Everyone is excited about the football World Cup and apparently so are those peddling adware. Earlier we discussed some of the more aggressive Android advertising SDKs integrated apps flagged by AV vendors as Adware - Google Play vs AV vendors. We recently came across a particularly aggregious adware app promoting World Cup news.
App: Brazil 2014 World Cup
List of suspicious methods identified via static analysis:
- getMACAddress
- getLine1Number
- getsms
- getLongitude
- getLatitude
- getImei
- getImsi
- getAndroidId
- getEmail
- getManufacturer
- getOsVersion
- getNetworkconnectiontime
Let see how it harvests all information.
 |
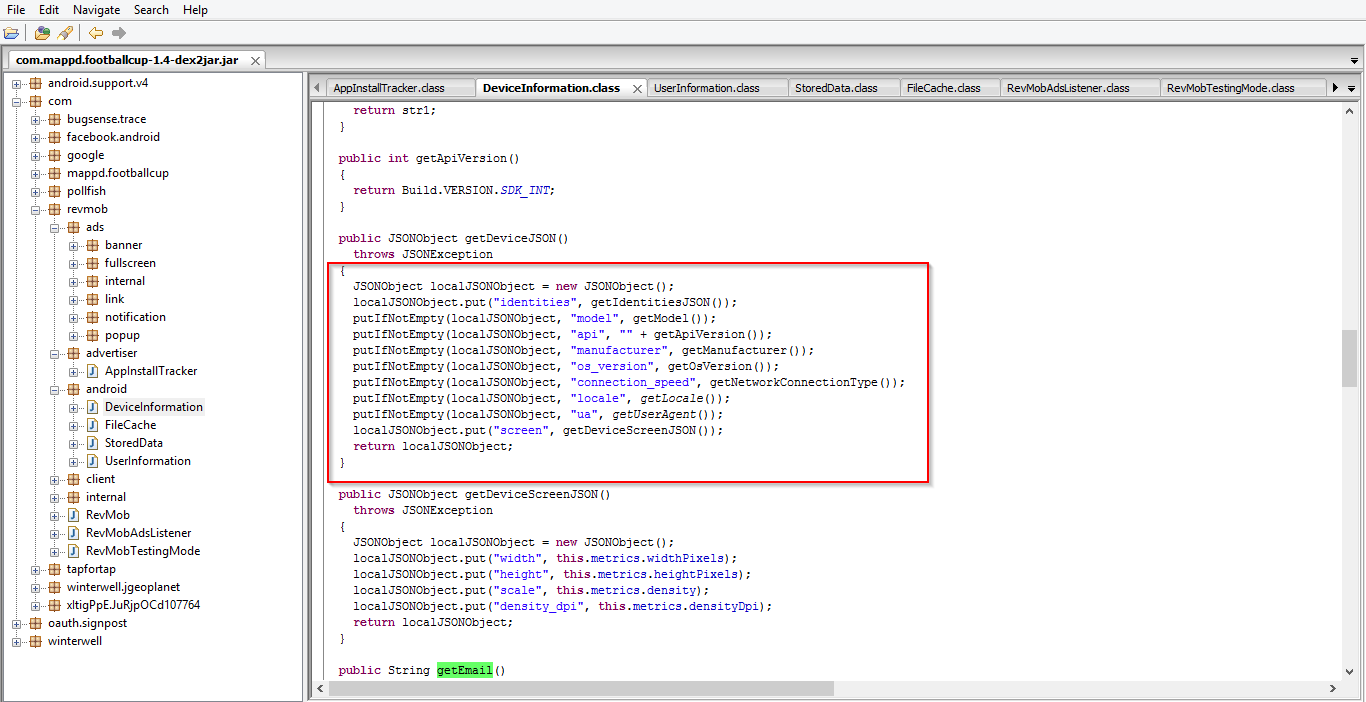
| Device information |
This app contains the Airpush and Revmob advertising SDKs. From the screenshot above, you can see the application harvesting the device MAC address (something Apple has cracked down on), mobile ID, Android ID and serial numbers. Adware harvests such information for tracking users as this information allows for tracking the user’s device across applications using the same SDKs.
