Search Engine Security (SES), a browser extension designed to protect users against Blackhat SEO links in search engines, is now available for Internet Explorer. You can download it from our website. It is compatible with Internet Explorer 6.0 and above, on Windows XP thru Windows 7.
The features are the same as Search Engine Security for Google Chrome, released two weeks ago. The Referer and the User-Agent headers are modified when you follow a search result link on Google, Bing and Yahoo! This prevents the hijacked sites from redirecting users to a malicious page.
As with SES for Firefox and Google Chrome, you can turn the extension on and off for the three search engines.
You can also whitelist specific pages. The only difference with the IE version as opposed to Firefox and Chrome is that the Referrer cannot be empty. This is why the default value is "-".
The options are available under Tools > Search Engine Security options.
To test the features, search for "what is my user agent" or "what is my referrer" in Google, Bing or Yahoo! and follow a link. You will notice a different value when Search Engine Security is ON or OFF.
There are very few browser extensions available for Internet Explorer, especially extensions helping to keep users safe. I will continue to port the Zscaler security extensions to Internet Explorer and will bring other security tools to this platform.
You can find a full list of all our browser extensions on the ThreatLabZ portal under Tools. Search Engine Security for Internet Explorer can be downloaded here.
The features are the same as Search Engine Security for Google Chrome, released two weeks ago. The Referer and the User-Agent headers are modified when you follow a search result link on Google, Bing and Yahoo! This prevents the hijacked sites from redirecting users to a malicious page.
As with SES for Firefox and Google Chrome, you can turn the extension on and off for the three search engines.
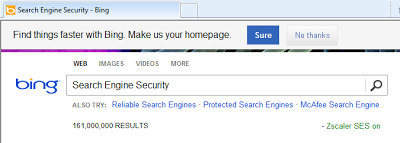 |
| Search Engine Security enabled on Bing |
You can also whitelist specific pages. The only difference with the IE version as opposed to Firefox and Chrome is that the Referrer cannot be empty. This is why the default value is "-".
The options are available under Tools > Search Engine Security options.
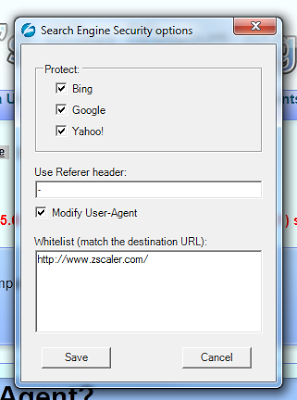 |
| Search Engine Security options |
To test the features, search for "what is my user agent" or "what is my referrer" in Google, Bing or Yahoo! and follow a link. You will notice a different value when Search Engine Security is ON or OFF.
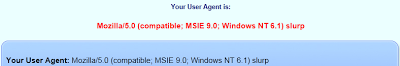 |
| Modified User-Agent |
You can find a full list of all our browser extensions on the ThreatLabZ portal under Tools. Search Engine Security for Internet Explorer can be downloaded here.





