Overview
Malvertising, or "malicious advertising," is not a new threat, and just a few weeks into 2016 ThreatLabZ has observed a malvertising campaign injecting iframes into banner advertisements that lead to Angler Exploit Kit. Surprisingly, the Angler operators took some vacation for the New Year, as noted by F-Secure, and have only recently resumed operations, so we were surprised to see a malvertising campaign so soon after their break.This post will detail aspects of this campaign, and there is a reference list of indicators at the end of this post.
OpenX/OpenAds and Malvertising
OpenAds, now called OpenX or Revive Adserver, is an advertisement platform with a long history and is still quite popular. From a high level, when a user browses to a website using OpenAds for serving advertisements, small code stubs make requests to the OpenAds server, which decides which banner advertisement to run and sends the banner ad plus some tracking code back to the page. The banner advertisements usually rotate on some interval, and a single ad server can serve and control advertisements for multiple domains.Unfortuantely, the nature of banner advertisements makes them highly lucrative for criminal groups since injecting malicious content into an advertisement can impact hundreds or thousands of sites. This particular campaign impacted multiple OpenAds/OpenX servers which affected hundreds of domains. Intermediary sites were used as an additional hop prior to serving the Angler landing page, and only six second-level intermediary domains were observed, each using dozens of different subdomains and URIs. All six second-level intermediary domains share music-themed names:
- everyoneismusical.com
- musik4fingersonthemove.com
- musik4littlefingers.com
- youaremusical.com
- youaremusicalforms.com
- youaremusik.com
Interestingly, these intermediary domains only use two different IPs for all the subdomains, and the operators appear to have changed hosts suddenly. Figure 1 shows the number of hits we captured for these two IPs.
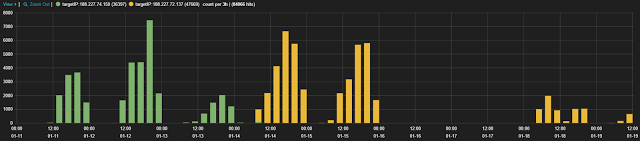 |
| Fig 1: Hits on Intermediary Domain IPs |
iframe Trampolining
The infection cycle starts with a malicious iframe injected in the banner advertisement code that references an intermediary URL. The injected iframe loads transparently, and the intermediary domain server will respond in one of the following three ways:- Response code 200 - iframe to Angler Exploit Kit landing page
- Response code 204 - no content
- Response code 404 - fake 'not found' page
 |
| Fig 2: Overview of Infection Cycle |
Infection Cycle
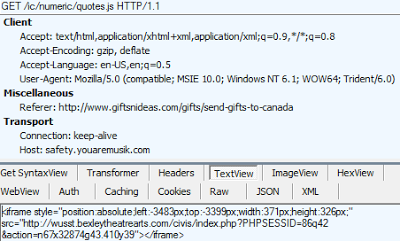
Looking at a full infection cycle in Figure 3, the benign domain 'giftsnideas.com' loads a banner ad with OpenX which contains an injected iframe to the trampoline domain. The trampoline domain's iframe finally sends the user to the Angler landing page. In this instance, the exploit failed, so no further content was loaded.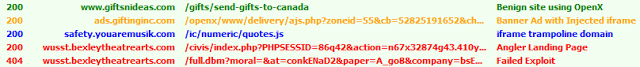 |
| Fig 3: Relevant URLs for Exploit Cycle |
 |
| Fig 4: Advertisement with Injected iframe |
 |
| Fig 5: Trampoline Header and Response |
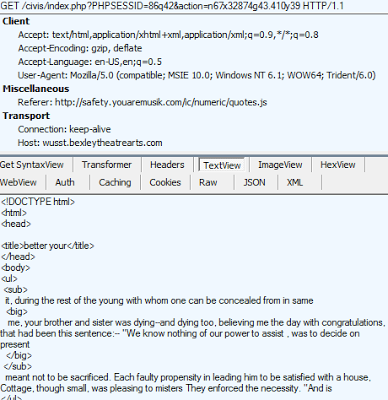 |
| Fig 6: Angler Landing Page |
Conclusion
Malvertising continues to be a highly effective means of targeting and compromising a large number of victims, and we expect this trend to continue for 2016. We noted that many of the victim sites we observed in this campaign were radio stations and auto enthusiast forums. Domains in these two groups are owned by Saga Communications and Autoforums.com, so it's likely that each uses a small number of ad servers to power the entire network of sites. ThreatLabZ will continue to monitor this campaign.Indicators
