Scammers are up to mischief again by tricking users into clicking false webmail widgets. The core goal of any phishing attempt is to compromise the victim's access to a particular service. Usually this is done by posing as the service the attacker wants to hijack from the victim, and sending the username and password information back to the attacker. I've seen plenty phishing schemes in the past but what follows is the most blatant attempt at tricking users I've ever seen. Get ready...
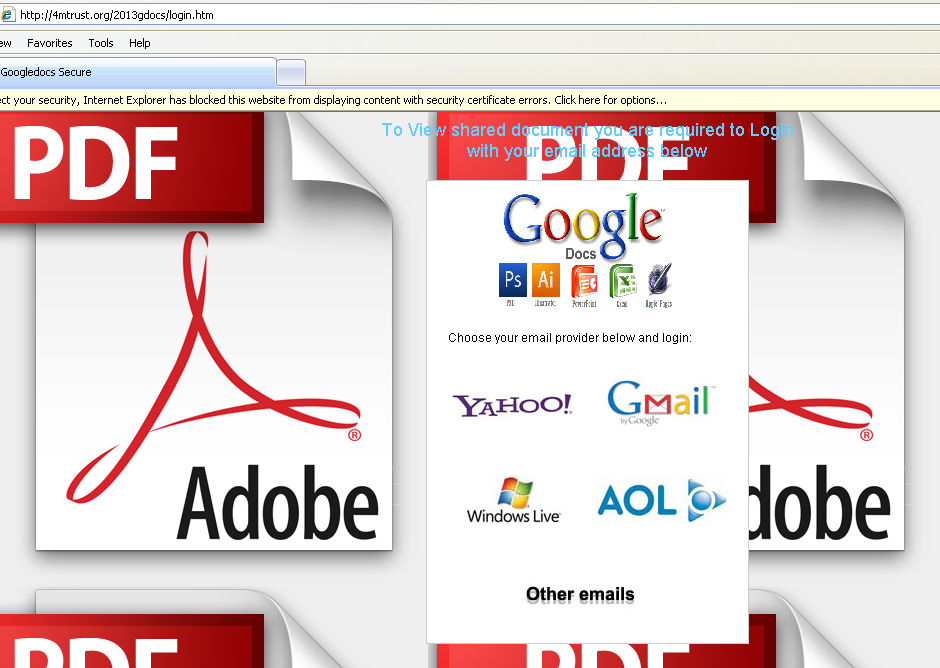
Nothing says legitimacy like what must have been Adobe Reader's Myspace page layout from 2004. Among the URL mentioned in the pic, other instances were seen as well to be related.
- hxxp://hasanalkhalaf.com/goglefiles-docs/2013gdocs/index.htm
- hxxp://bikecenteraracati.com.br/site/images/stories/ngdocs/login.html
- hxxp://4mtrust.org/2013gdocs/login.htm
- hxxp://kidneywisestp.org/kas_file/gdocs/
- hxxp://shareddocumentation.escuelajuanadeasbaje.edu.mx/
- hxxp://www.regnodellegno.it/tmp/sfile/googledocs/index.html
- hxxp://www.sgp.geodezja.org.pl/warszawa/images/stories/r/doc/file.index.htm
- hxxp://maso2.cl/wp-n/index.htm
- hxxp://www.chuchuguazastyle.com/lord/vhyvyvvyvyvy/
- hxxp://atcproject.ru/plugins/user/2013/2013googledocs/index.htm
- hxxp://www.myhawkslanding.com/site/plugins/doc/file.index.htm
- hxxp://ideid.in/olaat/gdocs/
- hxxp://casasnogeres.com/googledocs/googledrive/google/index.htm
- hxxp://cr-magazin.ch/cach/googledocss/googledocss/sss/
- hxxp://www.studiobanel.com/en/wp-admin/googledocfileap/
- hxxp://www.colerainezomba.org.uk/phpthumb/gdocs/index.htm
- hxxp://www.atlasfernsehdienst.de/joomla/delonghi-kundendienst-muenchen.de/components/com_user/ngdocs/login.html
If you happened to click through one of these links to "Log In" with your username and password, this is what you didn't seen in the background.
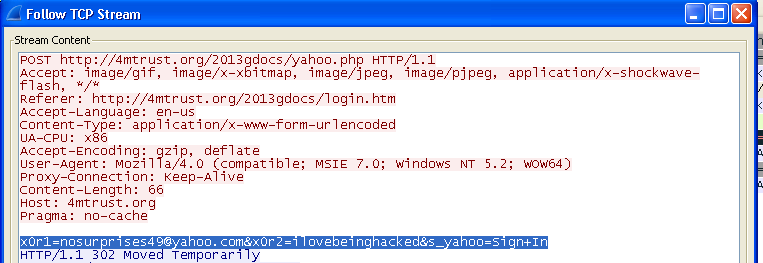 |
| Whoops |
Afterwards, the victim will find that whatever option they chose will land them at Google's HomePage. In the tested instance seen above, it was observed that the attacking site was hosted in India.
Mind your Clicks.