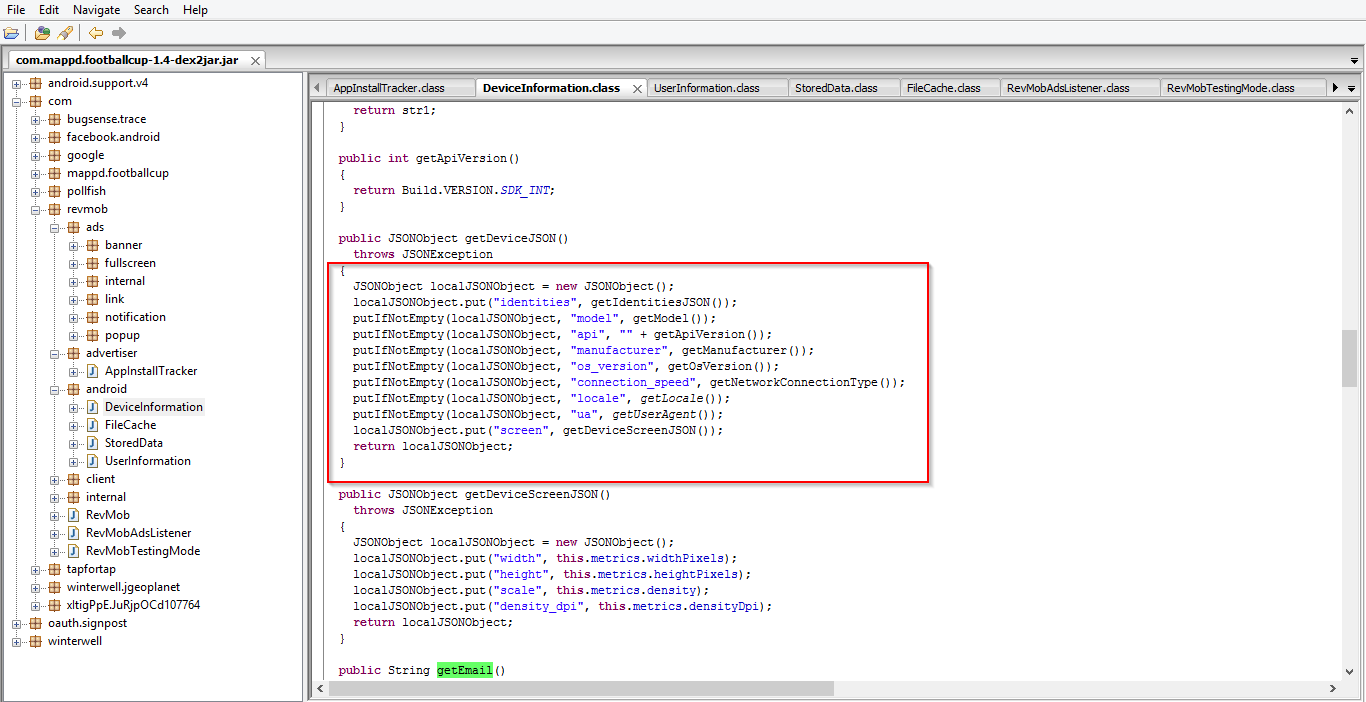 |
| Device information |
Above, you can see the application harvesting device model information, the SDK API version, manufacturer details and the device OS version. This information can then be used by advertisers to build statistics about app usage.
 |
| Phone number |
In this screenshot, you can see the application also collecting the user's phone number. This is very sensitive information as such information can be used for phone based spamming and advertising campaigns.
