Zscaler Blog
Get the latest Zscaler blog updates in your inbox
Recent DarkGate Activity & Trends
Introduction
DarkGate is a malware family, dating back to 2018, that gained prominence after the demise of Qakbot with a Malware-as-a-Service (MaaS) offering advertised in underground cybercrime forums starting in the summer of 2023. This blog examines DarkGate intrusion trends observed by ThreatLabz between June and October 2023.
Key Takeaways
- DarkGate activity surged in late September and early October 2023.
- According to our customer telemetry, the technology sector is the most impacted by DarkGate attack campaigns.
- Most DarkGate domains are 50 to 60 days old, which may indicate a deliberate approach where threat actors create and rotate domains at specific intervals.
Trend 1: DarkGate activity surges in late September, early October
To better understand DarkGate distribution trends, the ThreatLabz team analyzed hostnames, registration information, IP addresses, website content, and any recent patterns that emerged.
Increase in DarkGate domains
Our analysis revealed that there was a significant rise in the number of active DarkGate domains during the last week of September 2023. This means that more DarkGate websites associated with illegal activities were active during this specific time period.
Uptick in DarkGate transactions
DarkGate transactions increased in late September and into October. Notably, there was a substantial spike in transactions on October 10, 2023. This suggests that the threat actors behind Darkgate were particularly active during this time, possibly executing a series of attacks.
This DarkGate transaction data was compiled by observing the Zscaler cloud. Each time an infected machine made contact with a C2 server was counted as a transaction.
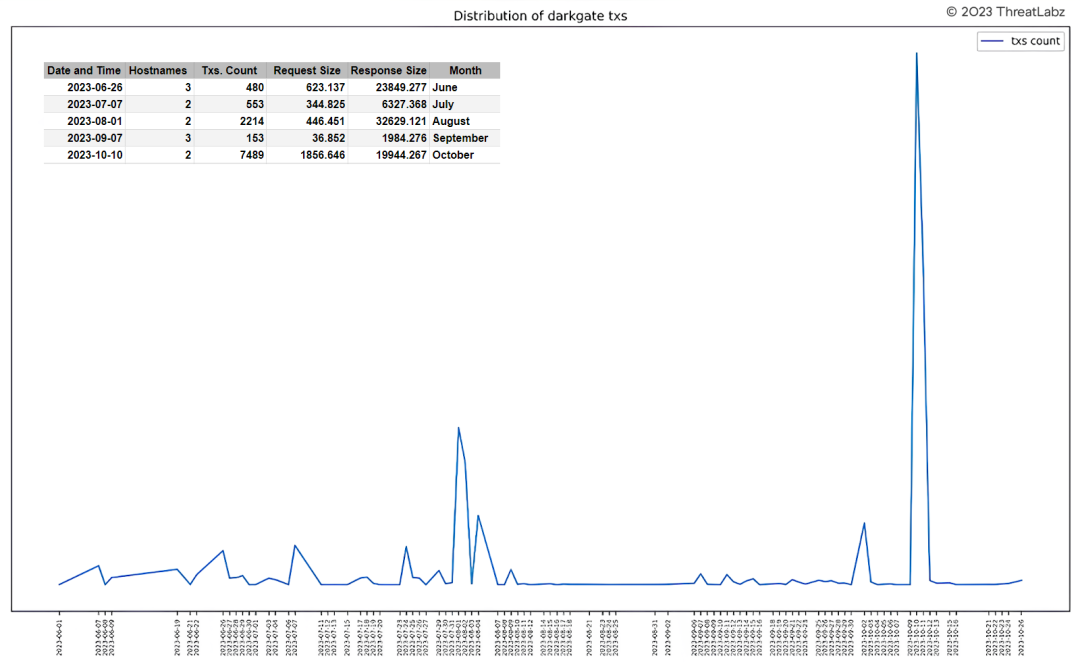
Figure 1: Illustrates spikes in DarkGate command-and-control (C2) activity by date
Trend 2: Technology sector most targeted by DarkGate
Based on analysis of our customer telemetry, the technology industry is the most targeted by DarkGate at 36.7%. Food, beverage, and tobacco come in second at 12.7%.
