A cloud-native application protection platform (CNAPP), is a suite of security tools that enable developers and security teams in any enterprise to identify, prioritize, and remediate security, legal, and compliance risks (in Cloud, Containers, Clusters, and Code) across the development lifecycle, from the build phase, all the way through to production operations.
The growth of cloud-native applications introduces security challenges
The rapid growth of the digital economy fostered the adoption of microservices architectures, cloud, and container technologies across nearly every product engineering team. This introduced new technology vectors and digital assets in an organization, all of which is dynamic and highly automated. This introduction of new technologies has added complexity and process challenges to information security teams seeking to protect digital assets.
To solve these challenges, security teams turned to the industry and the industry responded with a broad range of commercial and open source cloud security tools like CSPM, CIEM, Container security, KSPM (Kubernetes security posture management), IaC (Infrastructure as code), and SCA (open source vulnerabilities) to analyze the risk posture and keep the platforms secured and compliant.
Leveraging so many tools in large-scale cloud-native deployments means complexity and overhead. Each tool generates numerous alerts that must be triaged, prioritized, assigned, and responded to. Each tool must be integrated with other tools in the enterprise including Version Control Systems, CI/CD Tools, IDEs, ticketing systems, and more. And managing the overhead of operationalizing each tool means that product engineering teams have less time to focus on their core roles, reducing the velocity of application development.
The solution: a CNAPP platform
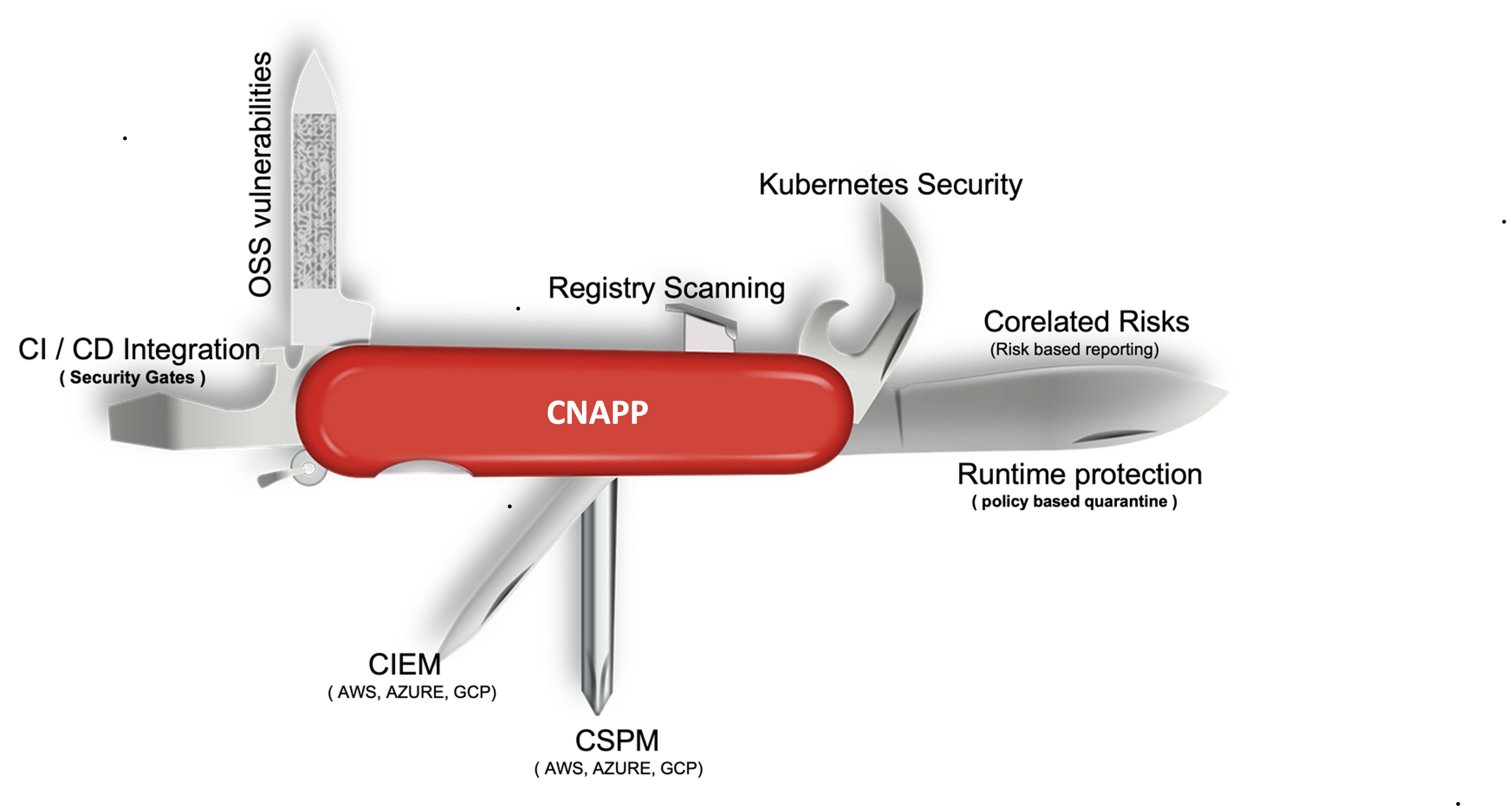
A CNAPP can scan, detect, track, monitor, correlate, and remediate different types of security and compliance issues, consolidating several point products into a single, powerful platform. CNAPPs work across cloud providers (AWS, GCP, Azure, etc.), covering all services (IAM, VMs, containers, serverless functions), container orchestrators like Kubernetes, infrastructure-as-code (IaC) tools such as Terraform and CloudFormation, container registries, open-source vulnerabilities, application binaries their licenses and cloud entitlements. Importantly, these platforms are built to correlate across several areas to find the combinations of weaknesses that represent the greatest risk to the enterprise, prioritizing those areas to cut down on alert fatigue and help product engineering teams maximize efficiency so they can focus on developing products, not fixing security issues.
