Introduction
Ransomware has evolved immensely over the past few years, with CryptoLocker being the ground breaking strain reaping huge profits for cybercriminals. According to a
report in December 2013, the CryptoLocker malware authors collected 27 million USD worth of bitcoins from their victims over a period of 3 months. Looking at the success enjoyed by the CryptoLocker strain, it's not surprising that many new copy cat variants including CryptoWall emerged in the wild starting in late 2013.
CryptoLocker suffered a major setback and the number of infections were reduced to nearly zero post
Operation Tovar. This gave way to a worthy successor in CryptoWall, which has since evolved into one of the nastiest and most successful strains of Ransomware in the wild today.
The following are some of the notable features responsible for the success enjoyed by CryptoLocker and CryptoWall variants:
- Asymmetric (public-key) encryption to encrypt user documents, making recovery infeasible
- Holding user files hostage with a timer that increases the ransom amount over time
- Ransom collected in bitcoins or as pre-paid cash vouchers
- Usage of anonymizing networks like Tor & i2p
Recent 'crypt4' campaign - CryptoWall 3.0
CryptoWall has been known to arrive via spammed e-mail attachments, exploit kits and drive-by downloads. Recently, we started seeing a new campaign involving multiple signed CryptoWall 3.0 samples in our Cloud Sandboxes being downloaded from a popular file hosting service, MediaFire.
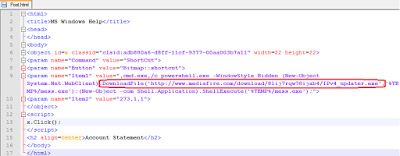
A quick Open Source Intelligence (OSINT), search lead us to this e-mail campaign where the attachment contains a Microsoft Compiled HTML help (CHM) file that leads to the download and execution of the the latest CryptoWall 3.0 variant hosted on MediaFire. The CHM file downloads and executes the CryptoWall executable from a hardcoded MediaFire location as seen in screenshot below:
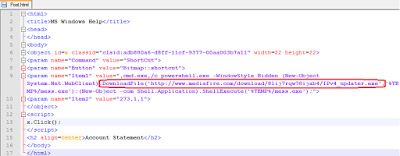 |
| Malicious CHM file - Extracted HTML code |
Some of the file names we have seen in this campaign:
- IPv6_updater.exe
- IPv4_updater.exe
- flashplayer17_ga_install.exe
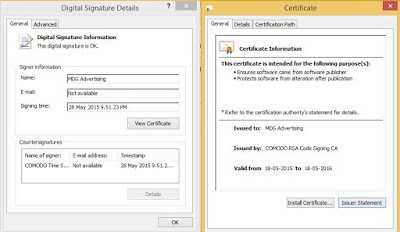
Analysis of the new variant The CryptoWall 3.0 payloads that we saw getting downloaded as part of this campaign were all signed by a valid certificate belonging to MDG Advertising as seen in the screenshot below:
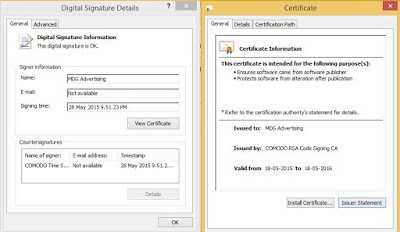 |
| Valid MDG Advertising certificate used to sign CryptoWall 3.0 |
|
The malware performs following file system changes to ensure persistence:
%USER%\APPDATA\7cc6cc79.exe [random alphanumeric name]
%USER%\Start Menu\Programs\Startup\7ddfa86e.exe [random alphanumeric name]
HKEY_USERS\Software\Microsoft\Windows\CurrentVersion\Run dd574bd = "%USER%\APPDATA\7cc6cc79.exe"
It also deletes the original copy of itself.