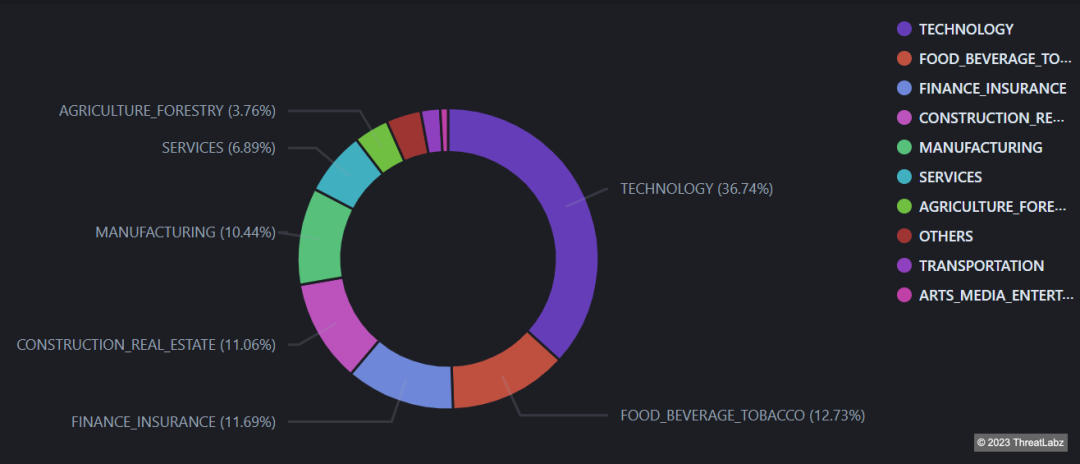
Figure 2: Industries most targeted by DarkGate
Trend 3: Most DarkGate domains are 50 to 60 days old
ThreatLabz found a concentrated level of activity (such as serving websites, handling transactions, or participating in network communications) among hostnames that have been in existence for 50-60 days. The fact that DarkGate domains follow this pattern could indicate that threat actors are taking a systematic approach where they create and rotate domains at specific intervals. Most likely, this intentional pattern perpetrated by threat actors is a way of evading security measures that target known malicious domains.
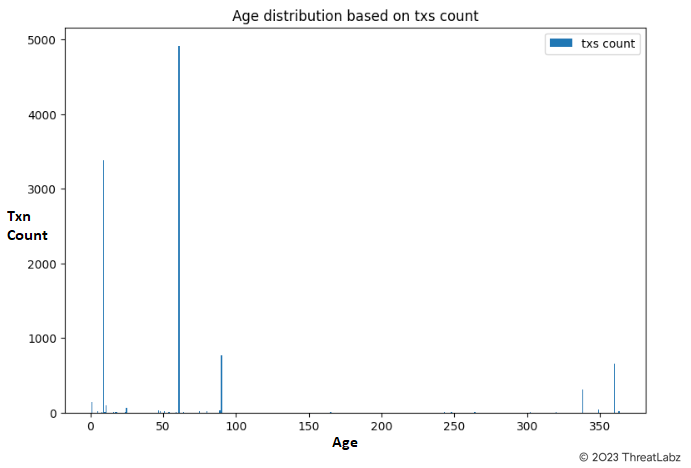
Figure 3: Age distribution of DarkGate domains based on transaction volume
Conclusion
The recent surge in DarkGate's activity can be attributed to its use as a replacement for Qakbot. In addition to staying on top of the threat of DarkGate malware, Zscaler's ThreatLabz team continuously monitors for new and emerging threats and shares its findings with the wider security community.
Zscaler Coverage & Indicators of Compromise (IOCs)
Zscaler's multilayered cloud security platform detects indicators related to DarkGate at various levels. Zscaler Sandbox played a particularly crucial role in analyzing the behavior of various files. Through this sandbox analysis, the threat scores and specific MITRE ATT&CK techniques triggered were identified, as illustrated in the screenshot provided below. Zscaler’s advanced threat protection capabilities and comprehensive zero trust approach empowers cybersecurity professionals with critical insights into malware behavior, enabling them to effectively detect and counter the threats posed by malicious actors.