CNAPP is a powerful suite that can protect any cloud-native application and assets by enabling security from build to runtime. A single pane of glass that empowers developers and security professionals to support speed and agility.
Why CNAPP is important for security leaders:
CNAPP provides a consolidated set of tools to proactively protect cloud-native applications and assets. In other words, it's a Swiss Army knife for security teams to proactively protect and remediate security and compliant risk in cloud-native applications and assets at the early stages and runtime. CNAPP helps with:
Projecting real risks: CNAPP consolidates multiple tools into one platform and correlates the alerts from various sources to project the real risks that have to be remediated by the security and development teams.
Defining security and compliance guardrails: CNAPPs can enable security engineers to define security and compliance guardrails for cloud-native applications and assets as policies.
Integration with CI and CD platforms: CNAPPs can seamlessly integrate at every stage of the SDLC and toolsets to ensure defined security gates are validated and passed. This extensive integration with Version Control Systems, container registries, and CI/CD tools will help both Developers, and DevOps prevent major security or compliance risks of accidentally deploying non-compliant resources into customer-facing portals, platforms, and APIs.
Protection at early stages: The major advantage of a CNAPP is not only to identify and report issues as early in the SDLC as possible, but to also give the right set of guidance to remediate the identified risks that can lead to major exploitation of the customer's digital asset.
Runtime protection: CNAPP also provides runtime protection with the ability to contain or quarantine the identified zero-day exploit or vulnerability during runtime in the cloud, container, or clusters before an actual fix can be applied via the developers using the DevSecOps pipeline ( e.g., the ability to quarantine the containers prone to log4j exploit while the developers are testing and fixing the code for log4j vulnerability).
Conclusion
A CNAPP provides security professionals with the ability to define security guardrails that enable close collaboration with developers and DevOps to build and run secure cloud-native applications. These Swiss Army Knives maximize risk reduction while reducing complexity and improving development efficiency. As an added bonus, if you’re in a pinch, you can use the corkscrew to open a nice bottle of Cabernet.
Interested in exploring more about CNAPP? Talk to our experts.




