Introduction
March Madness is officially upon us, with the last games of the round of 64 taking place today. As is usual with events that have such a level of interest, bad actors across the internet will be trying to get their cut of the action through topical spam advertising and phishing as well as search engine poisoning to draw ad revenue and in some cases, deliver malicious software. Though it is still early in the cycle of March Madness interest, we have seen a bit of everything: malware purporting to be NCAA bracket templates, a rash of ad-filled sites running March Madness related SEO campaigns, and the usual complement of shady streaming sites promising live streams of the tournament games (with some delivering a nasty surprise).
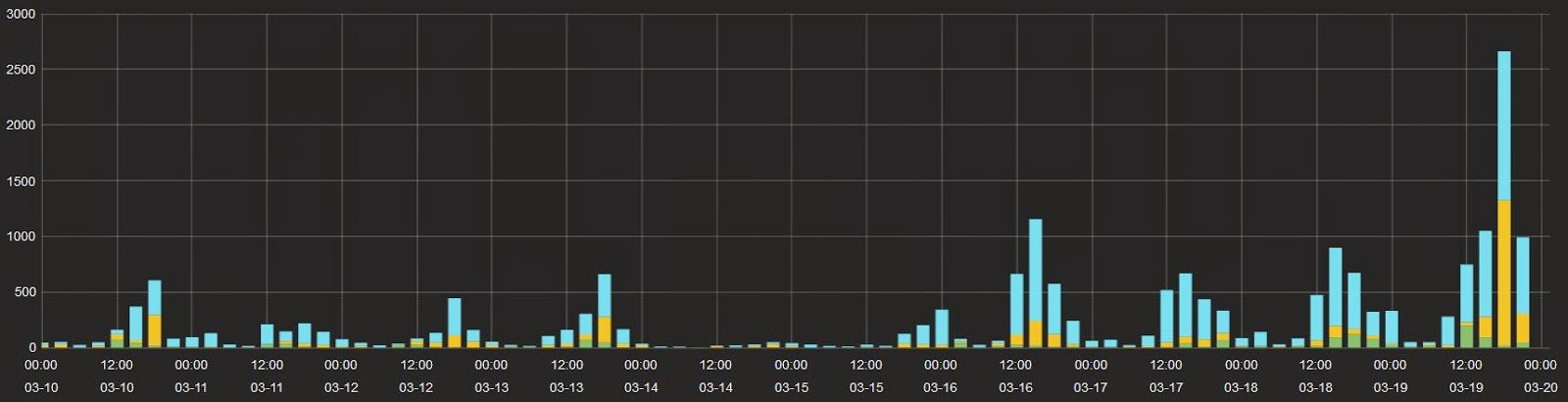 |
| NCAA Tournament related traffic shows a sharp uptick as the games began. |
NCAA Bracket Download Leads to Malware
While reviewing some of the tournament-related security blocks, we spotted an interesting file download attempt. It's not clear if the original click was derived from a search, but the primary link purports to be a zipped PDF file that can be used to create personalized brackets. The link ultimately directs to an unwanted EXE signed by the Ukranian publisher BERSHNET LLC (whose history is well documented on HerdProtect).
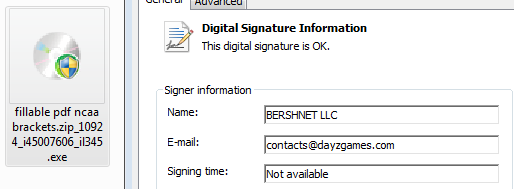 |
| The downloaded file features a valid Authenticode Certificate. |
The binary features an unusual number of protections against analysis for what appears to be simple adware. At this time, we have not fully explored the capabilities of the binary, but analysis shows that the sample gathers system information and sends it to a CloudFlare-hosted command & control server.