- Win64.Downloader.DarkGate
- Win32.Trojan.DarkGate
- Win64.Trojan.DarkGate
- LNK.Downloader.DarkGate
- VBS.Downloader.DarkGate
- JS.Downloader.DarkGate
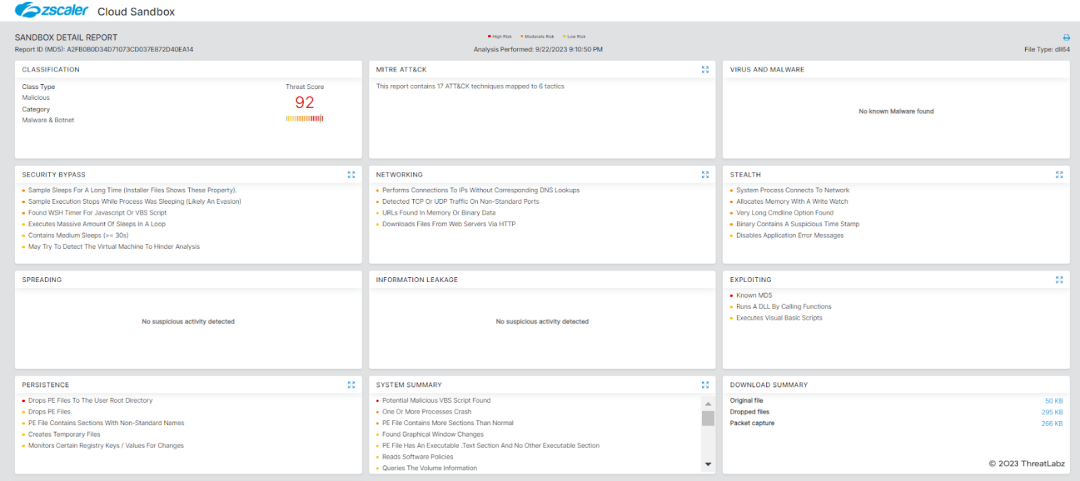
Figure 4: Zscaler Cloud Sandbox
MITRE ATT&CK TTP’s
| Tactic | Technique ID | Technique ID |
|---|---|---|
| Initial Access | T1566 | Phishing |
| Execution |
| |
| Persistence | T1547 | Boot or Logon Start Execution |
|
Defense Evasion |
| |
|
Credential Access
| T1555.003 |
Credentials from Web Browsers
|
| Discovery |
| |
| Command and Control | T1071 | Application Layer Protocol |
Indicators of Compromise (IoCs)
- Phishing PDF: 55f16d7f0a1683f32b946c03bdda79ca
- Malicious DLL: a2fb0b0d34d71073cd037e872d40ea14
- Encoded AutoIt Script: 0ea7d1a7ad1b24835ca0b2fc6c51c15a
- AutoIt Loader Benign: c56b5f0201a3b3de53e561fe76912bfd
- DarkGate Payload: f242ce468771de8c7a23568a3b03a5e2
- Malicious ZIP: d2efccdb50c7450e8a99fec37a805ce6
- LNK File: 7791017a97289669f5f598646ef6d517
- Phishing PDF: 803103fe4b32c86fb3f382ee17dfde44
- Malicious ZIP: 0a341353e5311d8f01f582425728e1d7
- VBS File: 3df59010997ed2d70c5f7095498b3b3f
- Encoded AutoIt Script: 660bc32609a1527c90990158ef449757
- AutoIt Loader Benign: c56b5f0201a3b3de53e561fe76912bfd
- DarkGate Payload: 9bf2ae2da16e9a975146c213abd7cd4f
- Malicious ZIP: 9f93952e425110de34e00ebd6d6daab3
- VBS File: c78dfe0f9b4fd732c8e99eb495ed9958
- Encoded AutoIt Script: 660bc32609a1527c90990158ef449757
- AutoIt Loader Benign: c56b5f0201a3b3de53e561fe76912bfd
- DarkGate Payload: 9bf2ae2da16e9a975146c213abd7cd4f
- Malicious ZIP: 54e65e96d2591106a2c41168803c77ff
- JS File: 57cfc3b0b53e856c78b47867d7013516
- Phishing Email: 0a50d4ea1a9d36f0c65de0e78eacbe95
- PDF document: 097cbe9af6e66256310023ff2fbadac6
- Malicious CAB File: 6ecd98dfd52136cff6ed28ef59b3f760
- MSI File: 8ef6bc142843232614b092fac948562d
- CAB file dropped from MSI: a169cebb4009ecfb62bb8a1faf09182f
Command-and-control (C2)
- luxury-event-rentals[.]com
- drvidhya[.]in
- alianzasuma[.]com
- cpm.com[.]py
- corialopolova[.]com
- skylineprodutora[.]com.br
- medsure[.]com.br
- humanrecruitasia[.]com
- journeotravel[.]com
- skylineprodutora.com[.]br
- ahantadevnet[.]org
- yellowstone[.]com.mm
- asiaprofessionals[.]net
- axecapital[.]ro
- semquedagotas[.]com.br