| # Hits | Second Level Domain | Registrar | Registrant |
|---|---|---|---|
| 23883 | youaremusik.com | GODADDY | Mark Lippman |
| 20681 | musik4fingersonthemove.com | GODADDY | Mark Lippman |
| 16878 | everyoneismusical.com | GODADDY | Michael Lippman |
| 16849 | musik4littlefingers.com | GODADDY | Mark Lippman |
| 5698 | youaremusical.com | GODADDY | Michael Lippman |
| 1619 | youaremusicalforms.com | GODADDY | Michael Lippman |
URL IPs
188.227.72.137 - IT-Grad nets - AS48096188.227.74.150 - IT-Grad nets - AS48096
List of FQDNs and URLs
Counts and FQDNs - via Pastebin (http://pastebin.com/7vSYi2uz)
URLs - via Pastebin (http://pastebin.com/QN9WqzPn)
Whois Samples
Domain Name: MUSIK4LITTLEFINGERS.COMRegistry Domain ID: 1916653940_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: http://www.godaddy.com
Update Date: 2015-04-05T16:22:42Z
Creation Date: 2015-04-05T16:22:42Z
Registrar Registration Expiration Date: 2018-04-05T16:22:42Z
Registrant Name: Mark Lippman
Registrant Organization:
Registrant Street: 4 Cloverbrooke Court
Registrant City: Potomic
Registrant State/Province: Maryland
Registrant Postal Code: 20854
Registrant Country: US
Registrant Phone: +1.2404294083
Registrant Phone Ext:
Registrant Fax: +1.1
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: Mark Lippman
Admin Organization:
Admin Street: 4 Cloverbrooke Court
Admin City: Potomic
Admin State/Province: Maryland
Admin Postal Code: 20854
Admin Country: US
Admin Phone: +1.2404294083
Admin Phone Ext:
Admin Fax: +1.1
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: Mark Lippman
Tech Organization:
Tech Street: 4 Cloverbrooke Court
Tech City: Potomic
Tech State/Province: Maryland
Tech Postal Code: 20854
Tech Country: US
Tech Phone: +1.2404294083
Tech Phone Ext:
Tech Fax: +1.1
Tech Fax Ext:
Tech Email: [email protected]
Name Server: NS67.DOMAINCONTROL.COM
Name Server: NS68.DOMAINCONTROL.COM
Domain Name: EVERYONEISMUSICAL.COM
Registry Domain ID: 1917710979_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: http://www.godaddy.com
Update Date: 2015-06-04T12:18:00Z
Creation Date: 2015-04-08T19:34:50Z
Registrar Registration Expiration Date: 2018-04-05T11:59:59Z
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.4806242505
Domain Status: clientTransferProhibited http://www.icann.org/epp#clientTransferProhibited
Domain Status: clientUpdateProhibited http://www.icann.org/epp#clientUpdateProhibited
Domain Status: clientRenewProhibited http://www.icann.org/epp#clientRenewProhibited
Domain Status: clientDeleteProhibited http://www.icann.org/epp#clientDeleteProhibited
Registry Registrant ID:
Registrant Name: Michael Lippman
Registrant Organization:
Registrant Street: 4 Cloverbrooke Court
Registrant City: Potomic
Registrant State/Province: Maryland
Registrant Postal Code: 20854
Registrant Country: US
Registrant Phone: +1.2404298083
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: Michael Lippman
Admin Organization:
Admin Street: 4 Cloverbrooke Court
Admin City: Potomic
Admin State/Province: Maryland
Admin Postal Code: 20854
Admin Country: US
Admin Phone: +1.2404298083
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: Michael Lippman
Tech Organization:
Tech Street: 4 Cloverbrooke Court
Tech City: Potomic
Tech State/Province: Maryland
Tech Postal Code: 20854
Tech Country: US
Tech Phone: +1.2404298083
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: NS37.DOMAINCONTROL.COM
Name Server: NS38.DOMAINCONTROL.COM