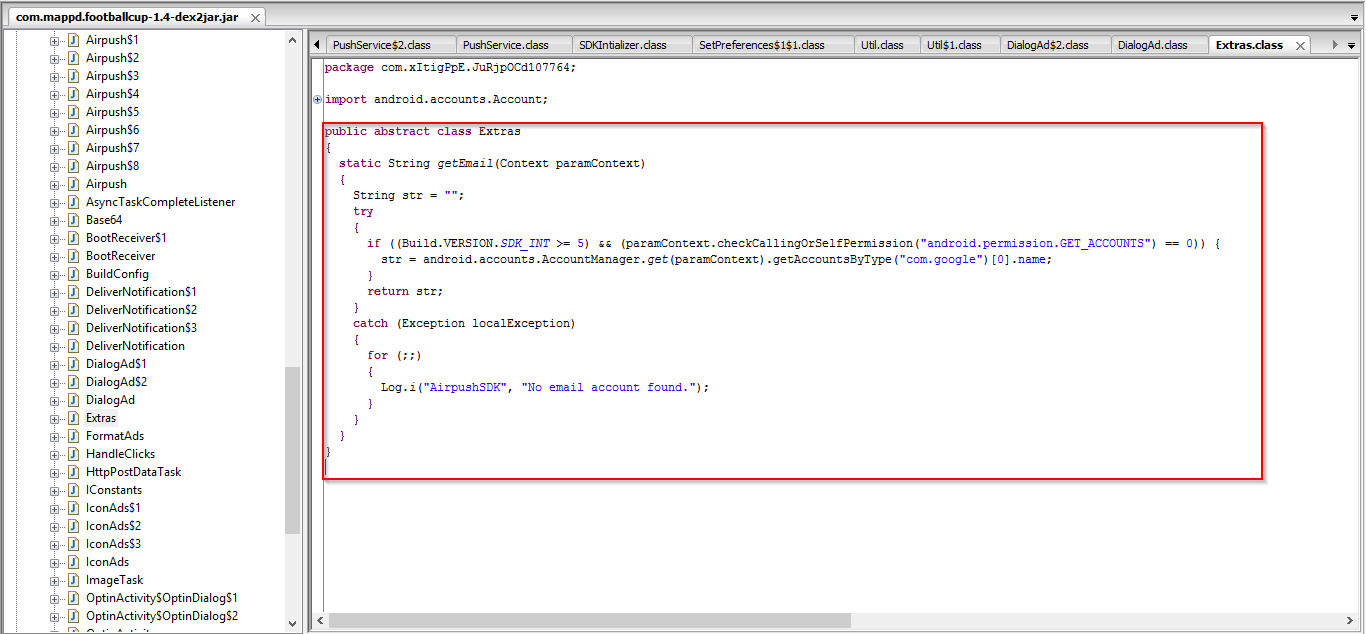 |
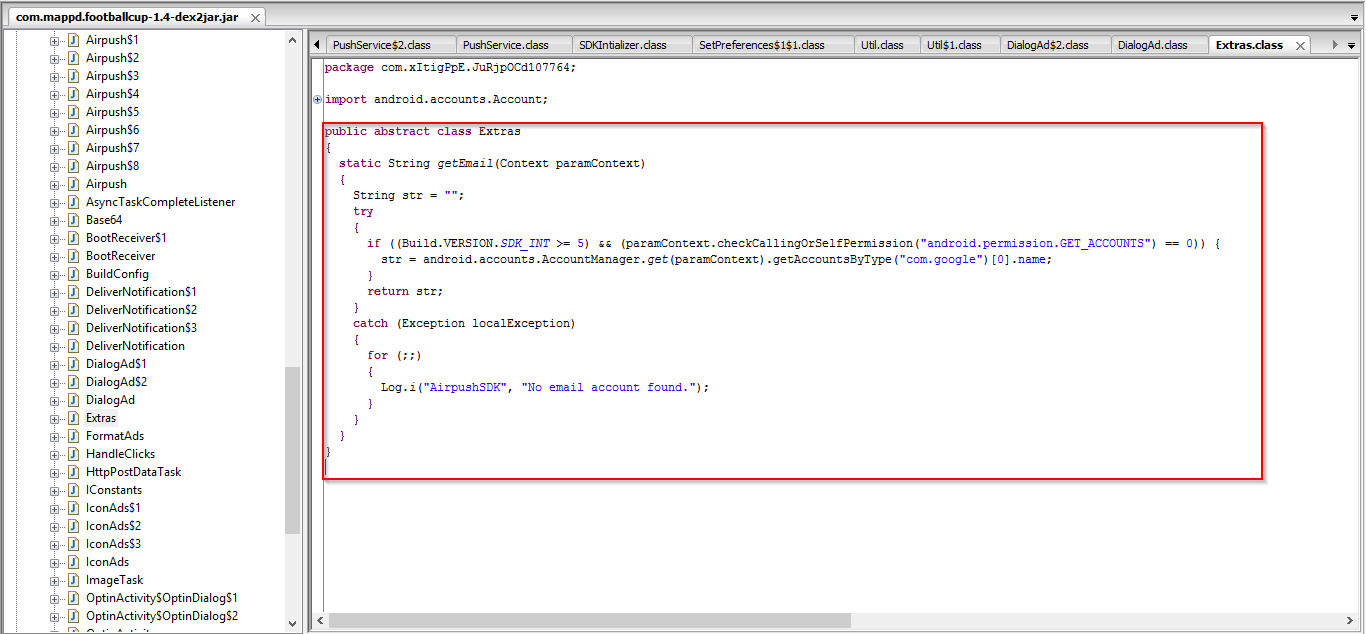
| Email |
This app also collects the user's email account, again, this too is likely used for spamming and advertising campaigns.
