Transform at the speed of your business
50%
70%
85%
The Problem
When it comes to M&A/D, IT is the key
The numbers don't lie—IT can make or break a merger, acquisition, or divestiture:

of deals experience technology integration issues
Bain & Company

of overall cost synergies are attributed to IT
Deloitte

increase in cyberattacks during M&A
McKinsey Insights
Solution Overview
Streamline M&A and divestitures with Zscaler
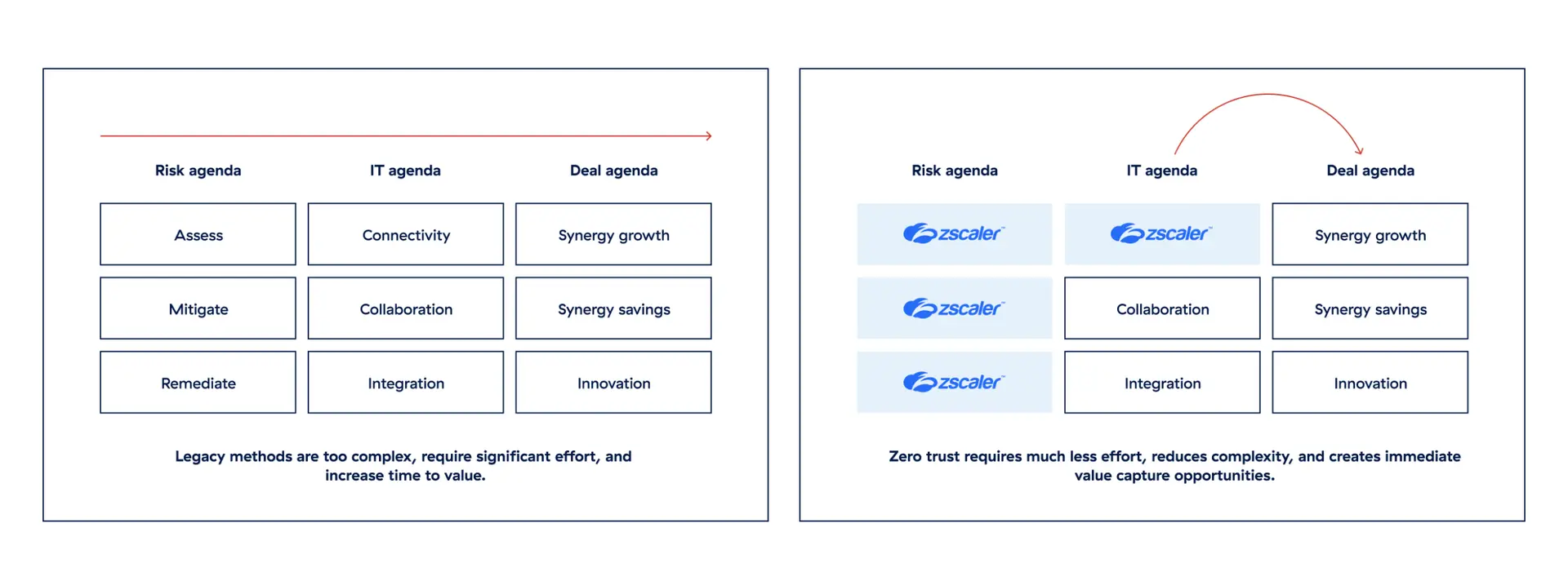
Securely accelerate M&A/D
Don’t let integration or separation complexities disrupt your competitive advantage. Modernize your M&A/D playbook with our cloud delivered, zero IT footprint zero trust approach for fast, cost-effective, and risk-managed transitions that help you maximize deal value.
Meet changing needs in changing times
As M&A/D activity continues to grow worldwide, countless complexities mean achieving a smooth transition—and fast time to value—is no easy feat. To minimize risks and keep everything running smoothly, you need the high-performance connectivity, consistent security, and great user experience you can only get from the world’s biggest security cloud.
