Malicious Iframe attacks are not new but remain heavily used to carry out different attacks. HTML Iframe tags are used to embed content into the web page from a particular source, including sources external from the actual web site. Attackers are using zero pixel Iframes embed malicious content while to keeping content hidden from the user. People are often become victims from such attacks as it is easy to inject such malicious Iframes into a legitimate webpage by taking advantage of web application vulnerabilities like SQL injection.
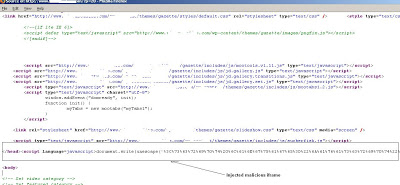
Let’s walk through live example where a malicious Iframe has been injected in the webpage. Here is the screenshot of one of the website injected by Iframe,
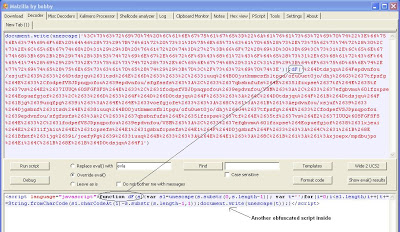
The above screenshot shows obfuscated JavaScript is present in the webpage after the closing html “” tag (prior to the actual page body). Malzilla a user friendly GUI tool was used to decode the obfuscated JavaScript. You can find good documentation on their website.
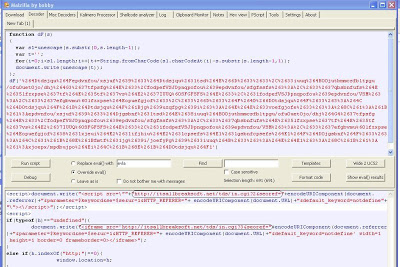
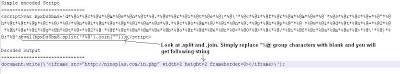
Interestingly, the JavaScript decodes into another obfuscated JavaScript. There is small function called dF() and a call to the “document.write()” function. Below is a screenshot of decoding this further:
After decoding a second time, the JavaScript is clear and readable. This hidden injected Iframe embeds this JavaScript within the page, and when someone visits the page the JavaScript is processed by the browser, transparent to the user. If you look at the height and width of the Iframe, it is set to 1 pixel, which will not be seen by the user.
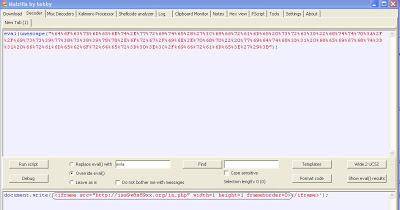
The above live example used multiple obfuscation techniques to hide the functionality of the malicious JavaScript. We have seen a number of websites infected with the same JavaScript code. The above example used “document.write()” function to write the malicious script into the page. Below is a decoded single obfuscated JavaScript example, which is still present on many websites:
Attackers are using simple to complex obfuscation techniques to encode their malicious script. Due to this, many Antivirus engines are unable to detect new injected Iframes. Here are the Virustotal results for the first example showing very low detection. Here is the third example of injected obfuscated script:
There are some important points to be considered here.
- In the past, it was common for attackers to inject their malicious Iframes at the bottom / end of the webpage. Attackers are now injecting malicious Iframes anywhere in the webpage.
- Many websites which were found to be infected in past months by malicious hidden Iframes appear to still be infected with them. Meaning most web site owners or hosting providers are not policing the content that they are serving on the web.
Start acting now. Be Safe while surfing!
Umesh