Overview
The only deterministic detection in your security stack
Zscaler Deception plants realistics decoys, lures and breadcrumbs across every attack surface in your environment so that any adversary—human or agentic—triggers an immediate alert your team can act on, with no correlation and investigation delays.
Stop lateral movement
with decoys deployed across every surface that attackers probe
Catch autonomous agentic attacks
that iterate instantly and run parallel paths before they can fully execute their playbook
Enable preemptive defense
by catching attackers before they can complete their objectives—with high-confidence alerts that initiate automated, machine-speed response actions
The Problem
Your security stack was built for human-speed attackers
Tools like EDR, SIEM, and XDR were built for an era when attackers moved at conventional attack timelines, correlating events over hours or days before generating a high-confidence alert. Now, AI-powered attackers have eliminated that window. Operating at machine speed, they can complete full kill chains in minutes, finishing long before your correlation engine can raise an actionable alert.
Your existing detection tools rely on signatures and behavior baselining—neither of which apply to novel AI attacks—and provide only probabilistic signals that require investigation and create even more alerts for your SOC to triage.
Product Overview
Deterministic detection for the era of AI-powered attacks
As attackers use AI to compress attack timelines, probabilistic detection tools compound the problem—more alerts, more triage, less time to act. Zscaler Deception shifts the advantage back to the defender with deterministic alerts, allowing your team to respond right away without having to investigate.
As part of the cloud native Zscaler Zero Trust Exchange™ platform, Deception can rapidly and seamlessly deploy high-fidelity threat detection throughout your enterprise.
Shrink mean time to respond (MTTR)
Traditional detection buries response in triage. Deception alerts arrive pre-confirmed, with no correlation required and no investigation to open. Your team moves directly to their response playbook from the first signal.
Get high-fidelity signals without the noise
Stop the cycle of alert fatigue. Because no legitimate user has a reason to interact with a decoy, every alert is a confirmed threat indicator. Your SOC stops filtering noise and starts acting on intelligence.
Stay ahead of novel threats
Deception technology is attack-tool and vulnerability independent. It doesn’t need to know what the attacker is doing—only that they touched something they shouldn’t have.
Automate containment in real time
Pre-authorize response actions tied directly to deception alerts. When a decoy fires, Zscaler zero trust policies or third-party tooling can automatically limit or revoke access before a human analyst even sees a notification.
What the experts say
250+ CISOs agree: Deception Can’t Wait
The Cloud Security Alliance’s Mythos Readiness strategy briefing, backed by hundreds of the world’s top security leaders, classified deception as one of the top Priority Actions in building a Mythos-ready defense, mandating that organizations deploy deception within 90 days.
Read the blogBenefits
Provide certainty to your Agentic SOC and the analysts staffing it. Leave attackers with nowhere to turn.
Eliminate investigation overhead
Deception alerts aren’t anomalies—they are confirmed threats that require response. They give your team the confidence to automate containment without the triage delay that AI attackers exploit.
Protect every surface that attackers pursue
Deception decoys are deployed safely in your production environment across endpoints, cloud, applications, identity, and AI infrastructure.
Lead AI adversaries into a no-win scenario
Moving fast and systematically will result in a decoy hit. Slowing down to stay hidden means they lose their speed advantage. Probing the environment to avoid decoys will trigger them anyway.
Product Details
High-fidelity detection across every attack surface
KEY CAPABILITIES
Neutralize AI agents by turning their exhaustive exploration against them with decoys that trigger on autonomous behavior.
Use decoy chatbots, decoys LLM APIs, adaptive decoys, and decoy agents to detect attackers targeting GenAI infrastructure in your environment.
Use internet-facing decoys to detect pre-breach threats specifically targeting your organization.
Plant a minefield to protect your endpoints with decoy files, credentials, processes, and more.
Detect lateral movement in your cloud environments with decoy web and file servers, databases, and more.
Deploy decoy server systems that host services like SSH servers, databases, file shares, and more.
Detect enumeration activity and malicious access with fake users in Active Directory.
Extract insights from context-rich logs, and get automated forensics and root cause analysis in two clicks.
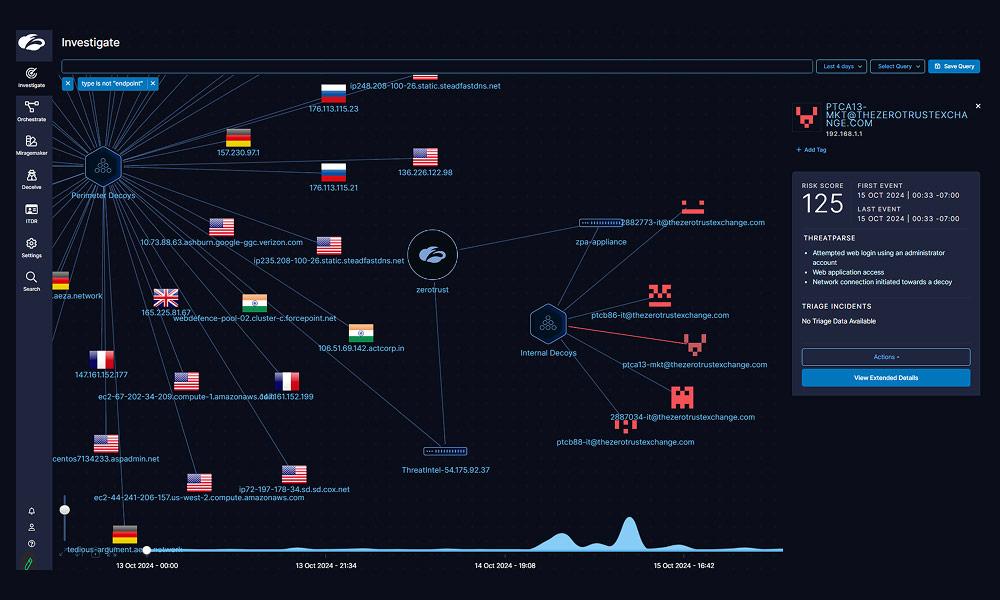
Product Video
Watch an agentic attack caught by Zscaler Deception
In this 5-minute video, see how multiple malicious AI agents work in parallel to perform reconnaissance, privilege escalation, lateral movement, and data exfiltration—with Deception detecting the entire attack in real-time.
Use Cases
Make your network a hostile environment for attackers
AI agents pursue every viable path with speed and parallelism. That thoroughness inevitably leads to a decoy interaction—an instant, confirmed alert.
Uncover prompt injection, data poisoning, and other severe attacks targeting your GenAI infrastructure and learning datasets.