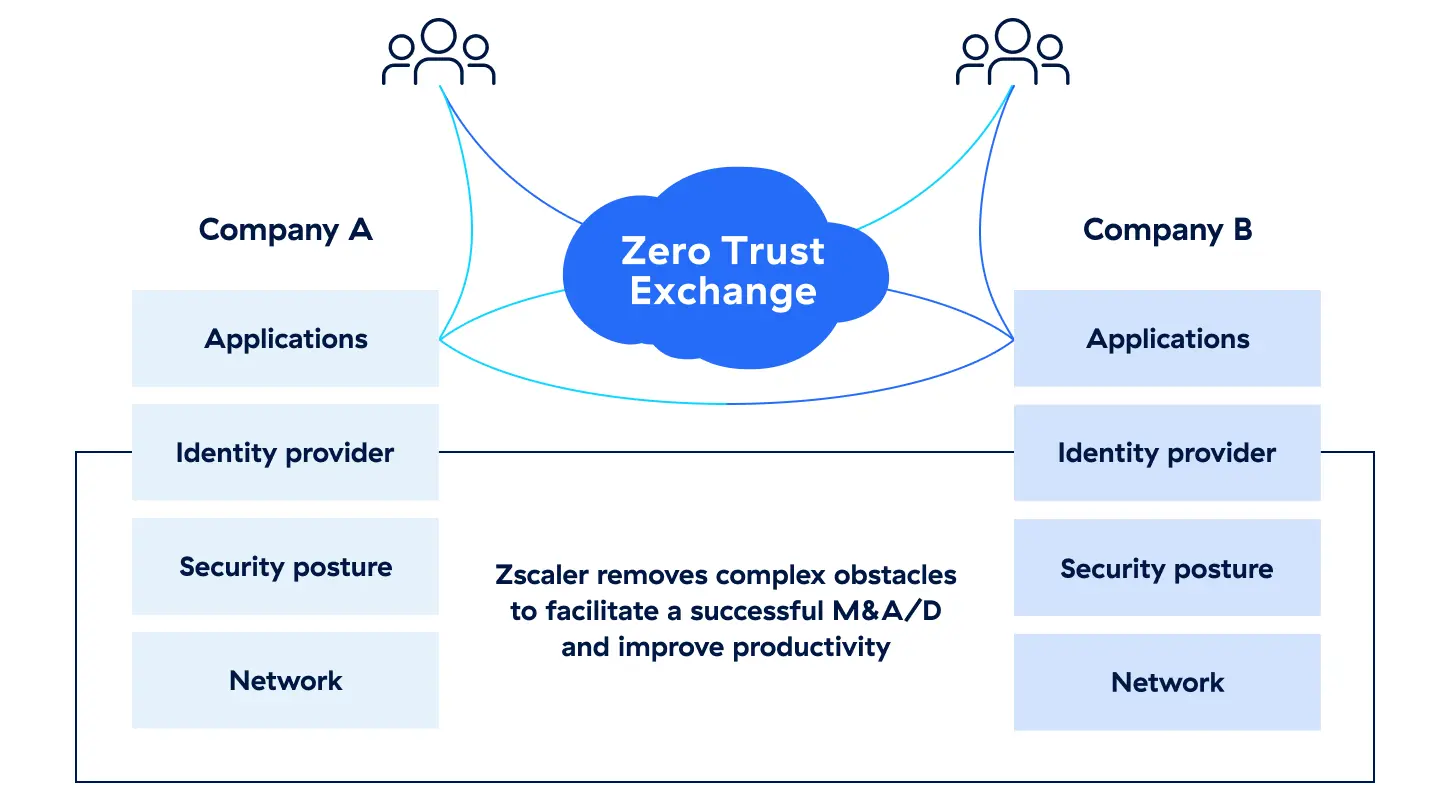
Nobody delivers it faster. With the Zscaler Zero Trust Exchange™, you’ll be able to streamline your IT M&A/D playbook and continue to manage, execute, and innovate your business strategy in half the time. Get to things like collaboration and innovation with ease.
Understand our approach to M&A
Benefits
Join 350+ organizations we’ve helped perform fast, secure IT integrations and divestitures with our unique zero trust approach
Accelerate time to value
Prioritize your deal value/synergies agenda and align business needs for maximum value capture.
Mitigate and control your risks
Keep your shields up, even when connecting assets and users between organizations.
Optimize costs and simplify transitions
Transform integration/separation projects into simple, predictable onboarding or offboarding processes.
Increase your business agility
Execute and close more deals, more quickly, with complete confidence that they’re secure.
Getting started