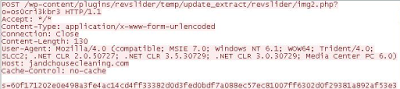
The malware then attempts to connect to the Command & Control (C&C) server to report the infection via a POST request as seen below:
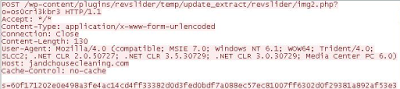 |
| C&C communication - Register infection |
It uses RC4 encryption for the data being sent in the POST request. The original data is of the format
{1|crypt4|UniqueMD5Hash|2|1|2|PublicIP}
- "crypt4" string represents the Campaign ID
- "UniqueMD5Hash" is calculated from Computer Name, Volume Serial Number, Processor & OS information
The RC4 key is generated by doing a simple alpha-numeric sort on a string stored inside the binary as seen in the screenshot below. The unsorted RC4 key is also sent as part of the POST request.
 |
| RC4 Key encrypted POST request to C&C server |
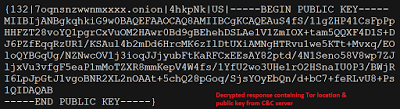
The malware then performs another POST request and in response it gets RC4 encrypted Tor domain & public key to use for encrypting the victim files. The Tor domain is leveraged for the decryption instruction. Screenshots below, show the original communication & decrypted response:
 |
| C&C communication - Requesting Public Key |
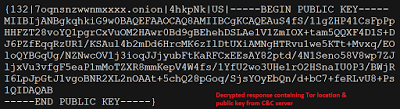 |
| C&C communication - Decrypted response with public key |
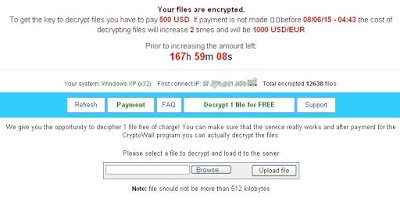
Upon successful encryption of the files on the victim machine using the public key, it reports back the number of files that were encrypted to the C&C server. The information collected by the C&C server is leveraged to present a more personalized decryption instruction page that includes user's operating system, public IP address, and the number of files encrypted as seen below.
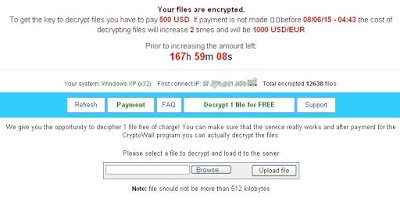 |
| Personalized ransom payment page |
The ransom amount requested in our case was $500 USD and to prove authenticity, the malware authors also offer the victim a "Decrypt 1 file for FREE" option, which is limited to a 512 kilobyte file.
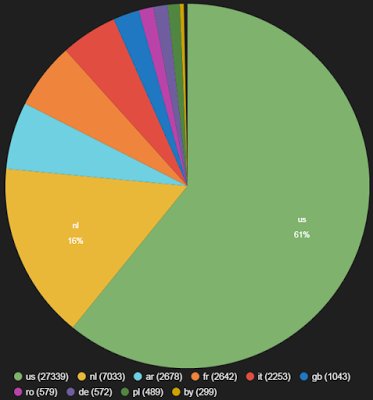
Below is the geo distribution of the CryptoWall C&C servers we oberved in the past week:
 |
| CryptoWall C&C servers |
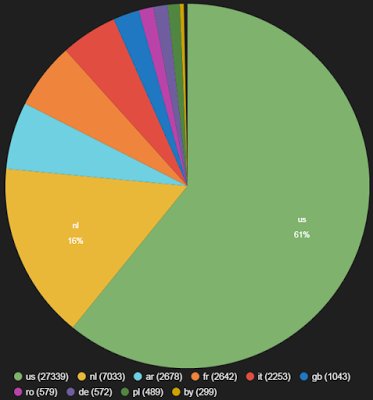 |
| CryptoWall C&C country distribution |
Compromised WordPress sites used for C&C communication
We are also seeing an increase in the number of compromised WordPress sites being used for CryptoWall C&C communication. Below are some of the locations where the malicious scripts are being hosted on these servers:
- /wp-content/plugins/revslider/temp/update_extract/
- /wp-content/uploads/wpallimport/uploads/
- /wp-content/themes/pptitan/
You can get full list of the Compromised WordPress sites that we have oberved in past one week
here.
Conclusion
CryptoWall remains a potent threat to enterprises and individual users alike. Traditional AntiVirus applications continue to struggle against this nasty strain of ransomware, as once the infection is successful, there is very little AV vendors can do, even by adding signatures reactively. A hybrid and multi-layered security approach is required to counter this threat.
Taking regular backup remains the most effective counter measure against ransomware.
Deepen Desai & Avinash Kumar