Get early warning signals from perimeter decoys when advanced threat actors like ransomware operators or APT groups are performing pre-breach reconnaissance.

Deploy decoy passwords, cookies, sessions, bookmarks, and apps to detect compromised users when an attacker interacts with the deceptive environment.

Use application decoys and endpoint lures to divert and intercept attackers who are trying to move laterally in your environment.

Surround your high-value assets with decoys that detect and instantly block even the stealthiest and most sophisticated adversaries.

Detect ransomware at every stage of the attack life cycle with decoys in your network, endpoints, clouds, and Active Directory environments.

Integrate seamlessly with the Zscaler platform and third-party security operations tools like SIEM and SOAR to shut down active attackers with automated, rapid response.

Intercept attackers using stolen credentials to access decoy web apps that resemble vulnerable testbed applications and remote access services like VPNs.
The Zscaler Platform
The cybersecurity platform for the AI Age - built on Zero Trust to protect users, workloads, branches and devices through the world’s largest inline security cloud.

Data Security
Secure data everywhere, with comprehensive visibility and controls across all channels.
AI Security
Embrace AI with confidence using Zscaler AI Protect, a unified solution to secure AI at scale.
Agentic SecOps
Draw on insights from the world’s largest inline security cloud and third-party sources to assess risk and detect and contain breaches.
FAQ
FAQ
AI-orchestrated attacks operate by attempting to exploit every vulnerability at once and move through an environment across multiple paths simultaneously. This specific behavior makes Deception uniquely effective: the probability of an AI attacker hitting a decoy is nearly 100% because they attempt to exploit everything at once. When a decoy fires, that alert is a true positive, so you can auto-trigger containment—isolate the compromised host, block the IP, revoke the credential—at the speed of the attack.
Yes, Zscaler Deception can detect attacks like prompt injection, data poisoning, jailbreaking, adversarial suffixes, training data extraction, and more. Zscaler Deception supports creating decoy LLM chatbots and APIs to detect these attacks.
Zscaler Deception technology reimagines traditional honeypots by embedding deception directly into user environments across endpoints, network, Active Directory, cloud workloads, IoT/OT devices, and more, making traps indistinguishable from legitimate assets. Unlike static honeypots, Zscaler utilizes decoys and breadcrumbs, enabling attackers to unknowingly reveal themselves. This proactive, distributed strategy detects threats in real time and integrates seamlessly with the Zscaler Zero Trust Exchange platform.
Zscaler Deception is seamlessly woven into the Zscaler Zero Trust Exchange to dynamically distribute lightweight decoy assets across enterprise endpoints, networks, Active Directory, cloud workloads, and IoT/OT devices. These traps mirror authentic assets, making detection of malicious activity virtually instant. This embedded approach enables proactive threat detection while maintaining continuous validation for zero trust. Zscaler Deception is also built into the Zscaler Client Connector endpoint agent and Zscaler Private Access to detect lateral movement from endpoints to applications.
Zscaler Deception is designed to uncover a diverse range of threats, including advanced persistent threats (APTs), pre-breach attacks, identity compromise, privilege escalation, lateral movement, insider threats, and ransomware. By luring attackers with decoys and lures, it identifies suspicious behavior at early stages, providing proactive protection against breaches and reducing dwell times significantly.