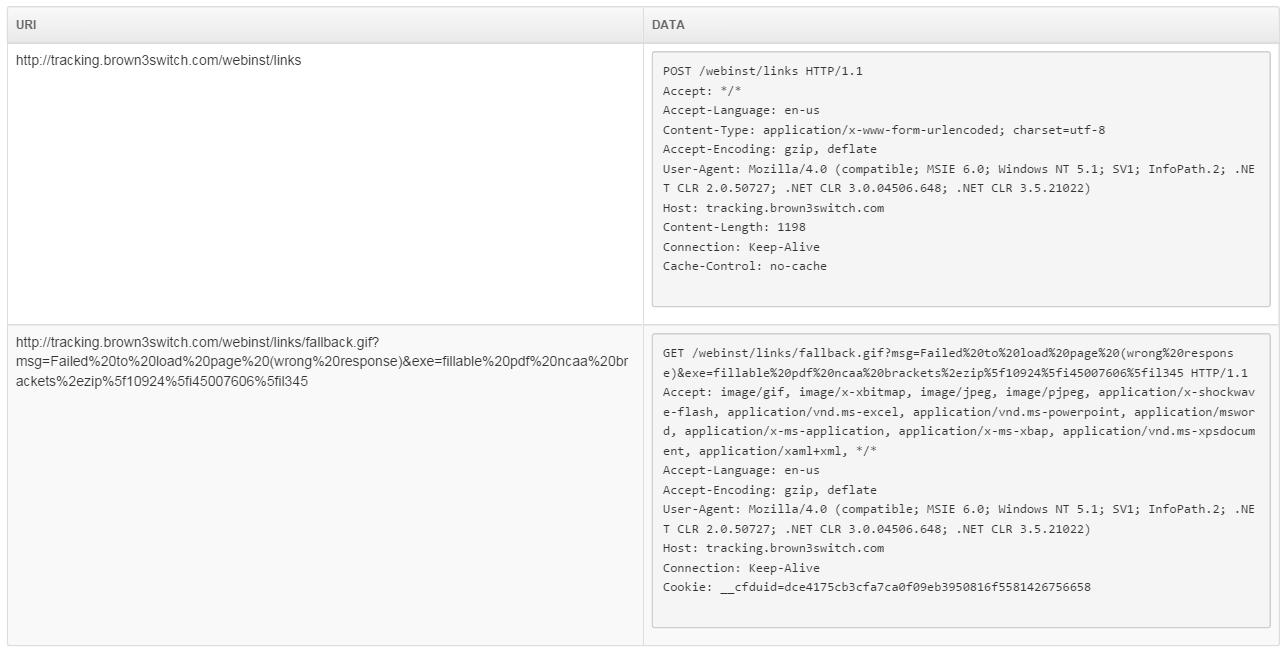 |
| HTTP Check-in activity includes POSTing system information. |
Fake .tk Blogs Generate Ad Revenue and Expose Users
Numerous ad-filled and auto-generated blogs have been popping up to take advantage of unwary search-engine users looking for bracket templates and related web-searches. While we have not seen any overtly malicious behavior on these sites, they represent a potential threat against the unwary searcher.
 |
 |
| Auto-generated blogs taking advantage of popular search terms. |
An interesting trend among these sites is the use of the free country TLD .tk. This isn't too surprising since the use of free domains is similar to the use of a dynamic DNS service, but the .tk TLD is slightly less conspicuous compared to no-ip.com or other common alternatives.
Streaming Scams Deliver Malware
Similar to sites offering bracket templates and insights on the match-ups, a large number of sites promising the ability to stream NCAA games have popped up to capture search traffic and generate ad-revenue. Unlike the SEO blogs, we have spotted -- and blocked -- malicious downloads related to tournament streams.
