Often, vulnerable sites are hacked by many groups for various purposes including spam delivery, such as Blackhat SEO, other scams, etc. Many of the sites hosting the Russian scams are now used for other malicious purposes.
Blackhat SEO
One of the parameters that is used to determine the rank of a web site in the search results is the number of links to a given page. As such, spammers take advantage of vulnerable sites by adding links to site that the attackers want to promote and these links are often hidden from visitors to the page. The most common technique used involves adding a hidden DIV tag at the end of the page. This was done on http://goingonfive.com/ for example:
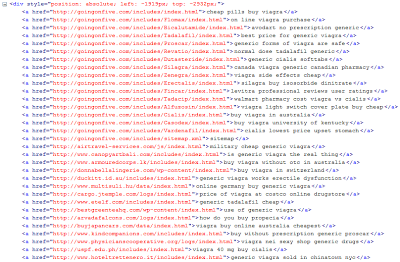 |
| Spam links |
The spam pages claim to be a "Google Pharmacy":
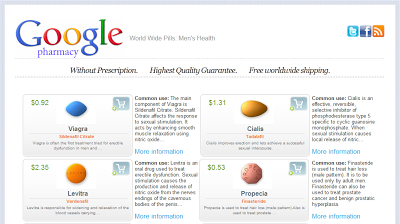 |
| http://goingonfive.com/includes/ |
The pages then link to grand-pills.com where people can order the drugs:
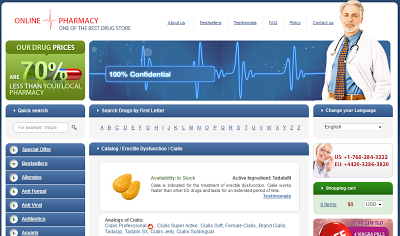 |
| http://www.grand-pills.com/catalog/Erectile_Dysfunction/Cialis.htm |
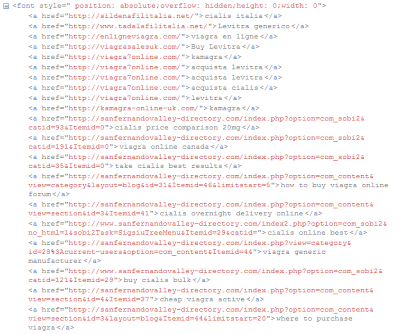 |
| Hidden spam links |
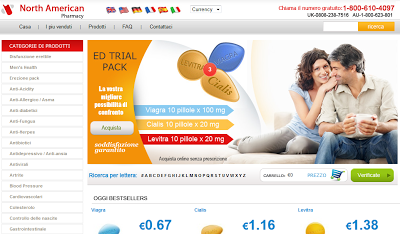 |
| Canadian Pharmacy |
American and other Russian scams
The Russian scam I reported on initially is using http://goingonfive.com/modules/mod_wdbanners/resmmdnd.php. The directory /modules/mod_wdbanners/ contains many other pages redirecting to other scams.
 |
| Pages uploaded on http://goingonfive.com/ |
Most of these pages redirect to another Russian scam at http://arhivi-familii.com/. I noticed this one about a month ago.
 |
| http://arhivi-familii.com/ |
| the service is NOT free! |
Two other pages redirect to a US scam that I detailed in an earlier post: get rich working from home, which abuses a Facebook Like widget to look legitimate.
 |
| "Work from home" scam |
These sites will probably host more and more spam and malicious content until they get added to popular denylists, at which point the hackers will move to new targets.




