Last week we announced support for log streaming in Zscaler Private Access (ZPA), our cloud service that delivers secure remote access to internal applications. The log streaming service allows you to automatically stream user activity, user authentication and connector logs to your SIEM provider. You can then view them within your SIEM to analyze, identify and remediate as needed.
Pro-tip: By default, ZPA streams logs for all users, but you can define policies to stream logs for specific users, applications or error scenarios.
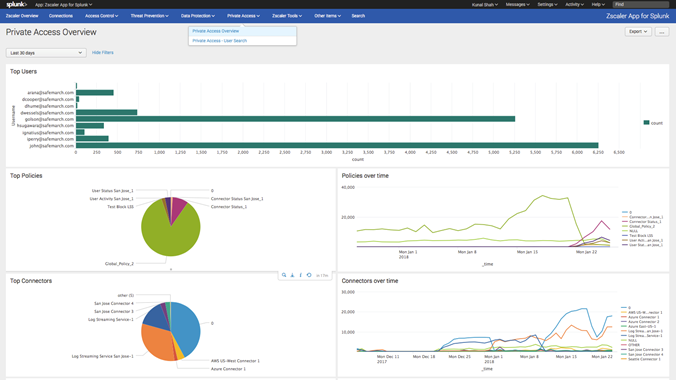
More visibility, more actionable intelligence
With real time streams, ZPA provides a better understanding of users, their locations as well as travel patterns. It provides you with data so that you can answer important questions like, “Are users connecting from a suspicious location?” The log streaming services can also help IT admins identify if a single user is active in multiple geographic locations, which could be a sign of nefarious activity. With ZPA you'll be able to identify users with potentially compromised credentials and reduce risk.
ZPA identifies and displays applications that are accessed through specific connectors. So, when you see a user accessing an application in a location where you had no idea something was even hosted, its probably time to call that user! In addition, ZPA notifies you when it discovers access to new applications or from new user devices.
Applications can now be closest to the users who need them
As a ZPA Administrator, you will be able to ensure that your users are connecting to the closest instance of enterprise applications.
By streaming ZPA logs to a SIEM, you will be able to make decisions that improve end user experience. Log streaming takes out the guess work when answering questions from leadership such as, “Is it time to bring up apps in additional locations?,” or “Do we need to add hosting capacity at this R&D site?”
Identify anomalous activity, remediate attacks faster
With ZPA, you can stream logs for policy blocks tied to specific applications. By configuring alerts in your SIEM, you can identify potentially undesirable user behavior. By analyzing logs streamed from policy blocks, you can conclude if your application access policies are too broad or just right. Such analysis can kick start the discussion around application segmentation.
Zscaler customers have come to rely on ZPA for not only securing access to internal applications but as a fundamental tool for implementing application segmentation.
The connection between IT admins and IT environment just got stronger
Setting up streaming of user and connector logs from your ZPA instance to a SIEM enables you to build powerful visuals and trend charts. With better tools, you can observe latency trends for applications in specific locations, and drill into connections between end user, ZENs, connectors and your enterprise applications.
Streaming connector status logs can also help the IT Operations teams with connector management. As opposed to treating the connector VM as a black box, Operations teams are leveraging connector status logs for real time stats related to throughput and compute utilization. This visibility provides specific data points in discussions related to connector capacity planning and lifecycle management.
Let the streaming begin!
To learn more about Zscaler Private Access and its new log streaming feature, be sure to request a demo.






