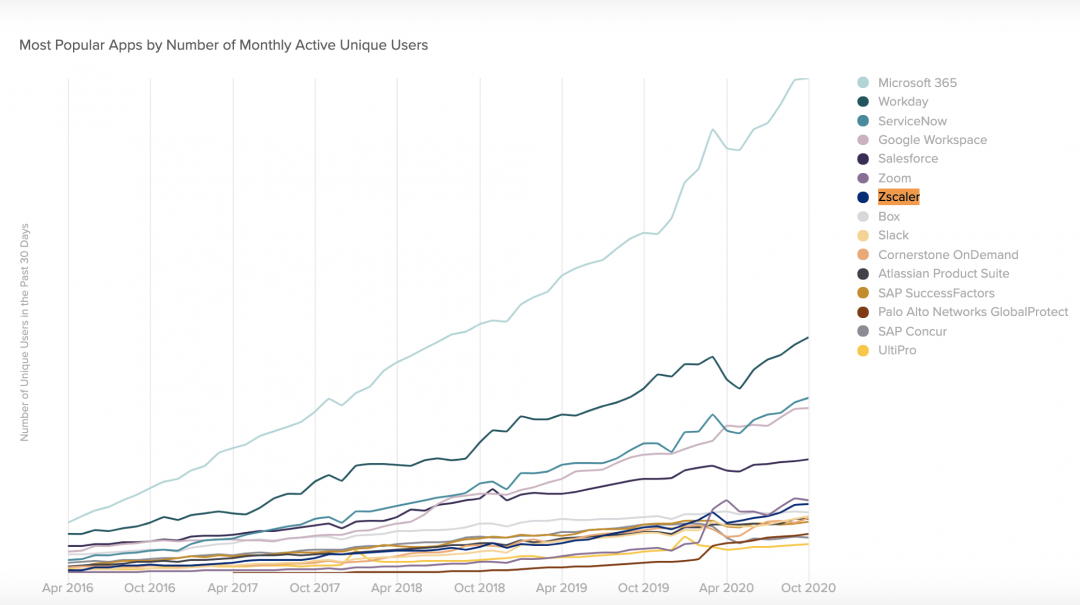
So, when I look at the findings from both Microsoft and Okta, two identity juggernauts, the most exciting sub-story that immediately jumps out to me is the fact that zero trust solutions are among the fastest-growing apps on the market–and Zscaler is one of the top solutions!
The state of apps by Microsoft identity (Zscaler is #4)
Okta Business at Work Report
Zero trust, no matter where users are
The value of adopting a zero trust strategy has become more evident than ever during COVID-19 life, but one important tip I give to customers is to not make the mistake of thinking zero trust is only valid for remote work. Many customers have told me about the prospect of building plans to support a new, hybrid workforce where employees have the ability to work two days remote and three days in the office. For many IT teams, this still remains to be seen, but whatever the case may be, it’s important to not revert back to traditional methods of connectivity that treat remote employee access to apps differently from in-office employee access, and imply trust by allowing users to connect onto the network using VPN, or simply by residing in the office. FIGHT THE URGE TO DO THIS.
I remind them that now that they’ve replaced their remote access VPN (or perhaps plan to soon) with a zero trust solution, they can also use that same zero trust solution to bring employees back to the office safely and securely. The great thing about identity and business policies are that they are omnipresent—they follow the user where they go. So why not take advantage of that? Fewer products for the customer to manage, a seamless user experience from everywhere, and, of course, zero trust access to the business services employees need—who doesn’t want that?
The mass transition to zero trust has already begun, and I am looking forward to its continued adoption within the enterprise–especially when the world begins to open back up