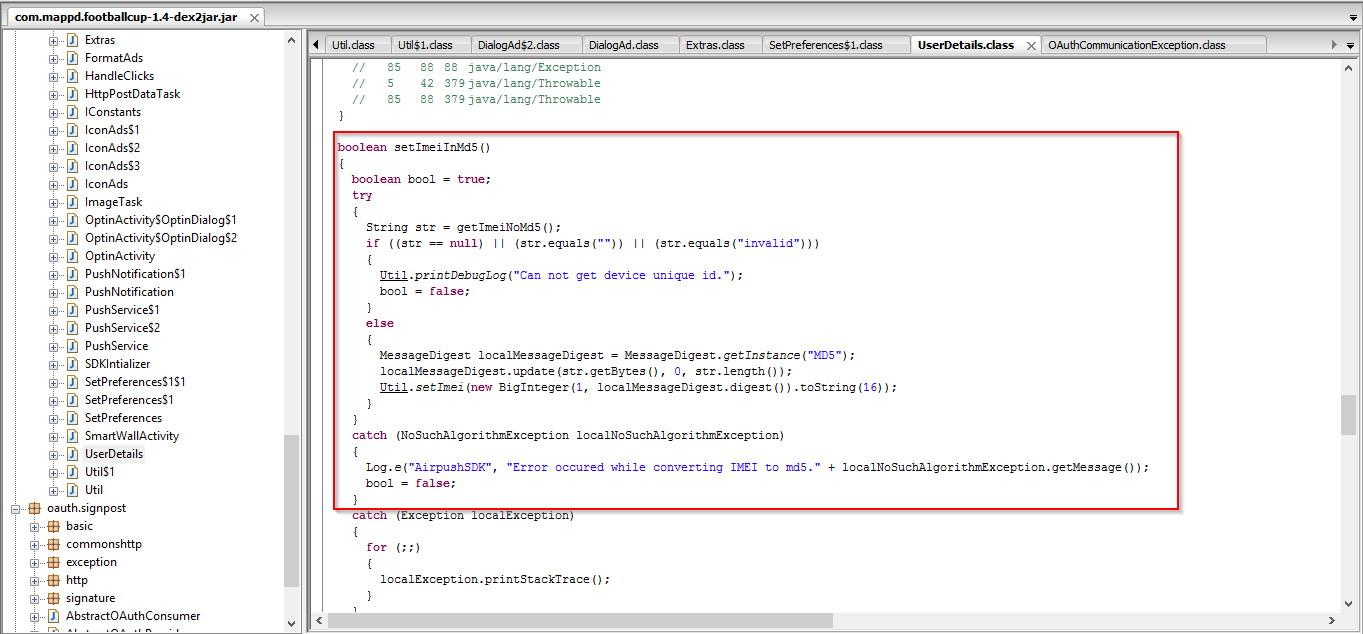 |
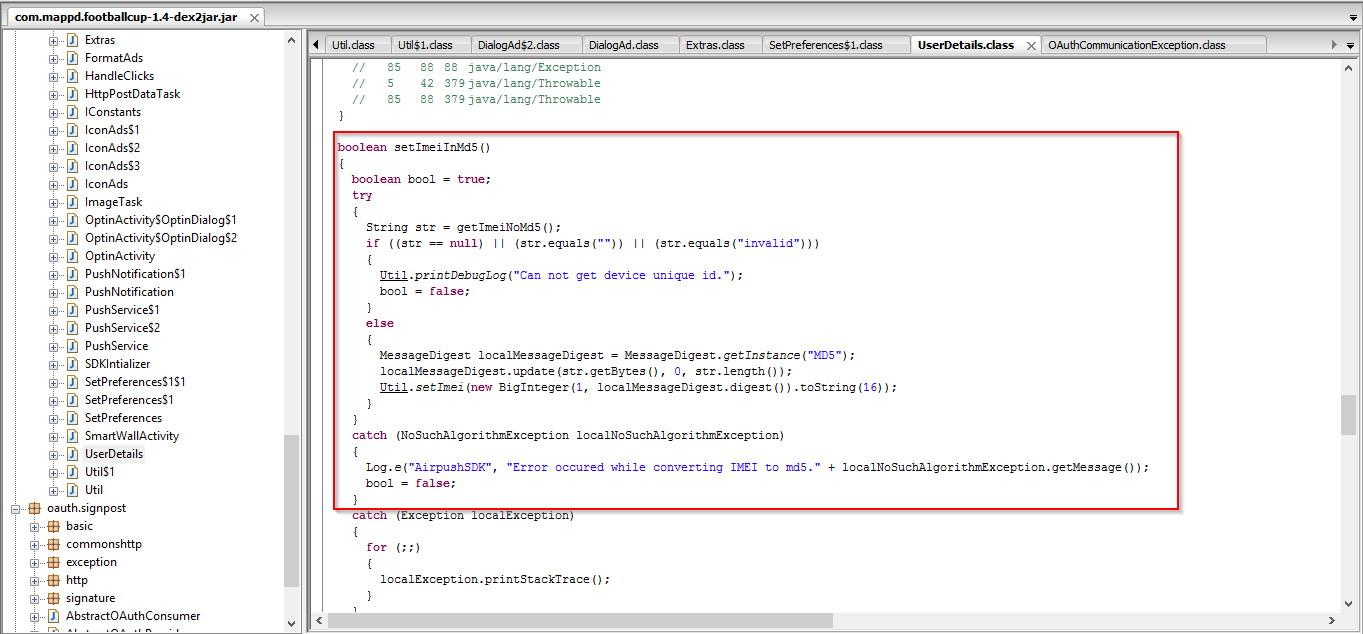
| IMEI |
Finally, the application collects the device IMEI number, another valuable identifier for tracking the same device across applications sharing the same advertising SDKs.
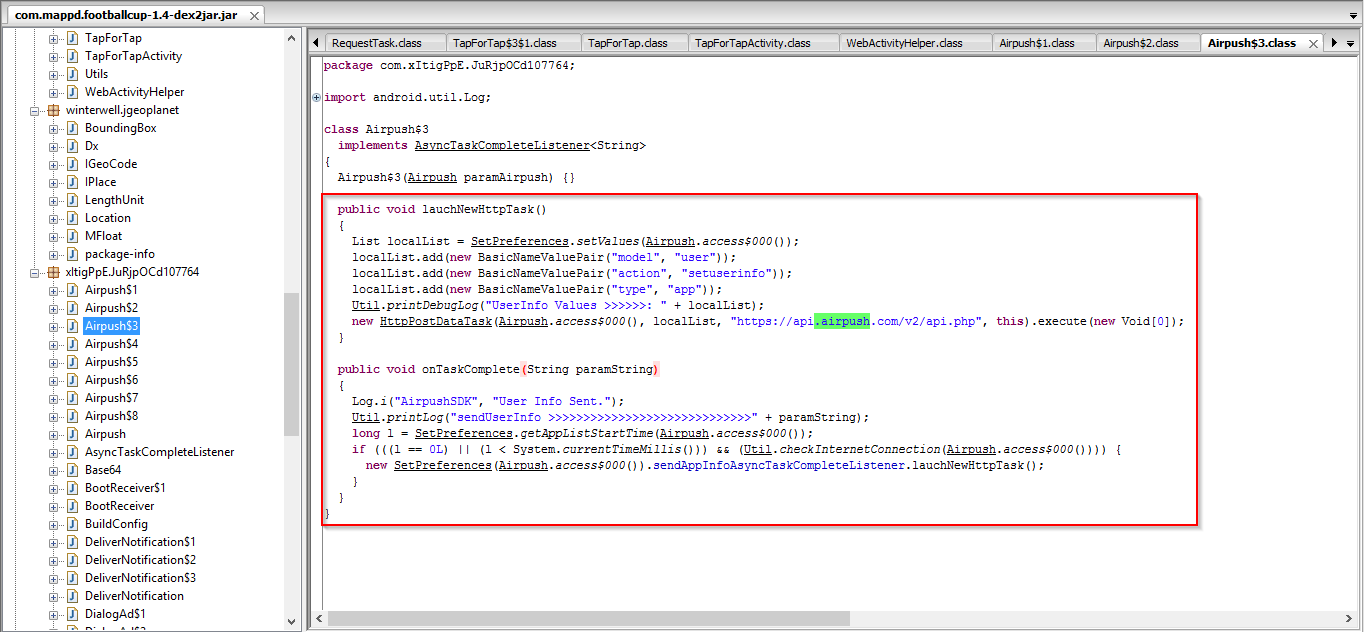 |
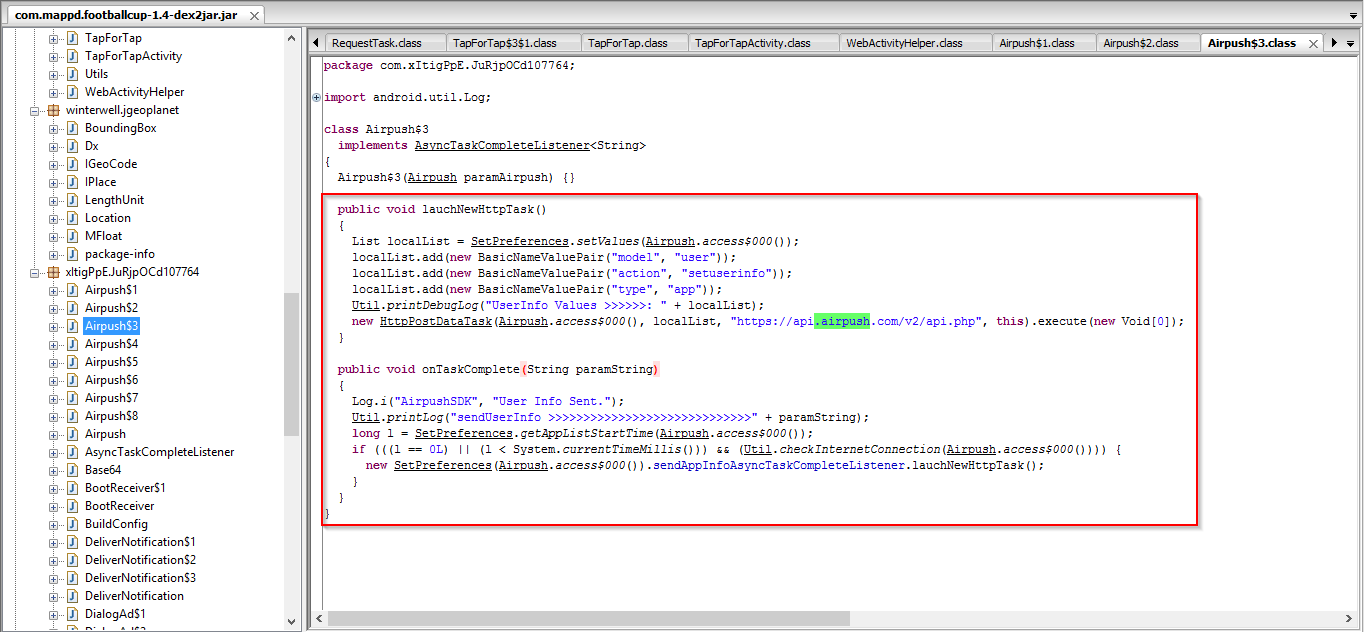
| Data sent |
You can also see all of the info being delivered to a third party.
 |
| Google play store developer policy |
As per the Google Developer policy, usage of MAC address and IMEI numbers is strictly prohibited. Still, apps are regularly permitted into the Google Play store and bypass Google's automated checks. This is an area where Apple is doing a better job of protecting end user privacy through both changes at the O/S level and via application reviews conducted prior to apps being included in the App Store. Apple would no longer permit an app with the level of data collection seen in this particular Android app. There is always confusion about content related to user privacy used by Android apps. In spite of clear guidelines from Google about data collection, developers are ignoring the rules and Google is not aggressively enforcing them.
Despite the aggressive data collection, this app is not malicious. Instead we (and many anti-virus vendors) consider this app an example of aggressive adware.
Stay safe while enjoying the World Cup.
-Viral.