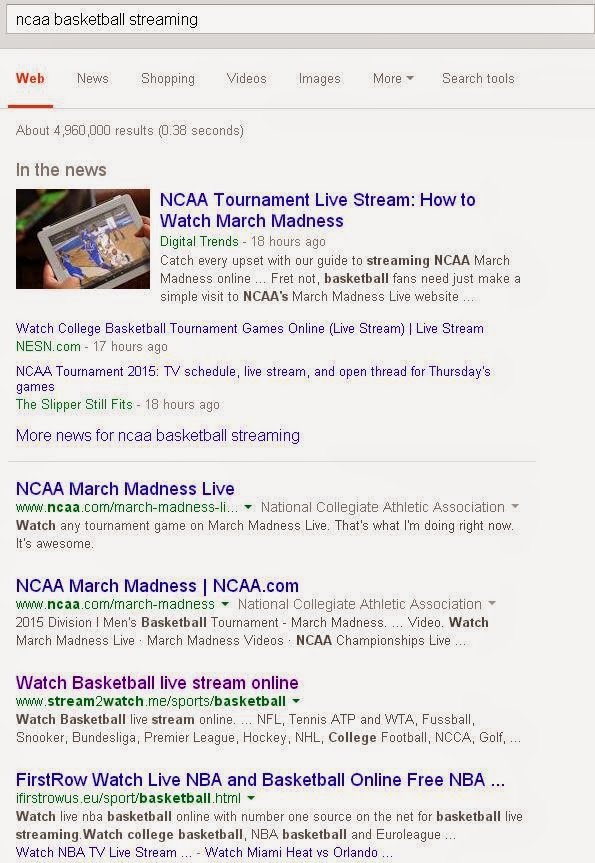 |
| Numerous scam sites are found among the top Google hits. |
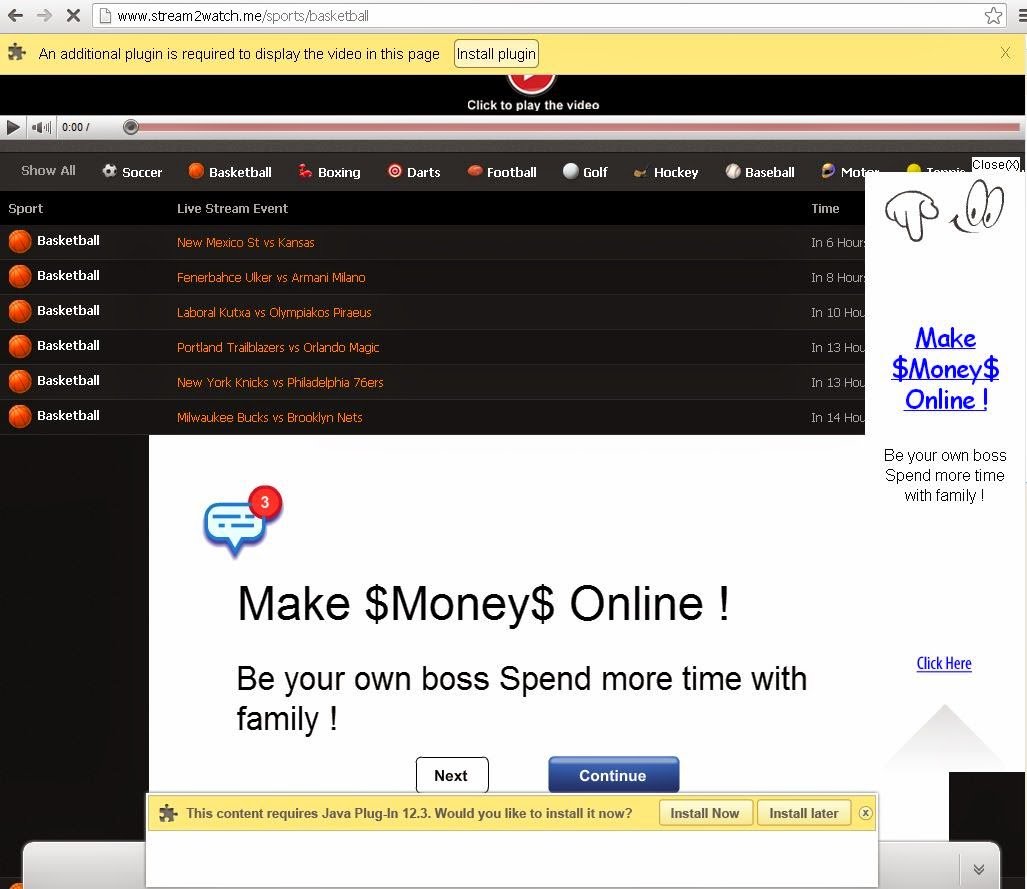 |
| Fake streaming site is filled with ads and fake plug-in install prompts. |
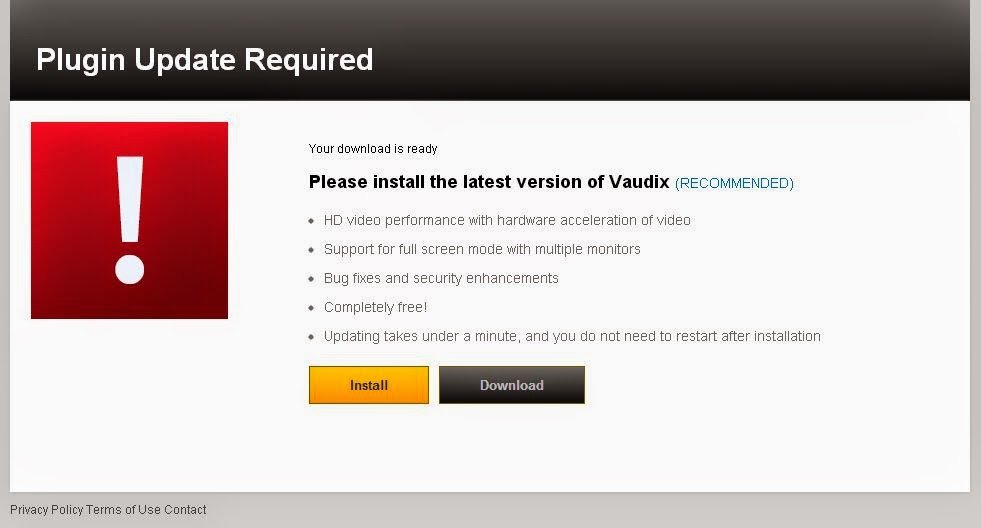 |
| Download page for fake plug-in emulates Adobe look and feel. |
Although this binary does not initially appear as sophisticated as the fake-bracket sample above, it downloads two supplemental encrypted files, one large binary blob and one base-64 encoded text file. Further analysis is needed to enumerate all functionality, but the malware can be observed collecting system information and sending it to a remote server.