- reverasuplementos[.]fun
- tikwave[.]site
- grupec[.]com.co
- chatpipoca[.]net
- ncsinternationalcollege[.]com
- gatraders.com[.]pk
- ibuytech[.]pk
- winstonandfriendz[.]ca
- skincaremulher[.]fun
- adam-xii-rpl.my[.]id
- mycopier.com[.]my
- japaaesthetics[.]com
- msteamseyeappstore[.]com
- youth[.]digital
- roundstransports[.]com
- mfleader.com[.]ar
- fefasa[.]hn
- nile-cruiise-egypt[.]com
- flyforeducation[.]com
- expertaitalia[.]eu
- plataformaemrede[.]com.br
- runnerspacegifts[.]com/umn/
- kiwifare[.]net
- getldrrgoodgame[.]com
- hmas[.]mx
- darkgate[.]com
- 5.188.87.58
- 5.42.77.33
- 45.144.28.244
- 94.228.169.123
- 94.228.169[.]143[:]2351/
- 94.228.169[.]143[:]8080/
- 66.42.110.147
- 94.131.106.78
- 88.119.175.245
- 45.32.222.253
- grupowcm[.]com[.]br
- thekhancept[.]com
- eelontech[.]com
- bligevale[.]co[.]zw
- dhtech[.]ae
- techs[.]com
- gsrhrservices[.]com
- glowriters[.]com
- a2zfortextile[.]com
- alpileannn[.]com
- boutiquedhev[.]com
- hypothequeswestisland[.]com
- onetabmusic[.]com
- sirishareddy[.]info
- appapi[.]store
- sictalks[.]com
- nia-dbrowntestserver[.]com[.]ng
- ofc[.]ai
- unasd[.]org
- plusmag[.]ro
- beautifullike[.]com
- gsrglobal[.]org
- winstonandfriendz[.]ca
- divinfosystem[.]com
- supershuttles[.]co[.]za
- ziaintegracion[.]com
- themarijuanashow[.]com
- blackshine[.]lk
- deroze[.]net
- vtektv[.]com
- dna-do-gamer[.]com
- kalismprivateltd[.]co[.]uk
- arshany[.]com
- kelotecnologia[.]com
- millennialradio[.]es
- phomecare.co.uk
Was this post useful?
Disclaimer: This blog post has been created by Zscaler for informational purposes only and is provided "as is" without any guarantees of accuracy, completeness or reliability. Zscaler assumes no responsibility for any errors or omissions or for any actions taken based on the information provided. Any third-party websites or resources linked in this blog post are provided for convenience only, and Zscaler is not responsible for their content or practices. All content is subject to change without notice. By accessing this blog, you agree to these terms and acknowledge your sole responsibility to verify and use the information as appropriate for your needs.
Get the latest Zscaler blog updates in your inbox
By submitting the form, you are agreeing to our privacy policy.



