Zscaler Blog
Get the latest Zscaler blog updates in your inbox
Turbocharge Your BYOD or B2B Initiatives with Secure Agentless Experience
Data breaches are on a tear, and continue to skyrocket. Their impact is huge, with hefty costs to organizations across all the major verticals. In deconstructing this rise in these data breaches, two key statistics jump out:
- 54% of organizational breaches occurred through B2B (business-to-business)/third-party access via external partners and contractors working on unmanaged devices.
- 71% of surveyed professionals leveraging BYOD (bring your own device), store sensitive work information on personal devices, and 43% of those devices have been targeted with work-related phishing attacks.
Double-clicking on these stats provide a user-centric view.
User-Centric View (requirements)
Third-party users, like contractors who may work with multiple organizations, love their independence and want the freedom to be able to use the same (unmanaged) device to service multiple end clients. Similarly, remote or hybrid employees wish to be super productive on their own device, enjoying BYOD flexibility.
To optimize experience for these users, the top requirement is to not install any specialized agents, and let the device be unmanaged.
IT-Centric View (challenges)
IT lacks control over unmanaged devices, creating business risks. So, enterprises need to prevent data exfiltration and protect applications while gaining full visibility.
SaaS adoption can further complicate matters, taking control away from IT. Not to mention, typical access methods may break content (CASB reverse proxy) as well as restrict access to a limited set of SaaS apps.
To support application access on unmanaged devices, organizations often use VDI (Virtual Desktop Infrastructure). Recently, the shortcomings of VDI have become clear—it doesn’t scale as it’s costly and complex while requiring an endpoint agent to install and manage. Moreover, increasingly the modernized applications are web or browser-based, and streaming an entire desktop via VDI doesn’t make for a very good end user experience.
Introducing the Zscaler Approach: A Secure, Agentless Experience
With Zscaler, end users authenticate into a portal for a dashboard view of their sanctioned SaaS and private web apps, without the need for an endpoint agent or forcing them to use anything but their favorite browser. This is because app access is provided through Zscaler Browser Isolation running under the hood, creating an isolated browser instance within an ephemeral cloud container that sends all traffic through the natively integrated policies and controls of the Zscaler Zero Trust Exchange. With this platform, users enjoy a managed device experience and security through whichever device they please.
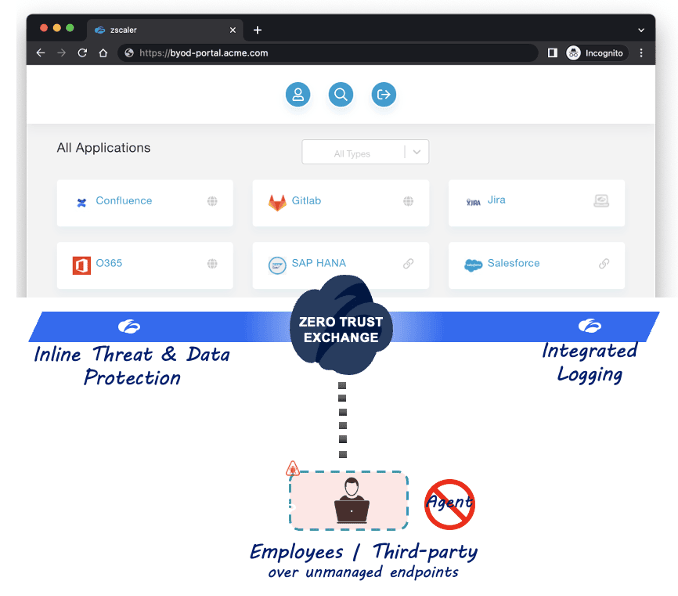
Zscaler Browser Isolation streams experience-optimized pixels back to the user’s device without sending the actual data, enforcing clipboard or read-only controls, restricting upload/download and print options, and providing watermarking etc. capabilities. Using file isolation capability and built-in document processing technology, users can view docs or share files (across apps, both SaaS and private, as per the policy) without having to download those to their unmanaged device. The integrated Zscaler DLP (Data Loss Prevention) suite provides comprehensive data protection, and all traffic goes through full inline inspection and security policy enforcement via the Zero Trust Exchange, while integrated logging provides deeper visibility.
Access to SaaS apps is provided uniquely and seamlessly. Some apps may use legacy authentication methods, but the Zscaler architecture can still ensure MFA (multi factor authentication), so you can adhere to your organization’s security standards. Moreover, users have the flexibility to access apps from any device, be it from a desktop, touch-screen laptop, or even mobile.
This architecture also provides application protection. Private web apps are hidden from the internet by the Zero Trust Exchange, reducing their attack surface. Moreover, Isolation obfuscates the application headers and hides away the application’s anatomy, (protocol, OS versions, software components, etc.), further shrinking the attack surface by stopping attackers from using malware-infected, unmanaged devices to exploit these apps.
Depending on the use case requirements, Zscaler Browser Access can provide native (non-isolated) access to these apps, as well. Leveraging Zscaler Privileged Remote Access, users can also access internal servers, desktops, jump hosts, and other OT/IT/IoT devices via a web-based RDP/VNC/SSH mechanism through the portal. As per policy configuration, access to systems and devices can be restricted for a specific timeframe. Plus, with session recording capability, admins can perform detailed audits through video recordings and gain deeper insight into the user behavior patterns
Zscaler SSE platform
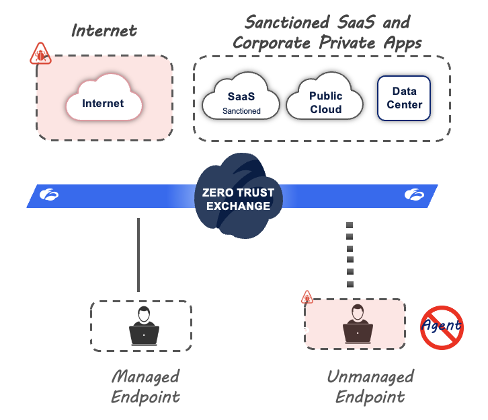
Holistically, the Zscaler SSE (Secure Services Edge) platform provides secure access for both managed and unmanaged devices.
Get started on your BYOD or B2B journey now!
In a nutshell, Zscaler respects an end user’s ideal of keeping their device unmanaged, without requiring an endpoint agent, turbocharging your organization’s BYOD and B2B initiatives.
Drop us a line for a quick demo, or sign up for a workshop! We will guide you on your zero trust journey, so you can boost user productivity without compromising security, and accelerate your innovation path. Experience the One True Zero!
Fun Fact - BYO has origins as BYOB and it’s suggested that in the early 19th century BYOB was a societal term for “Bring Your Own Basket” at picnics.
Was this post useful?
Disclaimer: This blog post has been created by Zscaler for informational purposes only and is provided "as is" without any guarantees of accuracy, completeness or reliability. Zscaler assumes no responsibility for any errors or omissions or for any actions taken based on the information provided. Any third-party websites or resources linked in this blog post are provided for convenience only, and Zscaler is not responsible for their content or practices. All content is subject to change without notice. By accessing this blog, you agree to these terms and acknowledge your sole responsibility to verify and use the information as appropriate for your needs.
Get the latest Zscaler blog updates in your inbox
By submitting the form, you are agreeing to our privacy policy.