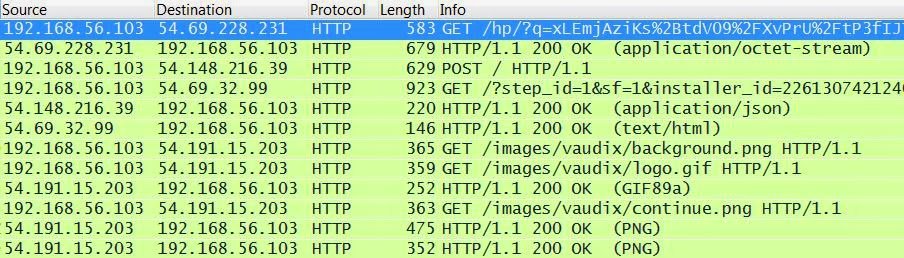 |
| Post-infection activity downloads another binary and POSTs system information. |
It should be noted that the NCAA has put tight restrictions on the streaming of the tournament, and apart from the first round, streaming the games requires a pay-TV subscription.
Conclusion
All of these examples should highlight the diversity of threats that latch on to the popularity of March Madness. We would like to advise the readers to exercise caution when doing searches or clicking on links related to March Madness.
Zscaler ThreatLabZ has deployed multiple layers of protection against these scams, safeguarding the users even when they are tricked into clicking a nefarious link.






